
HKCERT is pleased to bring to you the "Hong Kong Security Watch Report" for the third quarter of 2019.
Nowadays, many networked digital devices, such as computers, smartphones, tablets, are being compromised without the user's knowledge. The data on them may be mined and exposed every day, and even be used for various criminal activities.
The Hong Kong Security Watch Report aims to raise public awareness of the problem of compromised systems in Hong Kong, enabling them to make better decision in information security. The data in this quarterly report focuses on the activities of compromised systems in Hong Kong which suffer from, or have participated in various types of cyber attacks, including web defacement, phishing, malware hosting, botnet command and control centres (C&C) or bots. "Computers in Hong Kong'' refer to those whose network geolocation is Hong Kong, or the top level domain of their host name is ".hk'' or “.香港”.
Highlight of Report
In 2019 Q3, there were 26,320 unique security events related to Hong Kong used for analysis in this report. Data were collected through IFAS1 with 11 sources of information2, and not collected from the incident reports received by HKCERT.
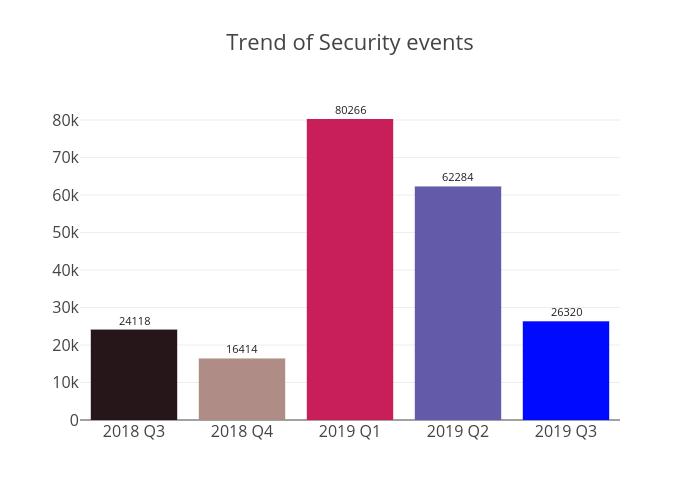
Figure 1 –Trend of security events
After reaching its peak in 2019 Q1, the total number of security events has decreased for two consecutive quarters. This was mainly due to a sharp drop in malware hosting events, which totalled 17,273 in 2019 Q3, down 65% from the previous quarter. Another significant decline was found in botnet events, falling by 39% in this quarter. On the other hand, defacement events have been doubled to 1,120.
Server related security events
Server related security events include malware hosting, phishing and defacement. Their trends and distributions are summarised below:
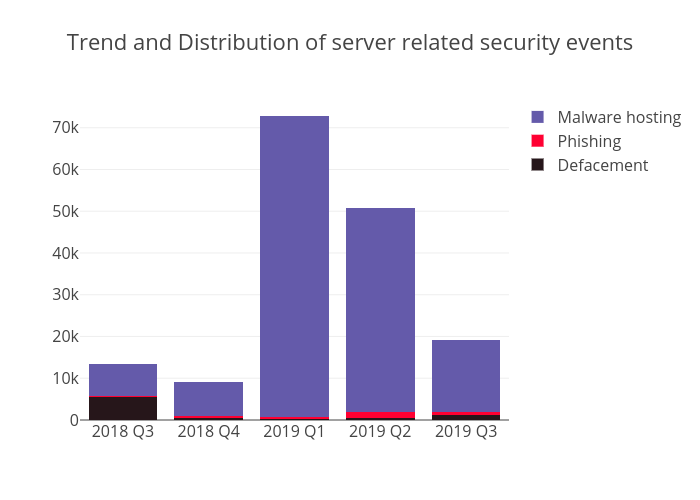 Figure 2 –Trend and distribution of server related security events
Figure 2 –Trend and distribution of server related security events
| Event Type | 2018 Q3 | 2018 Q4 | 2019 Q1 | 2019 Q2 | 2019 Q3 |
| Defacement | 5,439 | 590 | 318 | 532 | 1,120 |
| Phishing | 319 | 365 | 289 | 1,306 | 849 |
| Malware Hosting | 7,773 | 8,152 | 72,201 | 48,892 | 17,273 |
Table 1–Trend and distribution of server related security events
As shown in Table 1, there was a sharp rise in the number of defacement events from 532 in 2019 Q2 to 1,120 in 2019 Q3. While the number of defacement IP addresses increased by two-fold to 622, further probe revealed that 254 defaced websites were defaced in the same day - 23 September 2019, with the IP addresses of the defaced websites all under the same Class C IP address block. Therefore, HKCERT is of the opinion that these defacement events may probably come from the same mass defacement incident. To avoid becoming the victims of defacement incident, website owners should choose a secure and reliable web hosting service provider that is equipped with security functionalities and mechanism such as Web Application Firewall (WAF), Disaster Recovery (DR), etc.
