Hong Kong Security Watch Report (Q2 2014)
HKCERT is pleased to bring to you the "Hong Kong Security Watch Report" for the second quarter of 2014.
Nowadays, a lot of “invisible” compromised computers are controlled by attackers with the owner being unaware. The data on these computers may be mined and exposed every day and the computers may be utilized in different kinds of abuse and criminal activities.
The Hong Kong Security Watch Report aims to provide the public a better “visibility” of the situation of the compromised computers in Hong Kong so that they can make better decision in protecting their information security.
The report provides data about the activities of compromised computers in Hong Kong which suffer from, or participate in various forms of cyber attacks, including web defacement, phishing, malware hosting, botnet command and control centres (C&C) and bots. Computers in Hong Kong is defined as those whose network geolocation is Hong Kong, or the top level domain of their host name is “.hk” or “.香港”.
Highlight of Report
This report is for Quarter 2 of 2014.
In this period, there were 16,589 unique security events related to Hong Kong used for analysis in this report. The information is collected with IFAS1 from 19 sources of information2. They are not from the incident reports received by HKCERT.
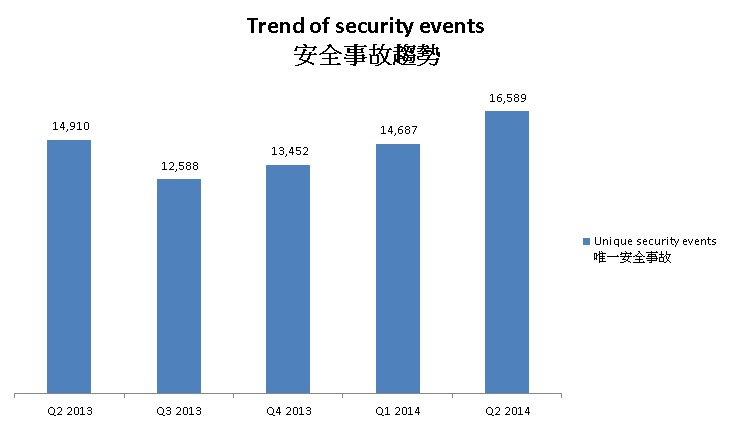
Figure 1 –Trend of security events3
Server related security events
Server related security events include malware hosting, phishing and defacement. Their trend and distribution is summarized below:
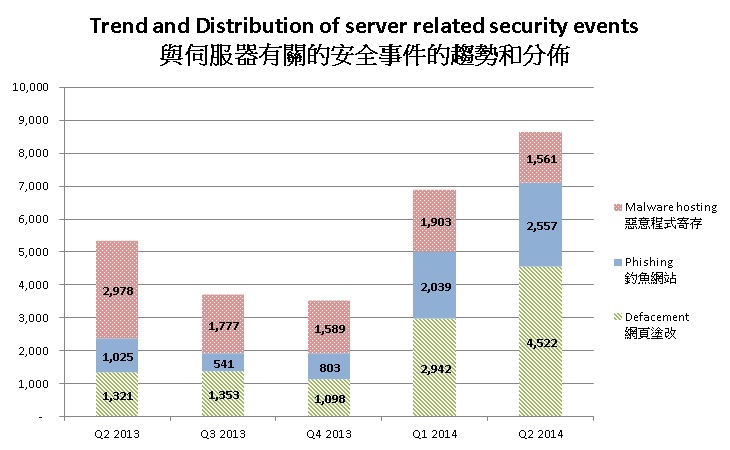
Figure 2 –Trend and distribution of server related security events distributions3
The number of server related security events moderately increased in Q2 2014.
In this quarter, the number of malware hosting security events decreased by 18% while the number of phishing and defacement increased by 25% and 54% respectively.
