Anonymous threatened to make Internet Blackout 31 March 2012
When you read this article, you do not need to be a fortune teller to “predict” if an Internet blackout really occurred on 31 March 2012. Our analysis was that Anonymous’ intention to blackout the Internet via DDoS attack to DNS root servers would not be a success.

Background
Anonymous hacking group delivered a very high profile threatening message in February, claiming to take out the so called “Operation Global Blackout” on 31 March 2012 to bring down the Internet (http://pastebin.com/NKbnh8q8). Their proclaimed objective of the attack was to protest against Stop Online Piracy Act (SOPA), Wall Street, irresponsible leaders and the bankers. In their message they stated they will flood the DNS root servers by reflective DNS amplification attack.
Impact if the attack succeeds
DNS resolution of domain names to IP address is the basis of Internet services like web, email and others. DNS root servers are the starting points of all DNS queries. If all DNS root servers fail to deliver their services, the consequence is that DNS resolution of the next level of DNS servers, i.e. global top levels domains (TLD) including .com, org, .net, .info and country code TLD (ccTLD) will subsequently fail. This snow ball will roll down to implicate a total blackout of the Internet.
Built-in defenses of DNS root servers
Because of the criticality of DNS to the Internet, Root and TLD DNS server architecture by design has taken into consideration DDoS attacks, excess requests and system failures. The root DNS architecture is intentionally unorganized, diversified and resilient in order not to have a single common vulnerability and a single point of failure. The infrastructure is well prepared daily for attacks of this kind. There are 13 root servers with hundreds of instances globally (http://root-servers.org/). Some instances may even have multiple physical nodes behind. If any root server is down, users will be directed to any available server with the smallest “distance” to obtain service.
Security researcher Rob Graham at Errata Security had a good article analyzing how DNS root server architecture and other factors are good mitigation measures to defend DDoS attack.
http://erratasec.blogspot.com/2012/02/no-anonymous-cant-ddos-root-dns-servers.html
ISC (the operating arm of F-root server which contributed to one third of the global root servers), CERTs, Internet exchange centres and governments around the world were coordinating regarding this incident. However they are not acting in a high profile manner because they do not want to make this a media attention and inadvertently credits any party.
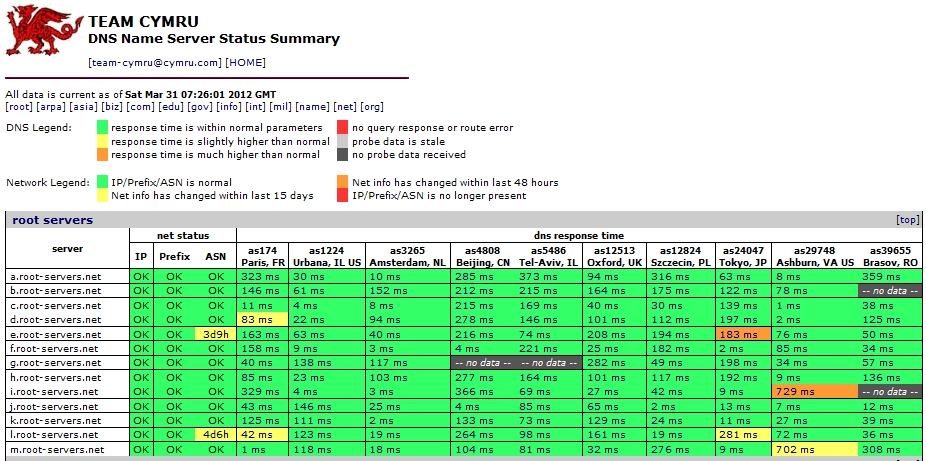
HKCERT monitored root and TLD servers via Team Cymru DNS Status Summary website: http://www.cymru.com/monitoring/dnssumm on every working day. Below was captured on 31 March 2012. We see nothing else special from normal days in our perspective.
There is no doubt that Anonymous has the capability and may be very determined to launch a DDoS attack. However, we do not see it would succeed. We had no Internet Blackout, none at all, as expected.
Share with
