Web 3.0 Cyber Security New Horizons: Strategies and Practices for Addressing Digital Age Challenges
Web 3.0 is considered the next generation of Internet technology, with its technology aimed at achieving a higher level of intelligence, automation, and personalisation.
The online world has already seen the emergence of Web 3.0 products, and future technology will rapidly develop around Web 3.0, thus gaining the attention of industries and even governments:
- At the end of 2022, the Hong Kong SAR Government issued a policy statement on the development of virtual assets in Hong Kong.
- In April 2023, the Institute of Web 3.0 Hong Kong was officially established, and the Chief Executive of Hong Kong, John Lee Ka-Chiu, was invited to deliver a speech at the ceremony.
- On June 1, 2023, the Securities and Futures Commission issued the “Guidelines for Virtual Asset Trading Platform Operators,” which officially came into effect.
However, new technology also brings unprecedented cyber security risks, as well as cyber security incidents related to Web 3.0 technology.
HKCERT listed cyber-attacks targeting Web 3.0 as one of five key information security risks in 2023, and it is crucial for the public to understand Web3.0 and its security risks.
This article will briefly introduce what Web 3.0 is, the potential cyber security risks of Web 3.0, and information security recommendations.
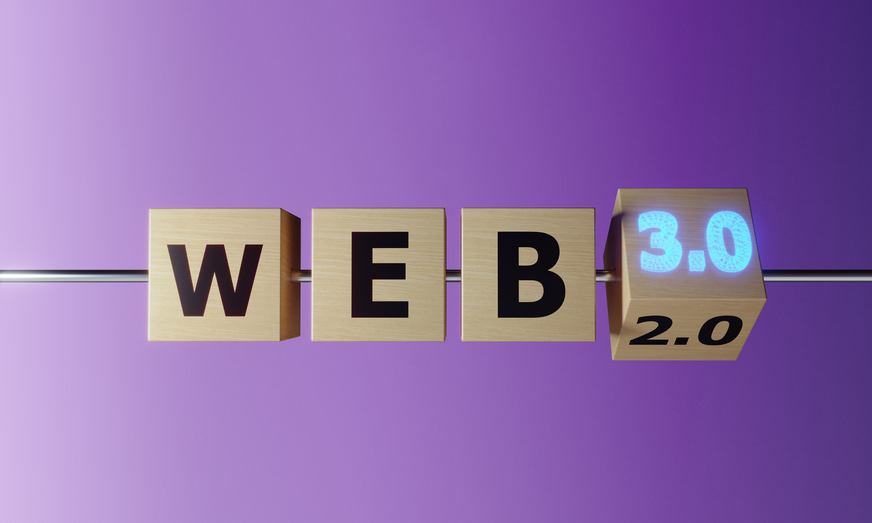
From Web 1.0 to Web 3.0
Over the years, the development of the Internet has seen great improvement, and it is generally believed that we have now entered the third generation:
Web 1.0 (1991-early 2000s):
Web 1.0 is considered the early stage of the internet, dominated by static HTML webpages. During this period, website content was usually created and updated by web developers, and users could only browse and read without interacting with the site. Websites at this time were similar to online promotional flyers, with the primary purpose of obtaining and disseminating information.
Web 2.0 (early 2000s-present):
Web 2.0 refers to a more interactive and dynamic web technology, where websites during this period allowed users to participate in creating and managing content, promoting social interaction and collaboration. Representative technologies of this period include AJAX and RSS, with representative websites such as Facebook, YouTube, and Wikipedia. Web 2.0 websites have higher usability and interactivity, emphasising user participation, and the internet has become a platform for sharing and collaboration.
Web 3.0 (future development trend):
Web 3.0 will leverage artificial intelligence, the Semantic Web, blockchain technologies, and decentralised applications to enable websites and applications to better understand, analyse, and process data, providing users with more accurate and personalised information. Web 3.0 will also emphasise data ownership and privacy protection, allowing users to have more control over their data.
Cyber Security Risks of Web 3.0
Although Web 3.0 brings many advantages, it also faces some cyber security risks. The following are some Web 3.0 cyber security risks and cyber-attack incidents:
- Smart contract security vulnerabilities: Smart contracts are automated execution protocols based on blockchain technology. However, since they are source code written by humans, smart contracts may have security vulnerabilities due to human mistakes or inadequate security measures.
In 2016, a decentralised autonomous organisation called The DAO was attacked, resulting in the theft of millions of dollars’ worth of Ether. This incident revealed the potential security risks of smart contracts. - Security issues of virtual asset trading platform and decentralised applications (DApps): With the development of Web 3.0, more and more virtual asset trading platform and DApps are appearing in the market. However, they may have security issues, such as code vulnerabilities and backend server security. These issues may lead to the loss of user data and assets.
On August 19, 2021, the cryptocurrency exchange Liquid Global suffered a hacker attack worth approximately $97 million.
