Hong Kong Security Watch Report (Q2 2016)
HKCERT is pleased to bring to you the "Hong Kong Security Watch Report" for the second quarter of 2016.
Nowadays, a lot of “invisible” compromised computers are controlled by attackers with the owner being unaware. The data on these computers may be mined and exposed every day and the computers may be utilized in different kinds of abuse and criminal activities.
The Hong Kong Security Watch Report aims to provide the public a better "visibility" of the situation of the compromised computers in Hong Kong so that they can make better decision in protecting their information security.
The report provides data about the activities of compromised computers in Hong Kong which suffer from, or participate in various forms of cyber attacks, including web defacement, phishing, malware hosting, botnet command and control centres (C&C) and bots. Computers in Hong Kong is defined as those whose network geolocation is Hong Kong, or the top level domain of their host name is “.hk” or “.香港”.
Highlight of Report
This report is for Quarter 2 of 2016.
In 2016 Q2, there were 20,988 unique security events related to Hong Kong used for analysis in this report. The information is collected with IFAS1 from 19 sources of information2. They are not from the incident reports received by HKCERT.
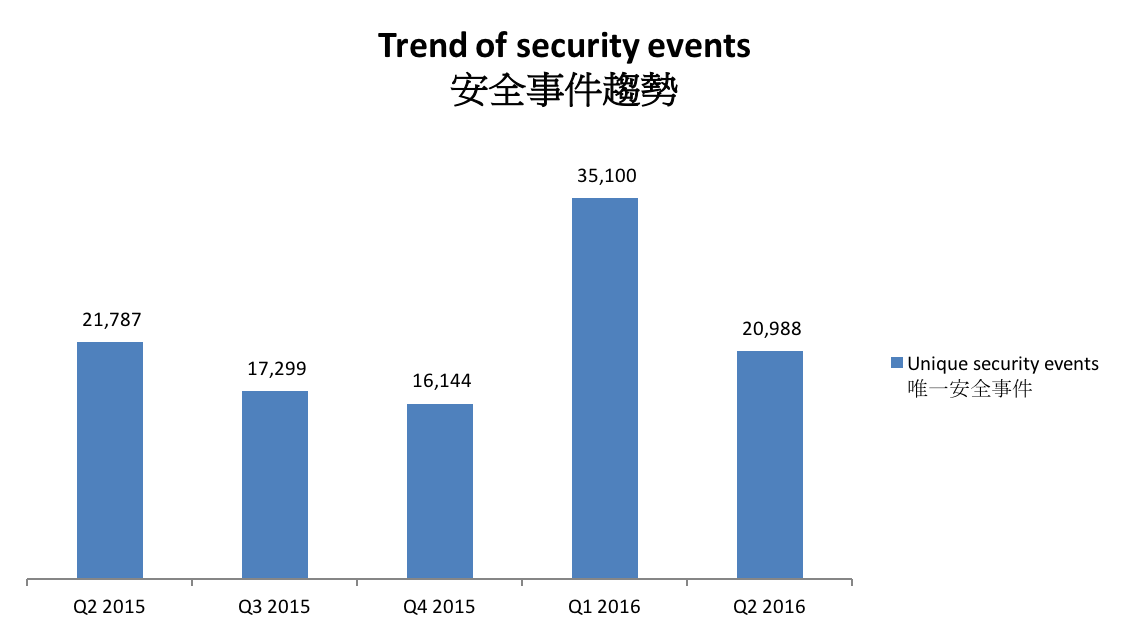
Figure 1 –Trend of security events3
The total number of security events in Q2 2016 decreased significantly by 40% or 20,988 events. It was mainly due to the decrease in server related events.
