Hong Kong Security Watch Report (Q3 2016)
HKCERT is pleased to bring to you the "Hong Kong Security Watch Report" for the third quarter of 2016.
Nowadays, a lot of “invisible” compromised computers are controlled by attackers with the owner being unaware. The data on these computers may be mined and exposed every day and the computers may be utilized in different kinds of abuse and criminal activities.
The Hong Kong Security Watch Report aims to provide the public a better "visibility" of the situation of the compromised computers in Hong Kong so that they can make better decision in protecting their information security.
The report provides data about the activities of compromised computers in Hong Kong which suffer from, or participate in various forms of cyber attacks, including web defacement, phishing, malware hosting, botnet command and control centres (C&C) and bots. Computers in Hong Kong is defined as those whose network geolocation is Hong Kong, or the top level domain of their host name is “.hk” or “.香港”.
Highlight of Report
This report is for Quarter 3 of 2016.
In 2016 Q3, there were 6,774 unique security events related to Hong Kong used for analysis in this report. The information is collected with IFAS1 from 19 sources of information2. They are not from the incident reports received by HKCERT.
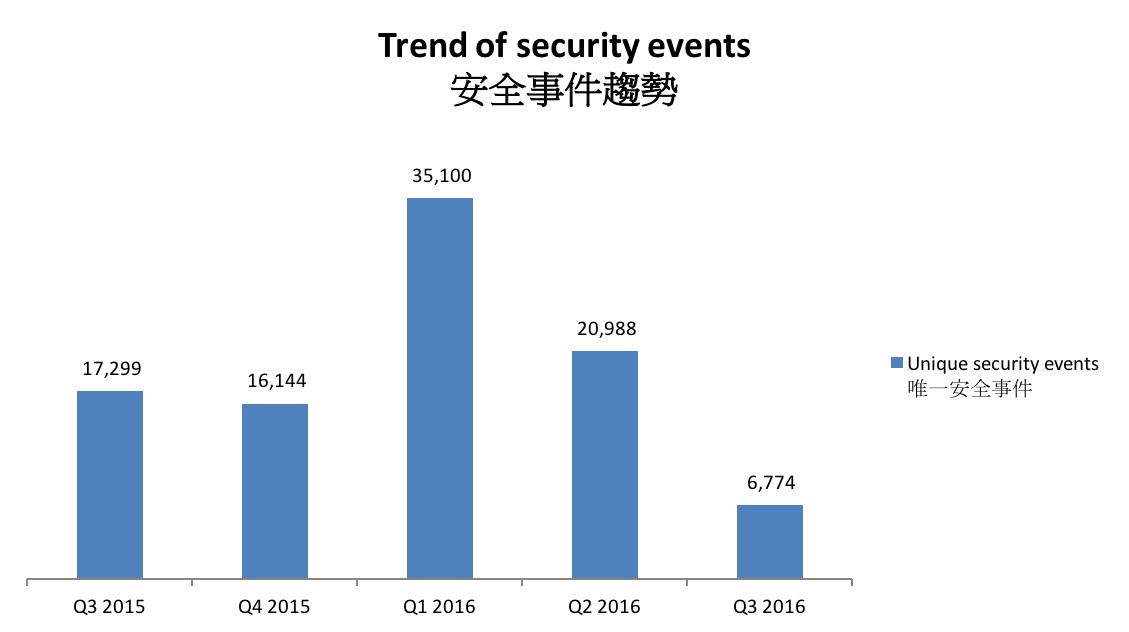
Figure 1 –Trend of security events3
The total number of security events in Q3 2016 decreased significantly by 68% or 14,214 events. The sharp decrease was due to two reasons. First, the data from CleanMX, which is one of our major sources of phishing events and malware hosting events, was temporarily unavailable in this quarter, leading to a huge drop in server related security events. Second, in the same period, the number of botnet (bots) events dropped significantly by 29%. As a result, the number of security events reached an all-time low of 6,774.