Although phishing events fell by 35% to 849, they were still relatively high compared to previous quarters. Same as in 2019 Q2, Apple iCloud, and Amazon.com were the top two targeted brands of these phishing events. Based on HKCERT’s analysis, the top 2 IP addresses were 210.56.62.114 and 216.83.55.149, accounting for 83 events (10%) and 61 events (7.2%) respectively, both targeting Apple iCloud. In addition, the Microsoft Forms-based phishing attack
3 was found in these phishing events, where the attacker sent a phishing email to lure the victim to input their credentials into Microsoft Forms and submit to the attacker. So user should be aware of this type of phishing attack and to be alert of the authenticity of any online form asking for sensitive personal info (i.e. HKID number, credit card information, pin number, password and etc.) through online form whenever possible.
Malware hosting events continued to fall, down 65% from 2019 Q2. However, the number of involved malware hosting IP addresses only declined by less than a third, totalling 3,357; while the URL/IP ratio of Malware Hosting halved to 5.1.

| HKCERT urges system and application administrators to protect the servers. |
- patch server up-to-date to avoid the known vulnerabilities being exploited
- update web application and plugins to the latest version
- follow best practice on user account and password management
- implement validation check for user input and system output
- provide strong authentication e.g. two factor authentication, administrative control interface
- do not expose unnecessary services to the internet
|
Botnet related security events
Botnet related security events can be classified into two categories:
- Botnet Command and Control Centres (C&C) security events – involving a small number of powerful computers, mostly servers, which give commands to bots
- Botnet security events - involving a large number of computers, mostly personal computers which receive commands from C&Cs.
Botnet Command and Control Servers
The trend of botnet C&C security events is summarised below:
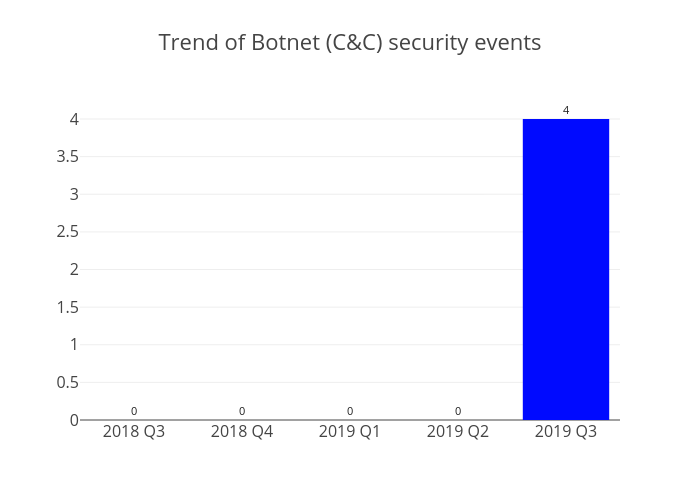 Figure 3 –Trend of Botnet (C&Cs) related security events
Figure 3 –Trend of Botnet (C&Cs) related security events
Command and Control Server events have reappeared for the first time since 2018 Q2, with 4 such events reported. All of them were identified as an IRC bot C&C server.