Server related security events
Server related security events include malware hosting, phishing and defacement. Their trends and distributions are summarized below:
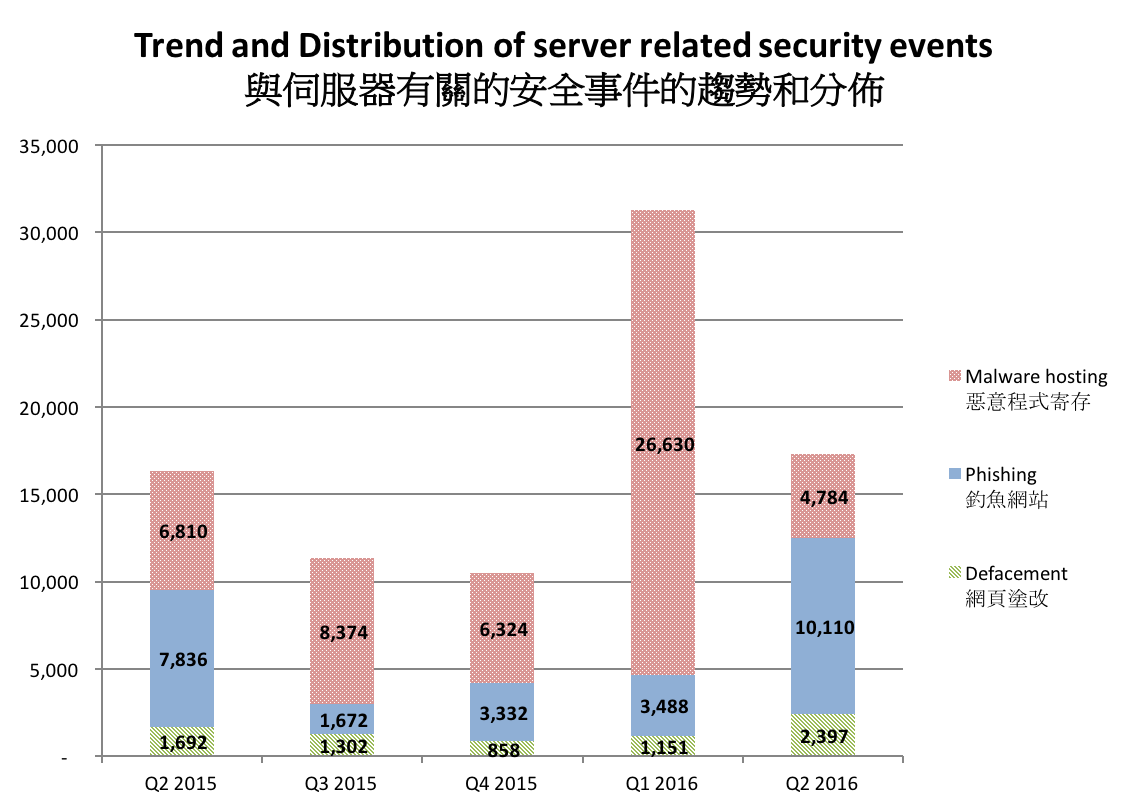
Figure 2 –Trend and distribution of server related security events4
The number of server related security events decreased from 31,269 to 17,291 (decreased by 45%) in Q2 2016.
In this quarter, the number of defacement events and phishing events increased by 108% and 189% respectively, while the malware hosting events decreased by 82%. The number of malware hosting events became normal after being extraordinarily high last quarter. The URL/IP ratio of malware hosting events dropped from 32.71 to 9.31.
On the other hand, phishing events reached a record high of 10,110 events with URL/IP ratio increased from 8.66 to 23.62. The high number was contributed by a few compromised websites and a free domains registrar.
In this quarter, most of the events were in compromised servers. The most serious case was from the domain hitsem.com, which contributed 5,142 events (50.9%). We have reported this domain in Hong Kong Security Watch Report 2015 Q4, in which it contributed to 1,085 events. The major phishing target was a Brazilian company aircompanybalonismo.com.br. This story reflected that security incidents should be handled in time, otherwise they may continue to cause even more damage. As of the time of writing, the websites associated to this domain were shut down and could not be reached.
The second largest source of phishing events were a few domains from a Korean online shop FREEMURA hosted 1296 phishing events. Those domains include lovemura.net, muralove.net, luxmura.com, lovemura.com, muralove.com, luxmura.net and freemura1.kr. All of them resolved to the same IP address. These phishing events were targeting Google accounts.
The third largest source of phishing events was the domain usa.cc. It is a free domains registrar that allow its users to register unlimited free subdomains. Free domains registrar and Dynamic DNS provider has long been abused by criminals to register domains for phishing URLs. In order to lure the potential victims to click on the phishing links, criminals will use domains very similar to the original link. Free domains registrars provide a way to register new domains in low cost.
