Hong Kong Security Watch Report (Q4 2014)
HKCERT is pleased to bring to you the "Hong Kong Security Watch Report" for the fourth quarter of 2014.
Nowadays, a lot of “invisible” compromised computers are controlled by attackers with the owner being unaware. The data on these computers may be mined and exposed every day and the computers may be utilized in different kinds of abuse and criminal activities.
The Hong Kong Security Watch Report aims to provide the public a better “visibility” of the situation of the compromised computers in Hong Kong so that they can make better decision in protecting their information security.
The report provides data about the activities of compromised computers in Hong Kong which suffer from, or participate in various forms of cyber attacks, including web defacement, phishing, malware hosting, botnet command and control centres (C&C) and bots. Computers in Hong Kong is defined as those whose network geolocation is Hong Kong, or the top level domain of their host name is “.hk” or “.香港”.
Highlight of Report
This report is for Quarter 4 of 2014.
In 2014 Q4, there were 12,437 unique security events related to Hong Kong used for analysis in this report. The information is collected with IFAS from 19 sources of information. They are not from the incident reports received by HKCERT.
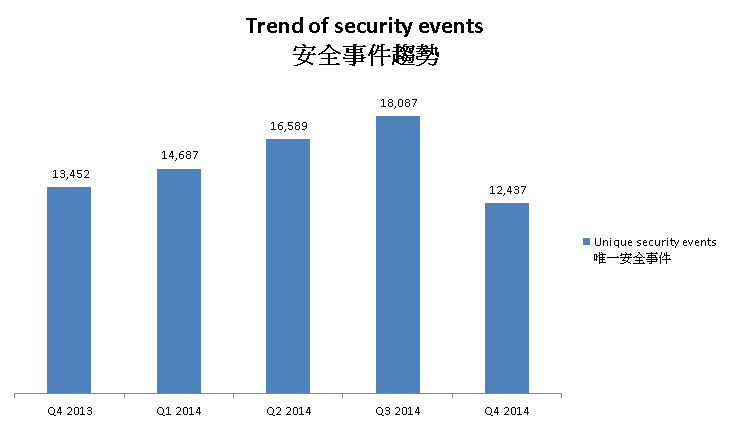
Figure 1 –Trend of security events3
The total number of security events in Q4 2014 dramatically decreased. It was the first decrease since Q3 2014.
Server related security events
Server related security events include malware hosting, phishing and defacement. Their trends and distributions are summarized below:
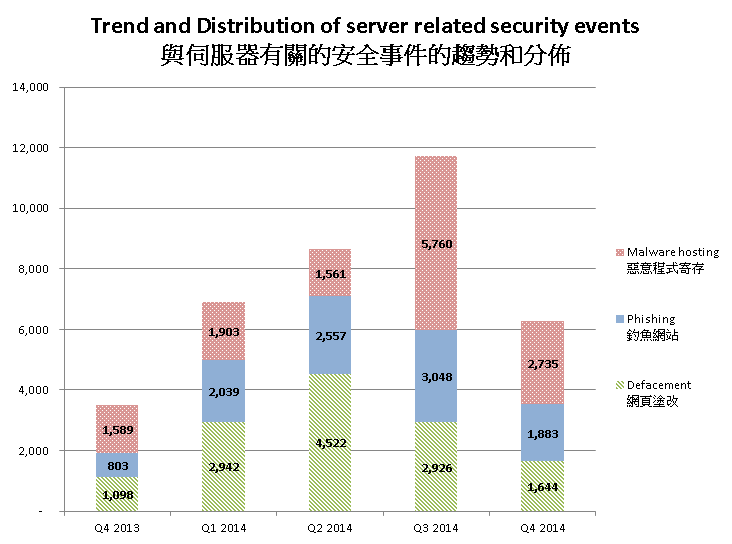
Figure 2 –Trend and distribution of server related security events4
The number of server related security events significantly decreased by 47% in Q4 2014.
In this quarter, the number of defacement events, phishing events and malware hosting events decreased by 44%, 38% and 54% respectively.
Though the number of total phishing events decreased, the number of phishing sites with top level domain .tk increased a lot. The number of related events increased 272% to 160 events. Among which, most of them are targeting taobao.com or alipay.com.
.tk was intended to be used by Tokelau, a territory of New Zealand. However, since the domain is available to individuals and small businesses free of charge, it was actually used by people all over the world. This domain is infamous of being abused for unwanted behaviours such as phishing and spam. According to a report of Anti-Phishing Working Group (APWG) , .tk contributed for 22% of all malicious domain registrations in the second half of 2013. Internet users should pay more attentions to this top level domain.
Abuse of another top level domain, .pw also increased significantly. The malware hosting events using .pw increased 110 folds to 331 events.
.pw was originally delegated to the Pacific island nation of Palau in 1997. But later it was redelegated. Similar to .tk, now the .pw domain is open to the public, known as the Professional Web. .pw was infamous for a source of spam mail . However, we discovered that its use in malware hosting is increasing.
| HKCERT urges system and application administrators to protect the servers. |
|
Botnet related security events
Botnet related security events can be classified into two categories:
- Botnet Command and Control Centres (C&C) security events – involving small number of powerful computers, mostly servers, which give commands to bots
- Bots security events – involving large number of computers, mostly home computers, which receive commands from C&C.