HKCERT encountered the discontinuation of feeds from two sources - (i)Abuse.ch: Zeus Tracker - C&Cs and (ii)Abuse.ch: Palevo Tracker - C&Cs. They had been removed from our analysis in this quarter.
Botnet Bots
The trend of botnet (bots) security events is summarised below:
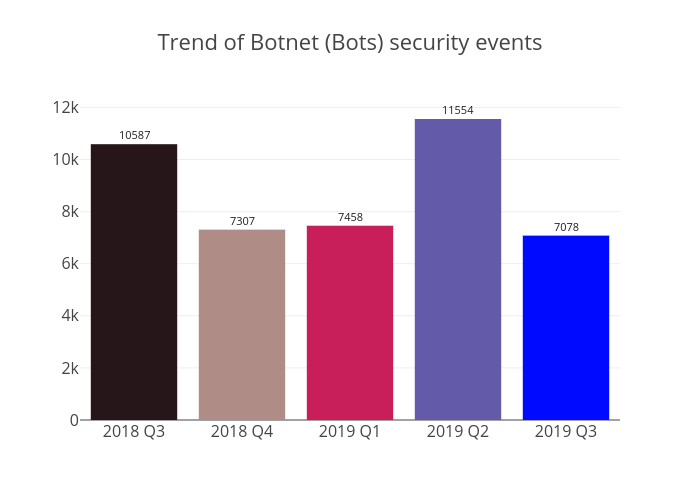 Figure 4 - Trend of Botnet (Bots) security events
Figure 4 - Trend of Botnet (Bots) security events
In 2019 Q3, the number of Botnet (bots) in Hong Kong network has dropped 39%. It was mainly caused by a dramatic plunge in Ramnit bots from 4,522 in 2019 Q2 to 49 in 2019 Q3. Mirai regained the top place of major Botnet families in Hong Kong network. The top 5 ranking of Botnet families was the same as from 2018 Q1 to 2019 Q1 (Mirai, WannaCry, Conficker, Virut, and Avalanche). Besides, HKCERT observed that the number of WannaCry events have gradually fallen to 697 in 2019 Q3, down 42% since 2018 Q4.

| HKCERT urges users to protect computers so as not to become part of the botnets. |
- patch their computers
- install a working copy of the security software and scan for malware on their machines
- set strong passwords to avoid credential based attack
- do not use Windows, media files and software that have no proper licenses
- do not use Windows and software that have no security updates
- do not open files from unreliable sources
|
HKCERT has been following up the security events received and proactively engaged local ISPs for the botnet cleanup since June 2013. Currently, botnet cleanup operations against major botnet family Avalanche, Pushdo, Citadel, Ramnit, ZeroAccess, GameOver Zeus, VPNFilter and Mirai are still ongoing.
HKCERT urges general users to join the cleanup acts, ensuring their computers are not being infected and controlled by malicious software, and protecting their personal data for a cleaner cyberspace.

| Users can use the HKCERT guideline to detect and clean up botnets |
|
Download Report
< Please click to download Hong Kong Security Watch Report >
1 IFAS Information Feed Analysis System is a HKCERT developed system that collects global security intelligence relating to Hong Kong for analysis.