This quarter there were 993 phishing events utilizing usa.cc, most of them targeting a Japanese gaming site hiroba.dqx.jp. This domain was reported to be a major phishing target in Hong Kong Security Watch Report 2015 Q2.
| HKCERT urges system and application administrators to protect the servers. |
|
Botnet related security events
Botnet related security events can be classified into two categories:
- Botnet Command and Control Centres (C&C) security events – involving small number of powerful computers, mostly servers, which give commands to bots
- Bots security events – involving large number of computers, mostly home computers, which receive commands from C&C.
Botnet Command and Control Servers
The trend of botnet C&C security events is summarized below:
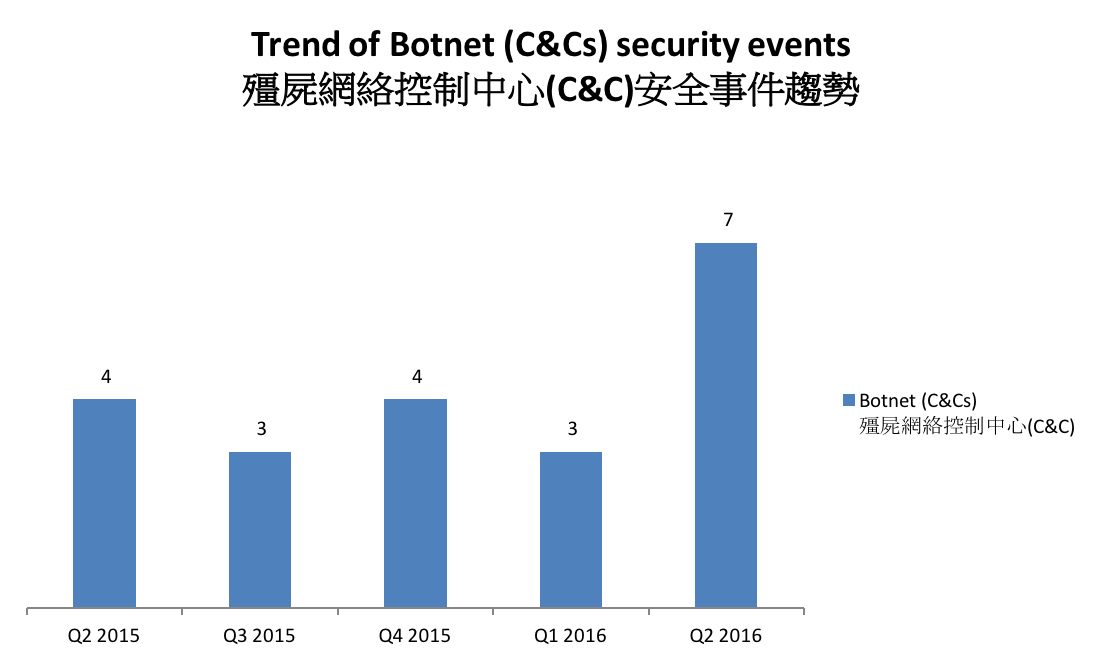
Figure 3 –Trend of Botnet (C&Cs) related security events
The number of botnet Command and Control Servers increased this quarter.
There were 7 C&C servers reported in this quarter. Six were identified as IRC bot C&C servers while one was identified as HTTP server.
