Hong Kong Security Watch Report (Q2 2019)
HKCERT is pleased to bring to you the "Hong Kong Security Watch Report" for the second quarter of 2019.
Nowadays, many “invisible” compromised systems (computers and other devices) are being hacked and seized control without their owners’ knowledge. The data on these systems may be mined and exposed every day, and even used for various criminal activities.
The Hong Kong Security Watch Report aims to raise public awareness of the problem of compromised systems in Hong Kong, enabling them to make better decision in information security.
The data in this report is about the activities of compromised systems in Hong Kong which suffer from, or have participated in various types of cyber attacks, including web defacement, phishing, malware hosting, botnet command and control centres (C&C) or bots. “Computers in Hong Kong” refer to those whose network geolocation is Hong Kong, or the top level domain of their host name is “.hk” or “.香港”.
Highlight of Report
In 2019 Q2, there were 62,284 unique security events related to Hong Kong used for analysis in this report. Data is not collected from the incident reports received by HKCERT, which came from IFAS1 from 13 sources of information2.
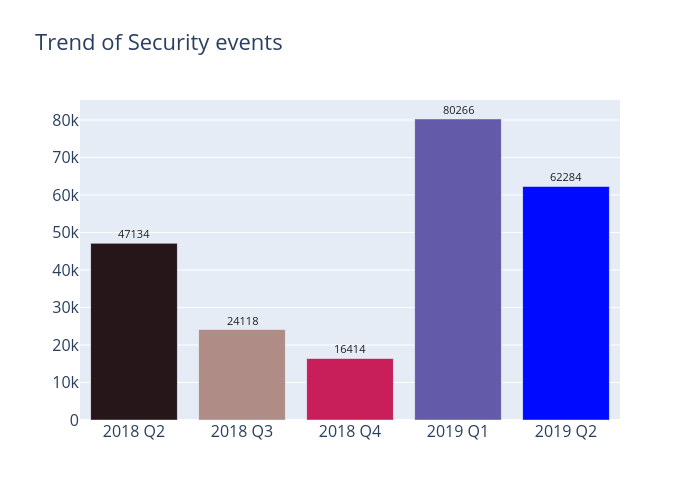
Figure 1 –Trend of security events
The total number of security events in 2019 Q2 (17,982 events) fell by 22% from the previous quarter. Although there was a notable decline in malware hosting events, other events had reported ascendant trends during this quarter. The most obvious increase was phishing events, which rose over three-fold. Meanwhile, defacement and botnet events had reported growths of 67% and 55% respectively. The total number of security events has remained relatively high in the first two quarters of 2019. As such, HKCERT will notify the affected operators to check and clean up their servers in August 2019.
Server related security events
Server related security events include malware hosting, phishing and defacement. Their trends and distributions are summarized below:
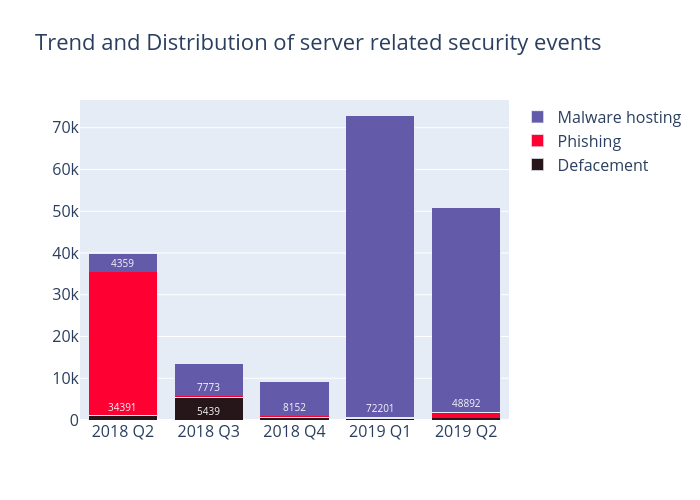 Figure 2 –Trend and distribution of server related security events
Figure 2 –Trend and distribution of server related security events
From the report for 2019 Q1, we have observed the emergence of malware hosting events from March 2019. Such events continued their presence in Q2. Although the number of malware hosting events has considerably reduced from 72,201 in Q1 to 48,892 in Q2, while the URL/IP ratio of malware hosting halved to 10 (see Figure 10), the number of involved malware hosting IP addresses rose by 33%, 4,851 in total. Therefore, it stated that the actual malware hosting trends did not show signs of decline. ASN AS38197 (Sun Network) hosted the most malware hosting URL, accounting for 36% of total events. HKCERT had notified the affected operators to check and clean up their servers in April 2019. We noted that 70% involved malware hosting IP addresses in Q1 were not found in Q2.
The number of phishing events, each involving a unique phishing URL, rose over three-fold from 289 in Q1 to 1,306 in Q2. It is worth noticing that over 40% of phishing events targeted apple.com and icloud.com, by adding them as subdomain to a legitimate domain name (for instance http://www.icloud.com.example.com), in order to mislead victim to believe that it belongs to that organisation, being the most common phishing method. At the same time, there has been a concurrent rise in the number of the involved phishing IP addresses to 302. The top IP address 103.65.182.5 accounted for 198 events (15%); followed by 103.65.182.89 which accounted for 151 events (12%); and both were registered under AS38197 (Sun Network).
