Hong Kong Security Watch Report (Q4 2018)
HKCERT is pleased to bring to you the "Hong Kong Security Watch Report" for the fourth quarter of 2018.
Nowadays, a lot of “invisible” compromised computers are controlled by attackers with the owner being unaware. The data on these computers may be mined and exposed every day and the computers may be utilized in different kinds of abuse and criminal activities.
The Hong Kong Security Watch Report aims to provide the public a better "visibility" of the situation of the compromised computers in Hong Kong so that they can make better decision in protecting their information security.
The report provides data about the activities of compromised computers in Hong Kong which suffer from, or participate in various forms of cyber attacks, including web defacement, phishing, malware hosting, botnet command and control centres (C&C) and bots. Computers in Hong Kong is defined as those whose network geolocation is Hong Kong, or the top level domain of their host name is “.hk” or “.香港”.
Highlight of Report
This report is for Quarter 4 of 2018.
In 2018 Q4, there were 16,414 unique security events related to Hong Kong used for analysis in this report. The information is collected with IFAS1 from 13 sources of information2. They are not from the incident reports received by HKCERT.
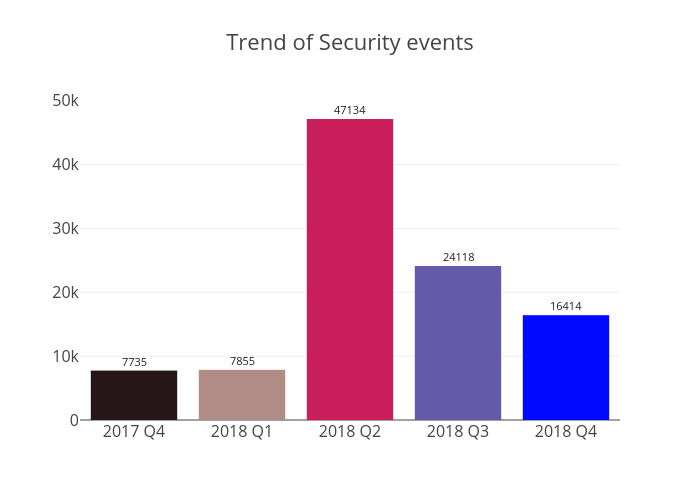
Figure 1 –Trend of security events
The total number of security events in 2018 Q4 is 16,414, declined by 32% or 7,704 events compared to the previous quarter. The decrease was mostly contributed by the reduction of defacement events by 89%, while the phishing and malware hosting events increased slightly by 14% and 5% respectively. The number of events fluctuated in different quarters of 2018. There was a sharp growth and reached a peak at 47,134 in 2018 Q2 then gradually dropped down in Q3 and Q4.
Server related security events
Server related security events include malware hosting, phishing and defacement. Their trends and distributions are summarized below:
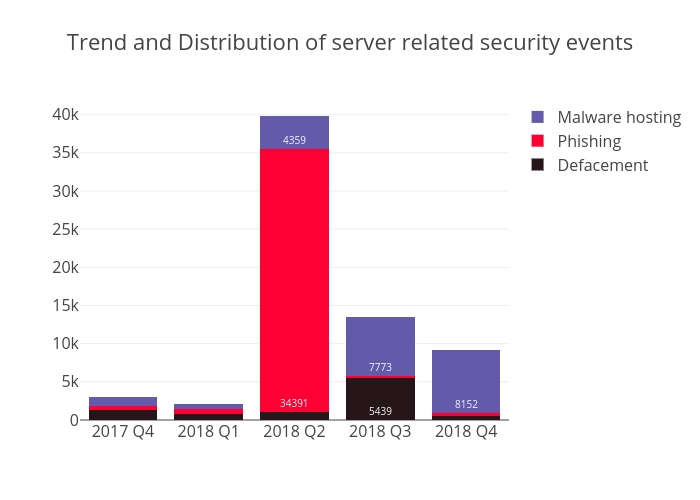 Figure 2 –Trend and distribution of server related security events
Figure 2 –Trend and distribution of server related security events
The number of phishing events, each involving a unique phishing URL, grew from 319 in Q3 to 365 in Q4, or a 14% increase. The URL/IP ratio remained at 3 in Q4, due to there was only a minor change in the number of unique phishing hosting IPs.
The number of malware hosting events, each involving a unique malware URL, grew slightly from 7,773 in Q3 to 8,152 in Q4, or a 5% increase. The top two IPs are 43.226.125.19 and 112.213.126.50, which accounted for 612 and 453 events respectively in Q4; and both were registered under AS38197 (Sun Network). Moreover, it can be seen that the number of malware events showed a sustained upward trend since 2018 Q1.