Server related security events
Server related security events include malware hosting, phishing and defacement. Their trends and distributions are summarized below:
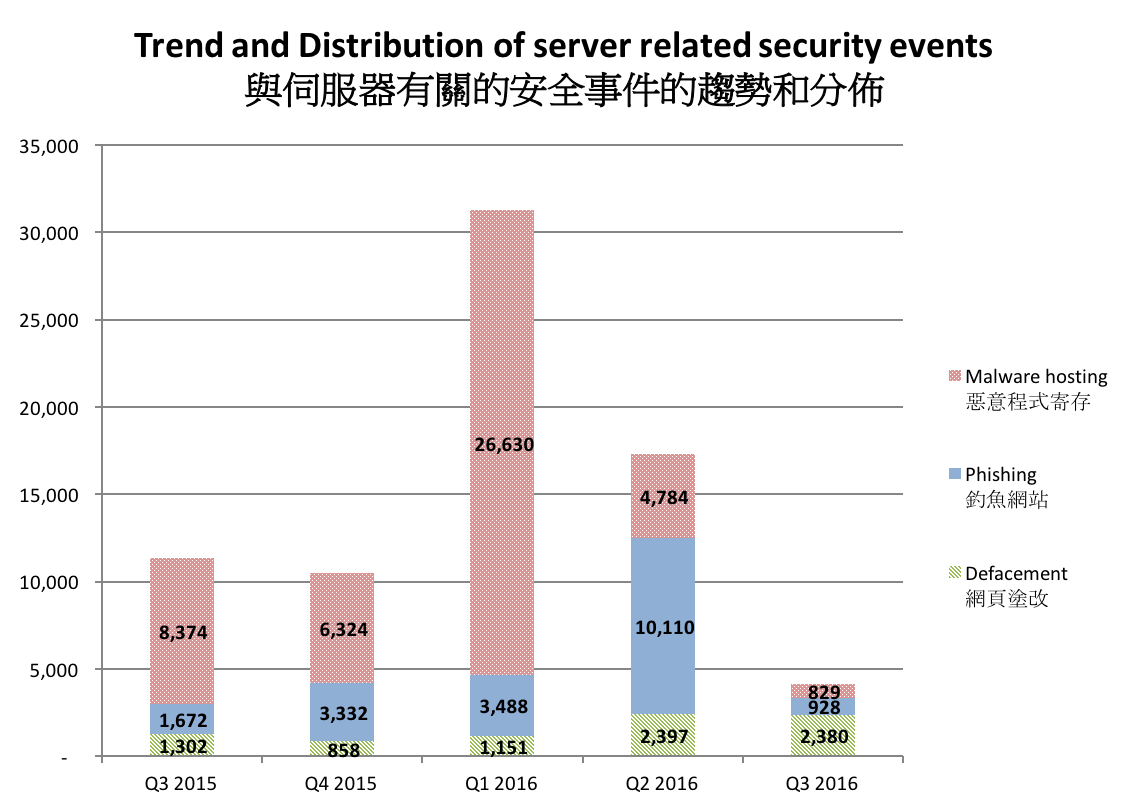
Figure 2 –Trend and distribution of server related security events
The number of server related security events decreased from 17,291 to 4,137 (decreased by 76%) in Q3 2016.
As mentioned in the previous section, the drop in number was due to the unavailability of one of our major data sources. It could not be interpreted as an improvement in server related security events. The number server events contributed from CleanMX data feed in Q2 2016 was 13,801 (80% of total server events).
In this quarter, the most popular TLD for phishing event was “.cc”. It is the first time a TLD other than “.com” was ranked number one. Most of the events were from a free domain registrar “.usa.cc”.
“.cc” is the country code top-level domain (ccTLD) of for Cocos (Keeling) Islands, an Australian territory. However, it was being abused for malicious purpose. According to Anti-Phishing Working Group (APWG) Phishing Attack Trends Reports Q2 2014, 1% of all malicious domains were from “.cc”.