2 Refer to Appendix 1 for the Sources of Information
3 Microsoft Adds Automatic Phishing Detection to Microsoft Forms
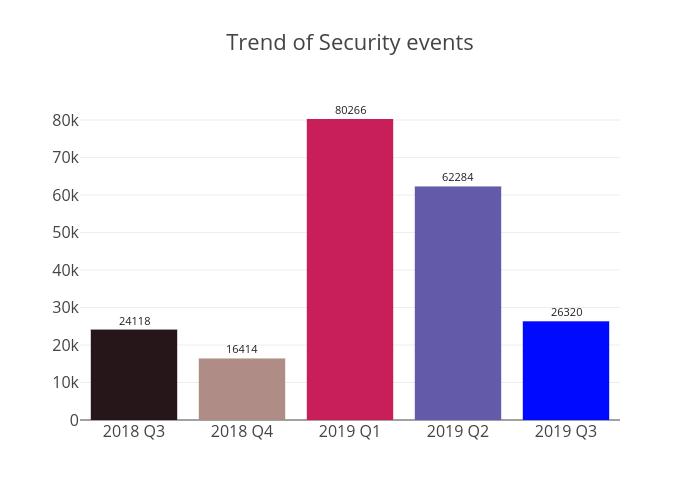
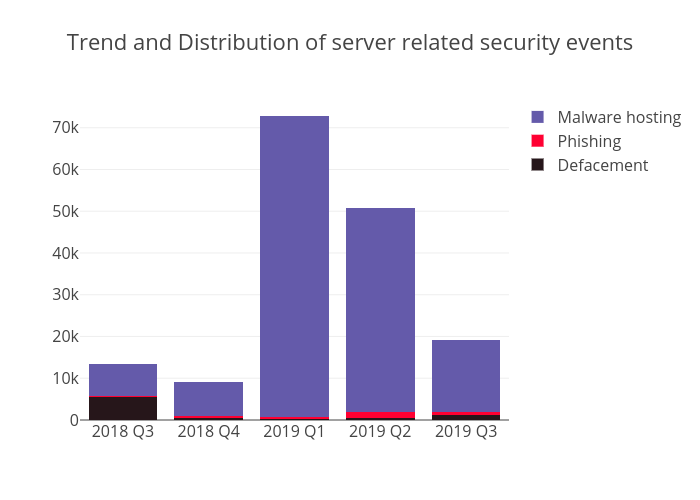 Figure 2 –Trend and distribution of server related security events
Figure 2 –Trend and distribution of server related security events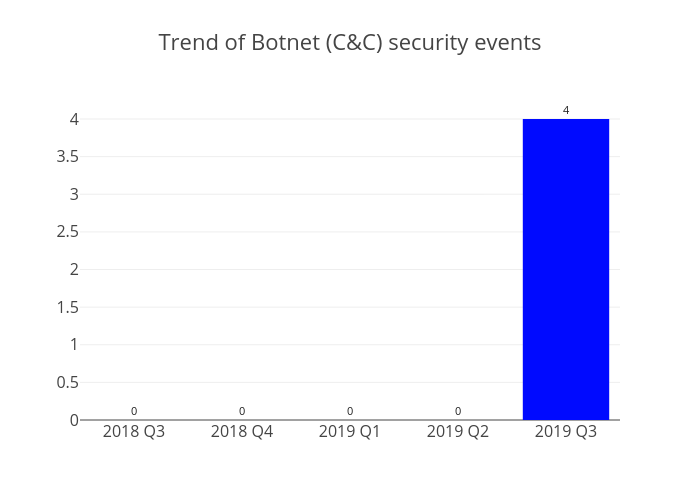 Figure 3 –Trend of Botnet (C&Cs) related security events
Figure 3 –Trend of Botnet (C&Cs) related security events 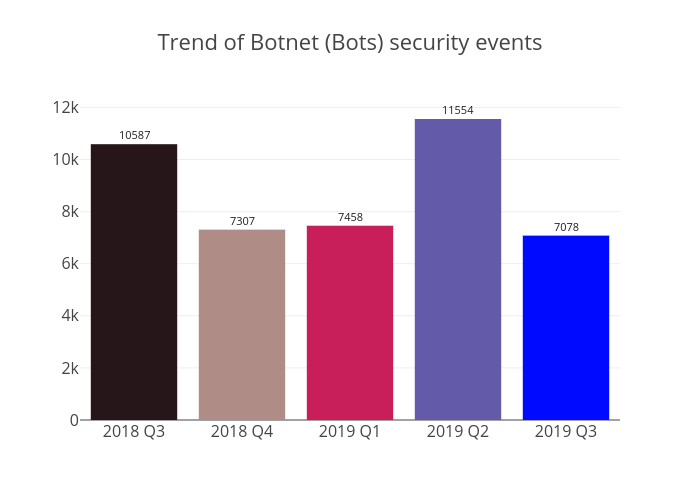 Figure 4 - Trend of Botnet (Bots) security events
Figure 4 - Trend of Botnet (Bots) security events

