Hong Kong Security Watch Report (Q1 2015)
HKCERT is pleased to bring to you the "Hong Kong Security Watch Report" for the first quarter of 2015.
Nowadays, a lot of “invisible” compromised computers are controlled by attackers with the owner being unaware. The data on these computers may be mined and exposed every day and the computers may be utilized in different kinds of abuse and criminal activities.
The Hong Kong Security Watch Report aims to provide the public a better "visibility" of the situation of the compromised computers in Hong Kong so that they can make better decision in protecting their information security.
The report provides data about the activities of compromised computers in Hong Kong which suffer from, or participate in various forms of cyber attacks, including web defacement, phishing, malware hosting, botnet command and control centres (C&C) and bots. Computers in Hong Kong is defined as those whose network geolocation is Hong Kong, or the top level domain of their host name is “.hk” or “.香港”.
Highlight of Report
This report is for Quarter 1 of 2015.
In 2015 Q1, there were 10,936 unique security events related to Hong Kong used for analysis in this report. The information is collected with IFAS1 from 19 sources of information2. They are not from the incident reports received by HKCERT.
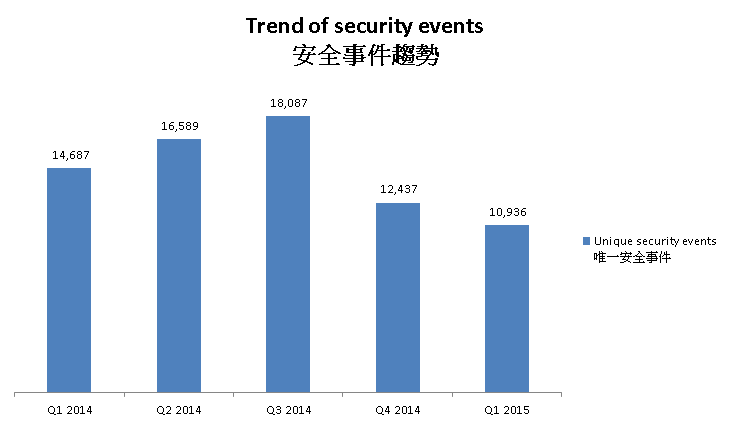
Figure 1 –Trend of security events3
The total number of security events in Q1 2015 decreased by 12% or 1501 events, continuing the drop since Q4 2014.
Server related security events
Server related security events include malware hosting, phishing and defacement. Their trends and distributions are summarized below:
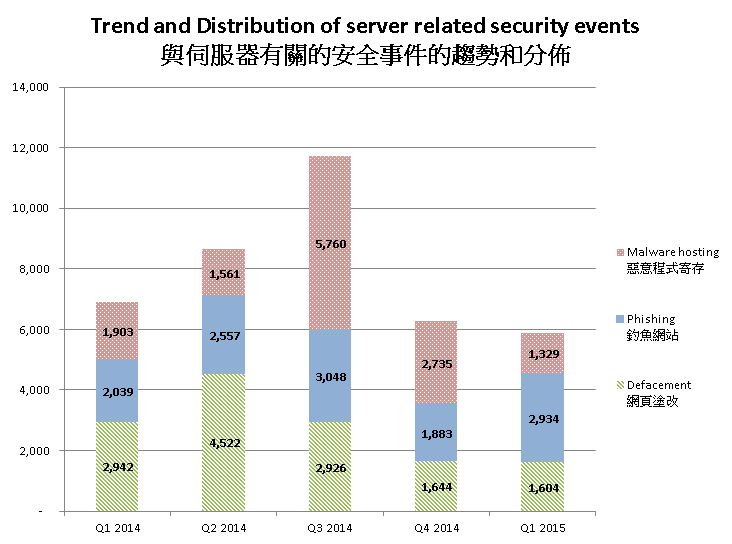
Figure 2 –Trend and distribution of server related security events4
The number of server related security events slightly decreased by 6% in Q1 2015.
In this quarter, the number of defacement events and malware hosting events decreased by 2% and 51% respectively; while the number of phishing events increased significantly by 55.8%.
The increase of phishing events was due to the increase in URL/IP ratio. The ratio this quarter (14.11) almost doubled the average ratio of the previous four quarters (7.48). The rapid increase of this number reflected that the number of URLs hosted in each IP address increased. In fact, the number of involved IP addresses actually decreased.
| HKCERT urges system and application administrators to protect the servers. |
|
Botnet related security events
Botnet related security events can be classified into two categories:
- Botnet Command and Control Centres (C&C) security events – involving small number of powerful computers, mostly servers, which give commands to bots
- Bots security events – involving large number of computers, mostly home computers, which receive commands from C&C.
Botnet Command and Control Servers
The trend of botnet C&C security events is summarized below:

Figure 3 –Trend of Botnet (C&Cs) related security events
The number of botnet Command and Control Servers increased this quarter.