The most notable change is the number of defacement events which dropped to a record low in recent years, and only had 590 events in Q4. One of the reasons is that the top IP (103.73.66.10) in Q3, which contributed to 4,493 events, had fixed the vulnerabilities. At the same time, the URL/IP ratio of defacement decrease considerably from 8 to 2, and the number of unique defacement IPs fell by 90%, or declined to 366.
| HKCERT urges system and application administrators to protect the servers. |
|
Botnet related security events
Botnet related security events can be classified into two categories:
- Botnet Command and Control Centres (C&C) security events – involving small number of powerful computers, mostly servers, which give commands to bots
- Bots security events – involving large number of computers, mostly home computers, which receive commands from C&C.
Botnet Command and Control Servers
The trend of botnet C&C security events is summarized below:
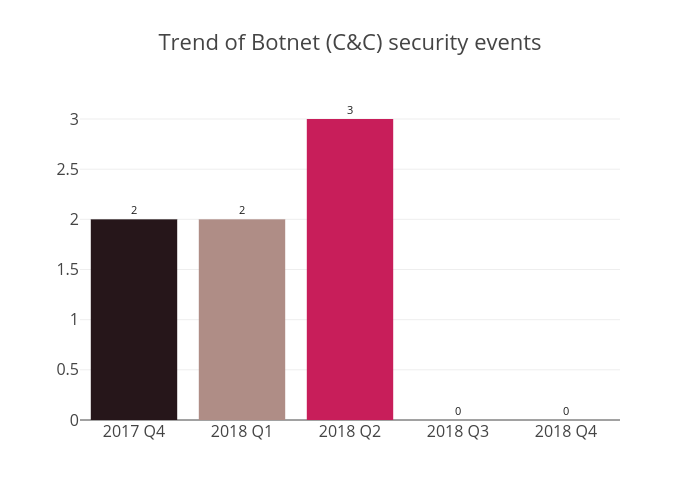 Figure 3 –Trend of Botnet (C&Cs) related security events
Figure 3 –Trend of Botnet (C&Cs) related security events
There was no Command and Control Server reported in this quarter.
The trend of botnet (bots) security events is summarized below:
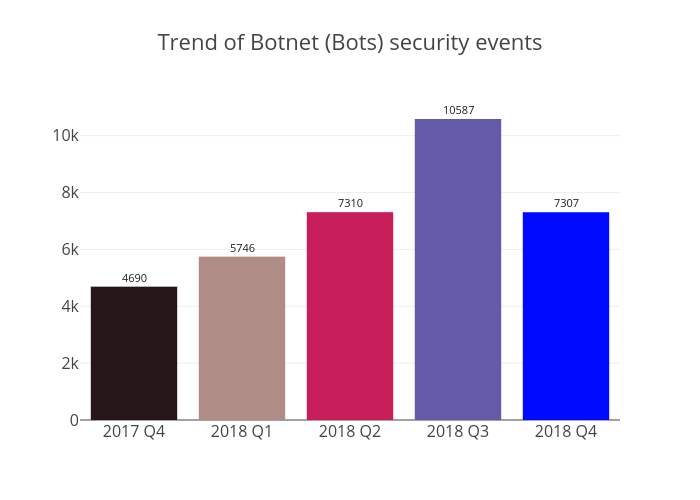 Figure 4 - Trend of Botnet (Bots) security events
Figure 4 - Trend of Botnet (Bots) security events
The number of Botnet (bots) in Hong Kong network decreased by 31% in 2018 Q4. Although the count of Mirai declined by 43%, it still keeps the first place in the rank of Major Botnet Families in Hong Kong Networks. There is a note that Ramnit has increased by 123%, with the number of unique IP address rose to 113 in 2018 Q4.
Mirai botnet became active at the end of 2016. Following our cleanup operation, we saw signicantly growth trend start from 2017 Q3 and hit the highest point at 7,205 in 2018 Q3. In 2018 Q4, despite the number of Mirai sharply dropped to 4,120, based on our record of the ports being scanned by infected IP addresses in each quarter, we see a rapidly surge for ports 23 (19,627 in 2018 Q4 compared to 3,242 in 2018 Q3) and port 2323 (2,876 in 2018 Q4 compared to 962 in 2018 Q3). Besides, Port 5555 (the default port used by Android Debug Bridge for development purpose) is still the most popular port being scanned, which reflected attackers were actively finding vulnerability to trigger attacks. HKCERT will keep monitoring the trend and continue botnet cleanup activities.
| HKCERT urges users to protect computers so as not to become part of the botnets. |
|
HKCERT has been following up the security events received and proactively engaged local ISPs for the botnet clean up since June 2013. Currently, botnet cleanup operations against major botnet family - WannaCry, Avalanche, XCode Ghost, Pushdo, Citadel, Mumblehard, Ramnit, ZeroAccess and GameOver Zeus are still in action.
HKCERT urges general users to join the cleanup acts. Ensure your computers are not being infected and controlled by malicious software.
Protect yourself and keep the cyberspace clean.
| Users can use the HKCERT guideline to detect and clean up botnets |
|
Download Report
< Please click to download Hong Kong Security Watch Report >
1 IFAS Information Feed Analysis System is a HKCERT developed system that collects global security intelligence relating to Hong Kong for analysis.
2 Refer to Appendix 1 for the Sources of Information
Share with


