Hong Kong Security Watch Report (Q4 2020)
HKCERT is pleased to bring to you the "Hong Kong Security Watch Report" for the forth quarter of 2020.
Highlight of Report
In 2020 Q4, there were 5,074 unique security events related to Hong Kong used for analysis in this report. Data were collected through IFAS1 with 10 sources of information2, and not collected from the incident reports received by HKCERT.
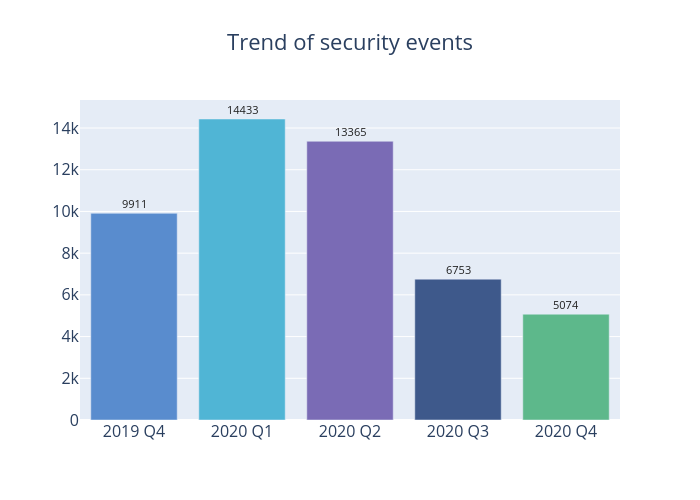
Figure 1 –Trend of security events
The total number of cyber security events in 2020 Q4 was 5,074, down by 25% from 2020 Q3 (6,753 cases). It had been on a downward trend for three consecutive quarters (Figure 1). Security events of all types had reported a decrease in this quarter. Malware hosting security events, in particular, had dropped from nearly 1,000 cases in 2020 Q3 to single digit in this quarter (Table 1).
Server related security events
Server related security events include malware hosting, phishing and defacement. Their trends and distributions are summarised below:
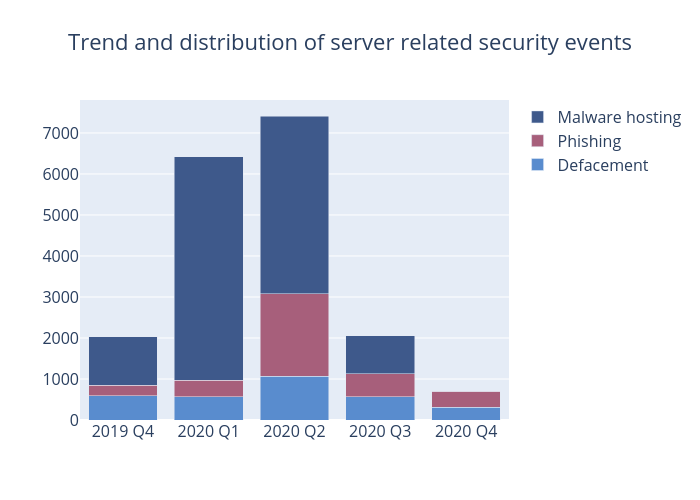
Figure 2 –Trend and distribution of server related security events
| Event Type | 2019 Q4 | 2020 Q1 | 2020 Q2 | 2020 Q3 | 2020 Q4 |
|---|---|---|---|---|---|
| Defacement | 591 | 572 | 1,062 | 571 | 305 |
| Phishing | 257 | 399 | 2,017 | 552 | 395 |
| Malware Hosting | 1,185 | 5,445 | 4,334 | 934 | 2 |
Table 1–Trend and distribution of server related security events
As shown in Table 1, while the number of phishing sites receded by over 28%, from 552 sites in 2020 Q3 to 395 sites in this quarter, the number of unique IP addresses involved had edged up to 149 (Figure 7). The unique URL/IP ratio shrank by 30% from 3.81 in 2020 Q3 to 2.65 in 2020 Q4 (Figure 8). Of these phishing sites, over half impersonated financial institutions and online shops. Besides, phishing sites with SSL certificates had been on the upward trend in recent years. The proportion of such sites has more than doubled from 27% in 2020 Q3 to over 56% in 2020 Q4. Checking for the SSL certificate had been one of the methods to identify a phishing website but the above-mentioned phenomenon had made the task more difficult. Also, HKCERT noted an automated phishing kit had been made available online recently, making it easier for hackers to develop high quality forged phishing content. HKCERT advises users to beware of web links of unknown sources. If suspicious, do not provide any personal information; and contact the related companies or organisations.