The situation of one of its second level domain, “.co.cc” was even more serious. The “.co.cc” subdomain is managed by the CO.CC company, which provided free and discounted domains. Since a high proportion of websites using “.co.cc” were malicious, all “.co.cc” websites were blocked by Google since 2011. The domain then suddenly shut down at 2012. Now all .co.cc domains were redirected to .cc.cc domains.
| HKCERT urges system and application administrators to protect the servers. |
|
Botnet related security events
Botnet related security events can be classified into two categories:
- Botnet Command and Control Centres (C&C) security events – involving small number of powerful computers, mostly servers, which give commands to bots
- Bots security events – involving large number of computers, mostly home computers, which receive commands from C&C.
Botnet Command and Control Servers
The trend of botnet C&C security events is summarized below:
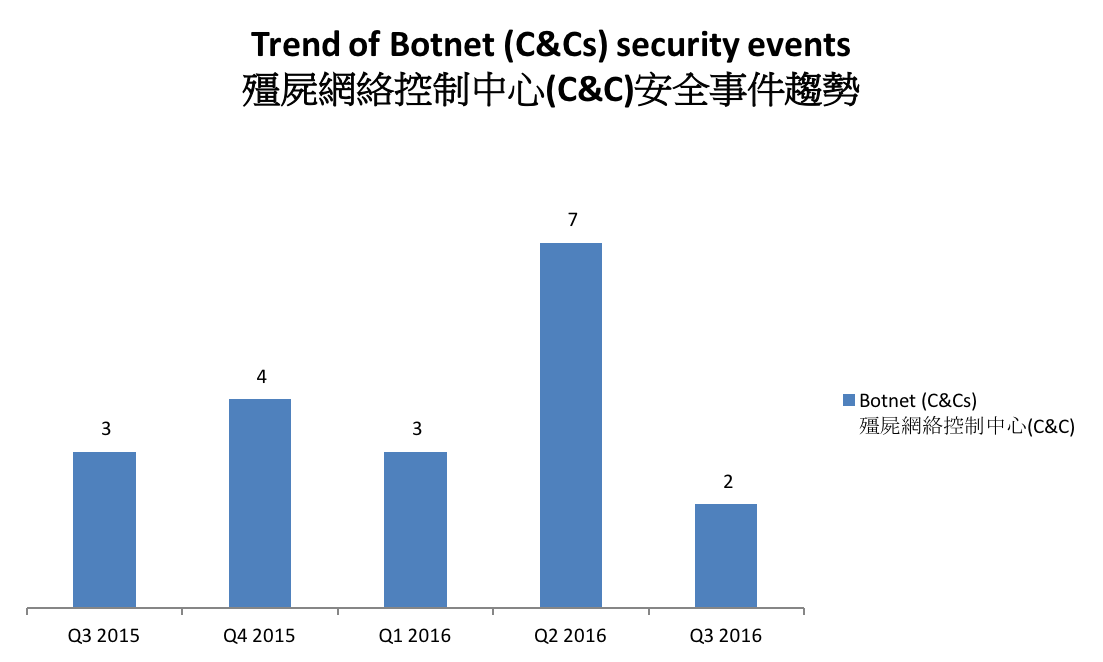
Figure 3 –Trend of Botnet (C&Cs) related security events
The number of botnet Command and Control Servers decreased this quarter.
