Windows Remote Desktop Vulnerability may be used to spread worms

Working exploits for a recent Windows vulnerability on Remote Desktop is publicly available on the Internet. This has lowered the technical hurdle for attackers to perform attacks. Some security researchers have warned that this vulnerability has potential to make a wide spreading worm. Users are advised to put patching of this vulnerability a highest priority.
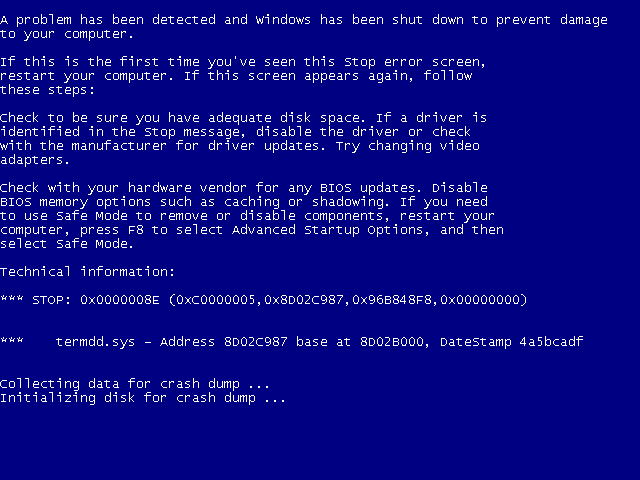
Remote Desktop1 is a system application which comes with most versions of Microsoft Windows Operating Systems. It allows users remotely connecting to a computer via TCP port 3389. Microsoft’s security bulletin summary for March 2012 reported a vulnerability of Remote Desktop (MS12-20) which was classified as critical level. Intruder can make use of this vulnerability to perform denial-of-service attack on remote vulnerable machines (Blue Screen of Death) or even take control of the machines.
We highly recommend users to apply the security updates from Microsoft. If you are unable to apply the security updates in short time period, below are some workarounds you may consider to reduce the risk.
- Enable Remote Desktop’s Network Level Authentication (NLA) to require authentication before a remote desktop session is established to the remote desktop server. Once NLA enabled on systems, NLA would require an attacker to first authentication to the server before attempting to exploit the vulnerability. This setting is only available on Windows Server 20082.
- Use other alternative remote management applications such as VNC and pcAnywhere, instead of remote desktop. Note that using more application programs implies managing more security updates will be required.
- By default, the remote desktop feature is not enabled on all Windows operating systems. Disable remote desktop if it is no longer in use.
If you really need to use remote management server (like Remote Desktop, VNC or pcAnywhere, etc.), we recommend you protecting it with VPN or SSH tunnels with strong authentication. You may also restrict the access to remote management server from only solicit IP address blocks by the firewall.
HKCERT had issued a security bulletin on the vulnerability:
Reference:
- What is Remote Desktop Connection:
http://windows.microsoft.com/en-US/windows-vista/Remote-Desktop-Connection-frequently-asked-questions - Configure Network Level Authentication for Remote Desktop Services Connections:
http://technet.microsoft.com/en-us/library/cc732713.aspx
Share with