For defacement events, there has been a marked overall increase from 318 in Q1 to 532 in Q2; while the involved defacement IP addresses slightly rose by 18% to 204. Top 5 IP addresses hosted accounted for 209 events (39%). Many of these defacement events could be attributed to attackers compromising those vulnerable servers which hosted multiple websites.
| HKCERT urges system and application administrators to protect the servers. |
|
Botnet related security events
Botnet related security events can be classified into two categories:
- Botnet Command and Control Centres (C&C) security events – involving small number of powerful computers, mostly servers, which give commands to bots
- Bots security events – involving large number of computers, mostly home computers, which receive commands from C&C.
Botnet Command and Control Servers
The trend of botnet C&C security events is summarized below:
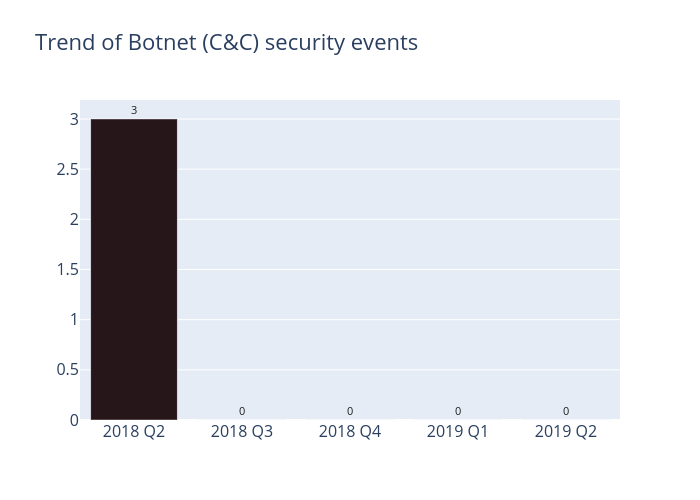 Figure 3 –Trend of Botnet (C&Cs) related security events
Figure 3 –Trend of Botnet (C&Cs) related security events
There was no Command and Control Server event in this quarter.
The trend of botnet (bots) security events is summarized below:
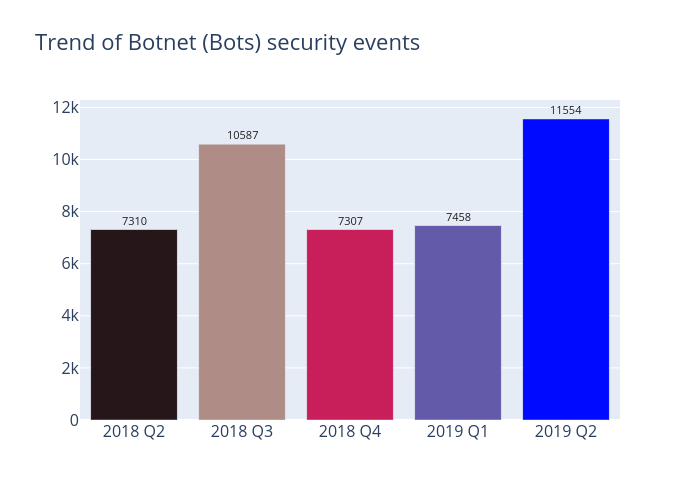 Figure 4 - Trend of Botnet (Bots) security events
Figure 4 - Trend of Botnet (Bots) security events
Compared with the previous quarters, the number of Botnet (bots) in Hong Kong network reached a record high of 11,554 in 2019 Q2; caused mainly by a surge in Ramnit bots, from 57 in Q1 to 4,522 in Q2, up more than seventy-eight times in the first quarter.
Also, Ramnit overtook Mirai at the top of Major Botnet Families in Hong Kong Networks. Ramnit’s operators are primarily focused on stealing sensitive information, such as passwords and online banking login credentials. It also functions as a backdoor capabilities that allow unauthorised access.
Based on the data in 2019 Q2, the counts of unique IP address attempting to connect to the Ramnit sinkholes soared sharply on both 12 and 14 June. Over 99% of infected IP addresses registered under ASN AS138979 (AresFlare CO., Ltd (Cambodia)) and AS138570 (AresFlare Network Limited). HKCERT has notified all the affected ASN during the regular botnet cleanup operations.
| HKCERT urges users to protect computers so as not to become part of the botnets. |
|
HKCERT has been following up the security events received and proactively engaged local ISPs for the botnet clean up since June 2013. Currently, botnet cleanup operations against major botnet family - WannaCry, Avalanche, XCode Ghost, Pushdo, Citadel, Mumblehard, Ramnit, ZeroAccess and GameOver Zeus are still in action.
HKCERT urges general users to join the cleanup acts. Ensure your computers are not being infected and controlled by malicious software.
Protect yourself and keep the cyberspace clean.
| Users can use the HKCERT guideline to detect and clean up botnets |
|
Download Report
< Please click to download Hong Kong Security Watch Report >
1 IFAS Information Feed Analysis System is a HKCERT developed system that collects global security intelligence relating to Hong Kong for analysis.
2 Refer to Appendix 1 for the Sources of Information
Share with