The trend of botnet (bots) security events is summarized below:
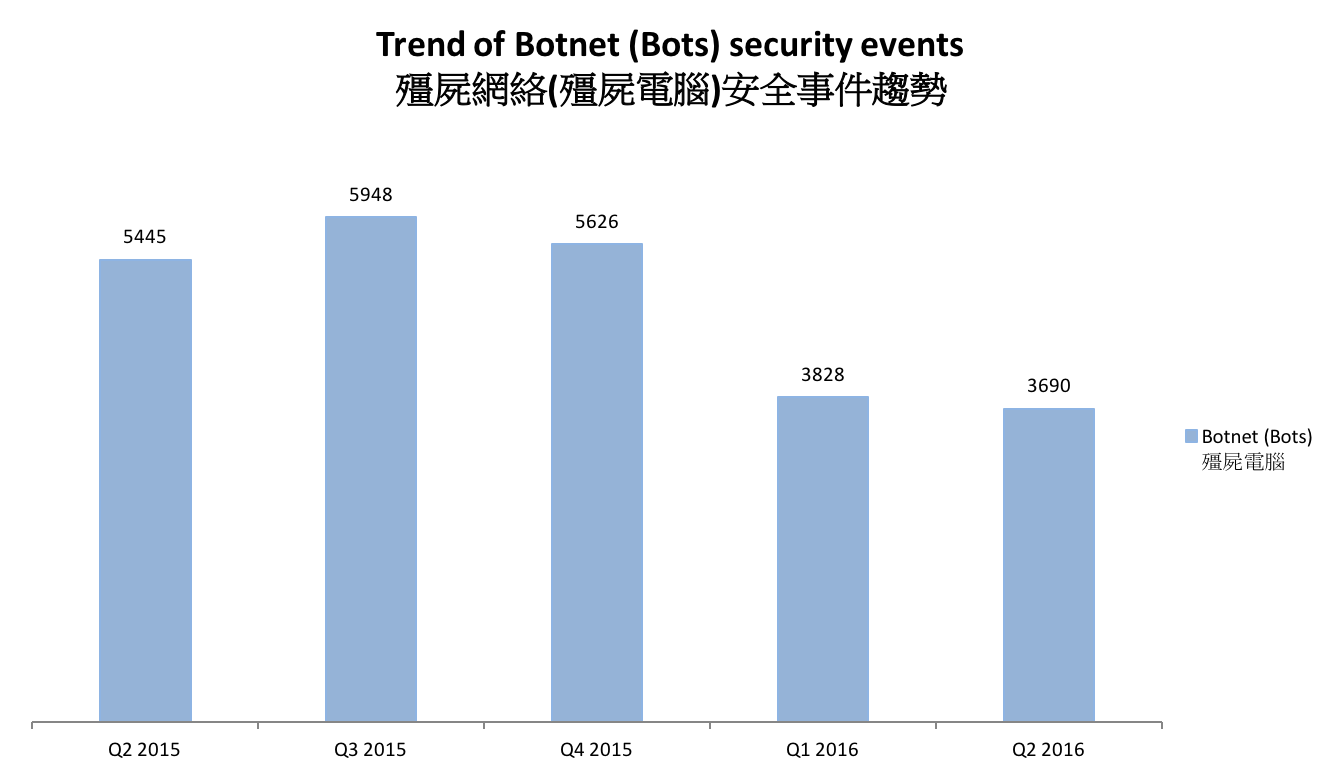
Figure 4 - Trend of Botnet (Bots) security events
Number of Botnet (bots) on Hong Kong network decreased slightly this quarter. Bedep grew from the eighth to the third this quarter. However, the number reached the peak at April. Its number has dropped significantly to 139 events in May and 69 events in June.
We have reported last quarter that Bedep was believed to have strong connection with Angler Exploit Kit. The drop of Bedep may be due to the disappearance of Angler Exploit Kit. In early June, the banking malware gang behind the Lurk banking Trojan was busted by Russian police. Researchers found that the same group was also linked to the Angler Exploit Kit. After the arrest, activities from Angler Exploit Kit effectively disappeared until now.
Though the botnet may be disrupted by the arrest, cyber criminals will certain find alternatives. HKCERT will keep monitoring this botnet.
| HKCERT urges users to protect computers so as not to become part of the botnets. |
|
HKCERT has been following up the security events received and proactively engaged local ISPs for the botnet clean up since June 2013. Currently, botnet cleanup operations against major botnet family - Pushdo, Citadel, ZeroAcces, GameOver Zeus and Ramnit are still in action.
HKCERT urges general users to join the cleanup acts. Ensure your computers are not being infected and controlled by malicious software.
Protect yourself and keep the cyberspace clean.
| Users can use the HKCERT guideline to detect and clean up botnets |
|
Download Report
< Please click to download Hong Kong Security Watch Report >
1 IFAS Information Feed Analysis System is a HKCERT developed system that collects global security intelligence relating to Hong Kong for analysis.
Share with