Botnet Command and Control Servers
The trend of botnet C&C security events is summarized below:
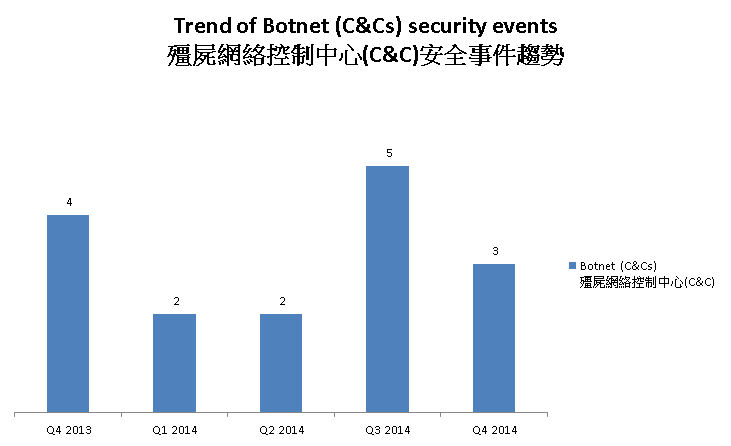
Figure 3 –Trend of Botnet (C&Cs) related security events
The number of botnet Command and Control Servers decreased this quarter.
There were 3 C&C servers reported in this quarter. One of the reported servers was identified as Zeus C&C server, while the other two were identified as IRC bot C&C servers.
The trend of botnet (bots) security events is summarized below:
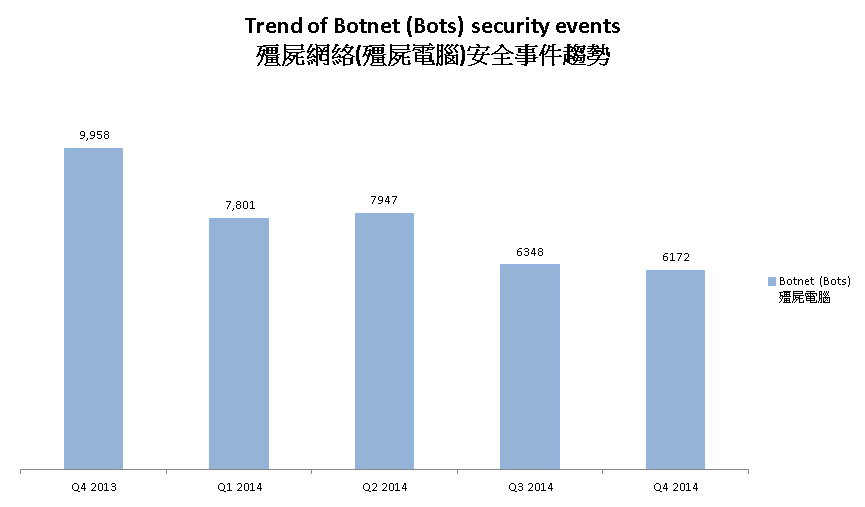
Figure 4 - Trend of Botnet (Bots) security events5
Number of Botnet (bots) on Hong Kong network decreased in this quarter.
In Q4 2014, the number of botnet infections in Hong Kong slightly decreased by 2.8%. 7 of the top 10 botnets had their numbers decreased. However, the other three had their numbers increased significantly.
The top three botnets, Conficker, Zeus and ZeroAccess continued their dropping trends. The number of ZeroAccess events dropped to below 1000 for the first time, which matched our previous prediction.
On the other hand, Virut, Pushdo and bankpatch botnets recorded a significant increase this quarter. Pushdo has been one of the largest botnet on the planet for a long time. It used to be the forth botnet in Hong Kong but the number of Pushdo events dropped dramatically this year, reaching a record low in the previous quarter. However, researchers discovered a new version of Pushdo in late September. Though very little, if any, improvement or new functionality could be found, it may be a framework for further improvements. This reflected the malware authors were putting new efforts on the malware. It may explain the sudden increase of the number.
Virut sends spams, launches DDoS attacks and conducts fraud and data theft. Pushdo sends spams, launches DDoS attacks and downloads other banking malwares. Bankpatch monitors specific banking websites and harvest user's passwords, credit card information and other sensitive financial data
HKCERT has been following up the security events received and proactively engaged local ISPs for the botnet clean up since June 2013. Currently, botnet cleanup operations against major botnet family - Pushdo, Citadel, ZeroAccess and GameOver Zeus are still in action.
| HKCERT urges users to protect computers so as not to become part of the botnets. |
|
HKCERT urges general users to join the cleanup acts. Ensure your computers are not being infected and controlled by malicious software.
Protect yourself and keep the cyberspace clean.
| Users can use the HKCERT guideline to detect and clean up botnets |
|
Download Report
< Please click to download Hong Kong Security Watch Report >
1 IFAS Information Feed Analysis System is a HKCERT developed system that collects global security intelligence relating to Hong Kong for analysis.
2 Refer to Appendix 1 for the Sources of Information
3 The numbers were adjusted to exclude the unconfirmed defacement events
4 The numbers were adjusted to exclude the unconfirmed defacement events
5 The number botnet(bots) security events in Q4 2013 was adjusted due to the update of numbers of the Zeus botnet.
Share with