Compared with last quarter, both defacement events and unique IP addresses involved in such events decreased by 48% to 305 cases and 159 cases respectively (Figure 5). The unique URL/IP ratio is 1.92, similar to last quarter (Figure 6).
In this quarter, the number of malware hosting events dropped significantly, from last quarter’s 934 cases to this quarter’s two cases only. Since they came from two IP addresses (Figure 9), the unique URL/IP ratio was 1 (Figure 10). Both sites are inaccessible now, with one having already been taken down; and the other blocked by common browsers.
| HKCERT urges system and application administrators to protect the servers. |
|
Botnet related security events
Botnet related security events can be classified into two categories:
- Botnet Command and Control Centres (C&C) security events – involving a small number of powerful computers, mostly servers, which give commands to bots
- Botnet security events - involving a large number of computers, mostly personal computers which receive commands from C&Cs.
Botnet Command and Control Servers
The trend of Botnet C&C security events is summarised below:
There was no Botnet Command and Control Centers (C&C) security events in this quarter.
There was no Botnet Command and Control Centers (C&C) security events from 2019 Q4 to 2020 Q4.
Figure 3 –Trend of Botnet (C&Cs) related security events
The trend of botnet (bots) security events is summarised below:
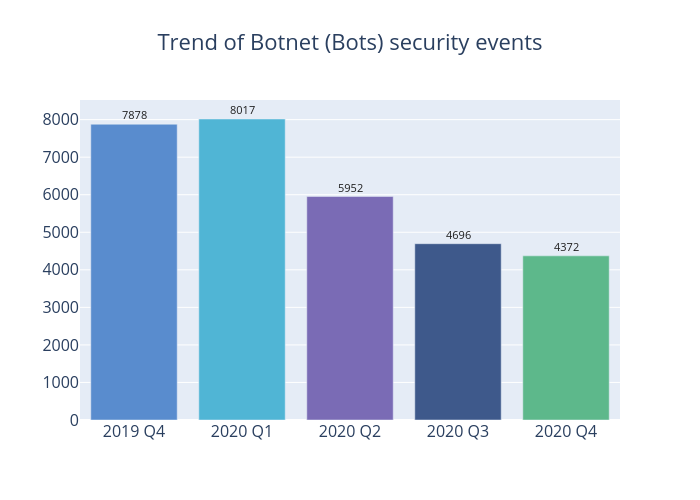
Figure 4 - Trend of Botnet (Bots) security events
The number of botnet (bots) event decreased by 7% to 4,372 in this quarter (Figure 4). Most botnet families have recorded a decrement. The top 5 botnet families are Mirai, WannaCry, Conficker, Avalanche and Virut, accounting for 91% of the total count.
Mirai botnet has a worm-like characteristic. It mainly targets unsecure IoT devices. Hackers had used those infected devices to launch large scale DDoS attacks against multiple organisations. It works by continuously scanning for IoT devices and attempting to intrude with default user name and password. Once succeeded, it took full control of the device. HKCERT reminds user to change the default password and close the TCP port 23 before using any IoT devices to enhance security. Since Mirai is memory-resident (volatile) only, if your device is infected, you can repeat the above mentioned steps, and then restart the infected device. Users can also visit HKCERT website to read the relevant guideline: https://www.hkcert.org/security-guideline/mirai-malware-cleanup-and-prevention.
| HKCERT urges users to protect computers so as not to become part of the botnets. |
|
| Users can use the HKCERT guideline to detect and clean up botnets |
|
Download Report
< Please click to download Hong Kong Security Watch Report >
1 IFAS Information Feed Analysis System is a HKCERT developed system that collects global security intelligence relating to Hong Kong for analysis.
2 Refer to Appendix 1 for the Sources of Information
3 Shodan is a search engine for Internet-connected devices: https://www.shodan.io/
Related Tags
Share with