This quarter, the URL/IP address ratio of defacement, phishing and malware hosting security events were added to the report. The server related security events in this report used to be counted in unique URL. However, this indicator may not be able to reflect the number of compromised servers since one compromised servers can contribute to hundreds or even thousands of events. For example, in this quarter, there is a mass defacement event on one single IP address that contributed 635 URLs. The URL/IP ratio can reflect the number of mass compromise events, the higher the ratio is, the more mass compromise happened.
According to the data from Zone-H, about one third of the defacements in this quarter were attacked through known vulnerabilities. Those vulnerabilities can be removed by applying latest security patches. System and application administrators should apply the latest security patches to avoid the known vulnerabilities being exploited.
Other than that, 11% of the events were attacked by social engineering. Social engineering means tricking people to perform certain actions or provide confidential information. In order not to fall into the traps of the cyber criminals, the awareness of information security should be raised. Server administrators, web sites owners and other related parties should obtain sufficient information security training. For servers that contains sensitive data or perform critical operations, measures such as segregation of duties should be deployed to limit the damage caused by one single staff.
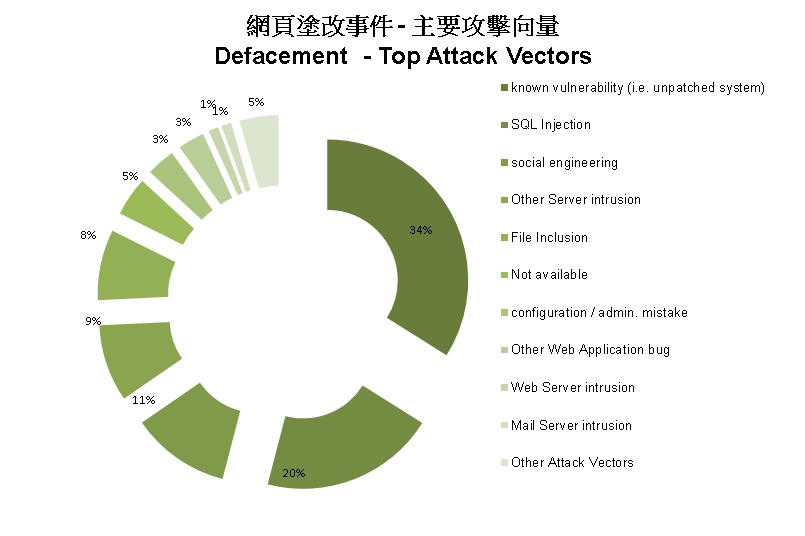
Figure 3 top attack vectors of defacements
| HKCERT urges system and application administrators to protect the servers. |
|
Botnet related security events
Botnet related security events can be classified into two categories:
- Botnet Command and Control Centres (C&C) security events – involving small number of powerful computers, mostly servers, which give commands to bots
- Bots security events – involving large number of computers, mostly home computers, which receive commands from C&C.
Botnet Command and Control Servers
The trend of botnet C&C security events is summarized below:
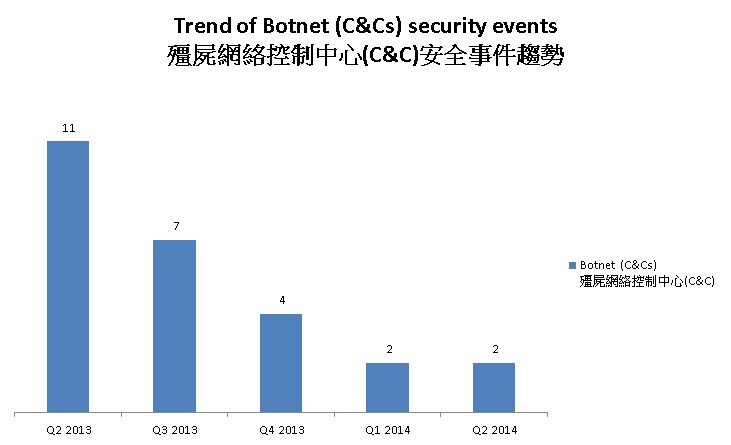
Figure 4 –Trend of Botnet (C&Cs) related security events
Number of botnet Command and Control Servers was the same as last quarter.