There were 2 C&C servers reported in this quarter. Both were identified as IRC bot C&C servers
The trend of botnet (bots) security events is summarized below:
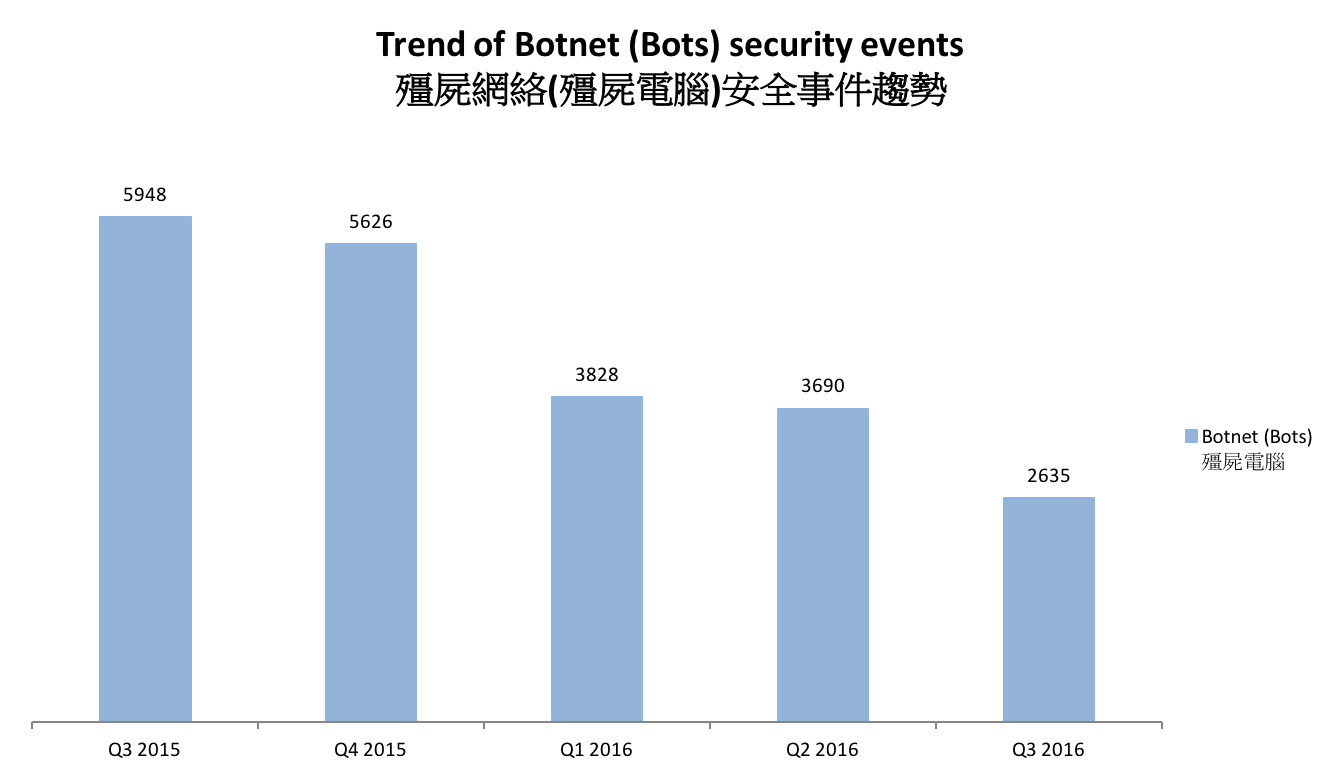
Figure 4 - Trend of Botnet (Bots) security events
Number of Botnet (bots) on Hong Kong network decreased this quarter. The number of events of Bedep, which was the third botnet last quarter, dropped the most by 86% or 290 events. Four other botnets recorded a decrease of 11-28% too. However, the botnet Nivdort botnet appeared in the chart for the first time.
Nivdort is a Trojan that steals sensitive information silently in the target systems. Nivdort spreads through spam emails. In early 2016, researchers discovered a spamming campaign sending malicious zip files pretending to be a vouchers or Whatsapp message. If the malicious file is opened, it will try to infect the system with Nivdort.
Once infected, Nivdort can disable the firewall notifications from the Windows Security Center. It will collect sensitive information of the victims including login credentials and credit card information.
| HKCERT urges users to protect computers so as not to become part of the botnets. |
|
HKCERT has been following up the security events received and proactively engaged local ISPs for the botnet clean up since June 2013. Currently, botnet cleanup operations against major botnet family - Pushdo, Citadel, ZeroAcces, GameOver Zeus and Ramnit are still in action.
HKCERT urges general users to join the cleanup acts. Ensure your computers are not being infected and controlled by malicious software.
Protect yourself and keep the cyberspace clean.
| Users can use the HKCERT guideline to detect and clean up botnets |
|
Download Report
< Please click to download Hong Kong Security Watch Report >
1 IFAS Information Feed Analysis System is a HKCERT developed system that collects global security intelligence relating to Hong Kong for analysis.
Share with