There were 4 C&C servers reported in this quarter. One of the reported servers was identified as Zeus C&C server, while the other three were identified as IRC bot C&C servers.
The trend of botnet (bots) security events is summarized below:
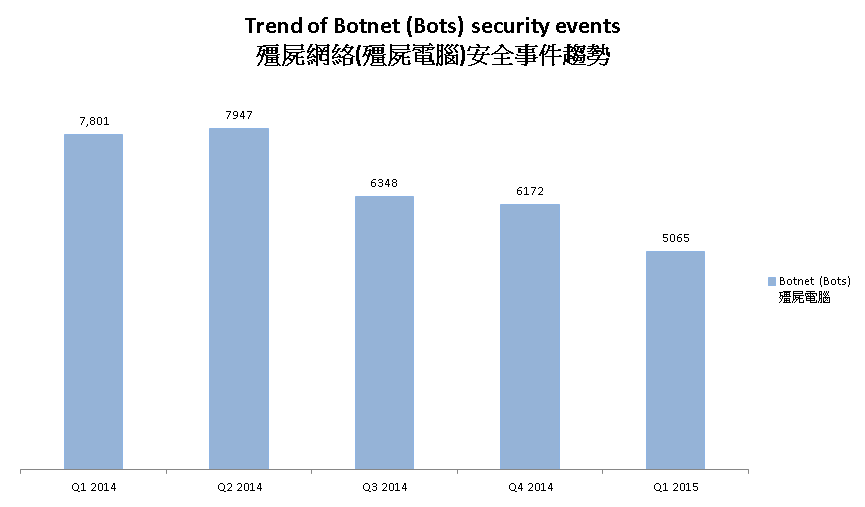
Figure 4 - Trend of Botnet (Bots) security events
Number of Botnet (bots) on Hong Kong network continued to decrease in this quarter since Q3 2014.
In Q1 2015, the number of botnet infections in Hong Kong decreased by 17.9%. Out of the top 10 botnets, 8 had double digit decreases in percentage (from 10% to 32%). However, the number of Gamarue botnet events increased by 206%.
The top three botnets of the previous quarter, Conficker, Zeus and ZeroAccess continued their dropping trends. Among them, ZeroAccess events dropped the most. It dropped 32% or 569 events. In the same period, the fourth botnet of the previous quarter, Virut continued to rise. Its number increased 5% and took over ZeroAccess as the third botnet in Hong Kong. It is the first time ZeroAccess dropped out of the top three.
However, researchers found out that ZeroAccess was reactivated after being silent for six months. ZeroAccess was once much stronger than today in 2013. Security researchers from Symantec found a flaw in the P2P communication mechanism in the botnet that enabled them to detect and clean up a large amount of botnets in July 2013. Law enforcements and other security vendors then launched another operation against ZeroAccess in December of the same year. After some struggling, the botnet operators surrendered and were silent since July 2014.
On 15 January, the botnet came back to life and started distributing click-fraud templates to compromised systems. Though the botnet operators didn’t attempt to infect new systems for more than one year, the reactivation of the botnet proved that the operators are putting new efforts to the botnet. Though we still have not yet detected the rise of ZeroAccess infection, we will pay more attention to its revival.
The eighth botnet, Gamarue, is another botnet that caught our eyes. Its number increased two folds to 52 events, which was a record high since Q2 of 2013. Researchers found that the botnet operators now use a new approach to spread the botnet – through macro in Microsoft Word documents. When a victim opens a malicious document, which was often sent via spam email, the document content will urge the user to enable macro. Once it is enabled, the macro will perform a multi-staged decoding and program execution to infect the computer.
Gamarue can steal sensitive information, allow hackers to remotely control the target system and further infect the victim with other malwares. In order to avoid being infected, HKCERT urges computers users not to open the attachments in any suspicious emails and do not enable macros in MS office documents that are from unreliable sources.
| HKCERT urges users to protect computers so as not to become part of the botnets. |
|
HKCERT has been following up the security events received and proactively engaged local ISPs for the botnet clean up since June 2013. Currently, botnet cleanup operations against major botnet family - Pushdo, Citadel, ZeroAccess and GameOver Zeus are still in action.
HKCERT urges general users to join the cleanup acts. Ensure your computers are not being infected and controlled by malicious software.
Protect yourself and keep the cyberspace clean.
| Users can use the HKCERT guideline to detect and clean up botnets |
|
Download Report
< Please click to download Hong Kong Security Watch Report >
1 IFAS Information Feed Analysis System is a HKCERT developed system that collects global security intelligence relating to Hong Kong for analysis.
2 Refer to Appendix 1 for the Sources of Information
3 The numbers were adjusted to exclude the unconfirmed defacement events
4 The numbers were adjusted to exclude the unconfirmed defacement events
Share with