In March 2022, hackers successfully gained access to the private keys and stole approximately $620 million worth of cryptocurrency. - 51% attack: Blockchain technology's consensus mechanism may be threatened by a 51% attack. When a malicious participant or organisation controls more than 51% of the network's computing power, they can carry out double-spend attacks and tamper with transaction records. This type of attack has already occurred in some small blockchain networks.
Ethereum Classic (ETC) attack: In January 2019, the Ethereum Classic network suffered a 51% attack. The attacker successfully carried out multiple double-spend transactions, stealing over one million dollars’ worth of ETC. - Privacy leaks: Although Web 3.0 introduces many privacy protection technologies, such as zero-knowledge proofs and secure multi-party computation, users still need to be vigilant when using these technologies. In some cases, user data may be leaked to third parties without their knowledge.
- Fraud and theft in value exchange: The exchange of digital currencies and tokens has become more common in the Web 3.0 era. However, this also provides opportunities for fraud and theft. For example, some dishonest projects may commit fraud through initial coin offerings (ICOs),or exploit security vulnerabilities in exchanges to steal user assets.
- Phishing attacks: Web 3.0 is not immune to phishing attacks either, for example, hackers may imitate a popular cryptocurrency wallet or decentralised finance platform and then send the fake website link to victims through email, social media, or other means.
MetaMask is a widely used Ethereum browser plugin wallet. Hackers have targeted MetaMask with phishing attacks, such as falsely claiming that your MetaMask wallet is about to be disabled and asking you to click on a link in the attachment to verify your account.
In June 2023, Bleeping Computer reported that a hacker organisation, Pink Drainer, pretended to be Cointelegraph and Decrypt to conduct interviews with victims. After gaining the trust of the victim, the victim was asked to go to a fake website for verification, with the purpose of stealing a Discord or Twitter account. Thereafter, the hacked account was used to send fake virtual asset projects or phishing websites to followers for deception. Mira Murati, the Chief Technology Officer of OpenAI, is also one of the organisational targets.
Recommendations
In the Web 3.0 era, cyber security becomes particularly important. The following are some recommendations to ensure security in the Web 3.0 environment:
- Protect your cryptocurrency assets: Crypto wallet has two types: Cold wallet and hot wallet. Users can consider putting a small amount of cryptocurrency in hot wallet for transactions, while the majority amount of cryptocurrency are put at cold wallet to reduce the risk of theft.
- Never disclose the wallet’s recovery phrase to a third party: If the hacker obtains the phrase, he could gain full control over the cryptocurrency in the wallet.
- Choose a virtual asset trading platform committed to cyber security: Security vulnerabilities of the trading platform are one of the targets of hackers. When choosing a platform, users should understand and compare the platform's security measures for user asset protection.
- Review smart contracts and DApps: Before using smart contracts and decentralised applications (DApps), ensure that they have undergone thorough review and testing. Use reliable security review services and check other users' ratings.
- Password management: Use strong passwords and change them regularly, avoiding using the same password to access different websites and services. Consider using a password manager to generate and store passwords.
- Two-factor authentication (2FA): Enable two-factor authentication for accounts to increase security. This usually requires entering a one-time verification code during login, which can be obtained via text message, app, or hardware device.
- Secure network connection: Use a VPN or other encryption methods to protect data transmitted over insecure networks. Avoid performing sensitive operations on public Wi-Fi networks.
- Defend against social engineering attacks: Be alert to emails and messages from strangers, and do not click on links or download attachments casually. Ensure that the person or service you interact with is trustworthy.
- Protect your digital identity: Avoid providing too much personal information when it is not necessary.
- Regularly back up data: Regularly back up important data to prevent data loss. Store backups in a secure location, such as encrypted cloud storage or an external hard drive.
- Keep your cyber security knowledge up-to-date: Regularly learn about and understand new cyber security threats and protection measures. Attend security training courses and follow industry news and trends.
- Cyber security policies and procedures: For businesses, it is crucial to develop and implement cyber security policies and procedures. Ensure that employees are aware of these policies and receive regular training.
HKCERT co-organised with the Office of the Government Chief Information Officer (OGCIO) and the Hong Kong Police Force (HKPF) to hold the seminar “Protect Your Online Security in Web 3.0” in early May. In the seminar, cyber security experts explained the security risks of Web 3.0, demonstrating the vulnerability of a smart contract and showing its consequences. People can learn from experts how to strengthen the security awareness in the world of Web 3.0.
The video clips of each speaker in the seminar have been uploaded to the HKCERT website and YouTube channel. Interested parties can revisit at: https://www.hkcert.org/event/protect-your-online-security-in-web-3-0-seminar-build-a-secure-cyberspace-2023
Reference links
- https://en.wikipedia.org/wiki/Poly_Network_exploit
- https://www.cnbc.com/2021/08/19/liquid-cryptocurrency-exchange-hack.html
- https://news.trendmicro.com/2023/01/13/metamask-paypal-usps-amazon-phishing-scams/
- https://www.bleepingcomputer.com/news/cryptocurrency/hackers-steal-3-million-by-impersonating-crypto-news-journalists
Share with