There were 2 C&C servers reported in this quarter. One of the reported servers were identified as Zeus C&C servers, while the other was IRC bot C&C servers.
The trend of botnet (bots) security events is summarized below:
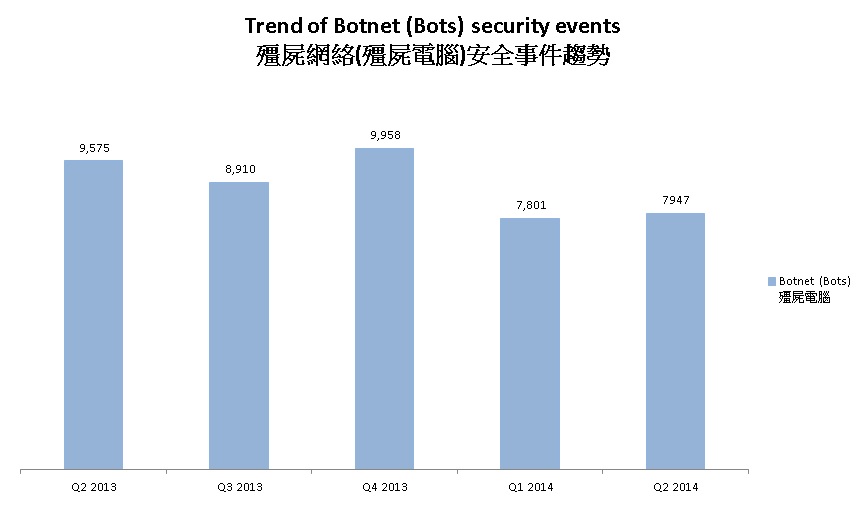
Figure 5 - Trend of Botnet (Bots) security events
Number of Botnet (bots) on Hong Kong network slightly increased in this quarter.
In Q2 2014, the number of botnet infections in Hong Kong increased by 2%, though 7 of the previous top 10 botnets have their numbers decreased or roughly unchanged.
In this quarter, Conficker remains to be the top botnet in Hong Kong. A research pointed out that the high infection rate of conficker was “attributed to the fact that a number of companies are still using Windows XP, susceptible to this threat”. It reflects that the number of computers using Windows XP is still high in Hong Kong.
The events of Zeus increased the most in the top ten botnets. It increased by 58% or 927 events. The increase of Zeus events was mainly due to a takedown operation, which caused a lot of victim IP addresses surfaced. In June, U.S. law enforcement cooperated with law enforcement of other nations and network security companies to launch a joint operation named "Operation Tovar". In the operation, the communications between the infected computers were severed, re-directing these computers away from criminal servers to sinkholes that are under the US government’s control. FBI identified the IP addresses of the victim computers that connected to the sinkholes and to provide that information to Computer Emergency Readiness Teams.
In late April, the events of Palevo botnet were recorded in IFAS for the first time. It soon grew to the fourth botnets in May and kept its rank in June. Palevo is a worm that spreads using instant messaging, P2P networks and removable drives. It opens a backdoor on the compromised computer and steals sensitive information of the victim. To stop it from further growing, all suspicious links and files should not be opened.
| HKCERT urges users to protect computers so as not to become part of the botnets. |
|
Among all the botnet family, Zeus has brought to our attention since Q4 2013. Zeus botnet security events in Oct 2013 had started to grow, and continued to soar through Q1 2014 despite a marginal drop in February 2014. It implied that Zeus botnet had been active or more users were infected with Zeus.
HKCERT has been following up the security events received and proactively engaged local ISPs for the botnet clean up since June 2013. Currently, botnet cleanup operations against
major botnet family - Pushdo, Citadel, ZeroAccess and GameOver Zeus are still in action.
HKCERT urges general users to join the cleanup acts. Ensure your computers are not being infected and controlled by malicious software.
Protect yourself and keep the cyberspace clean.
| Users can use the HKCERT guideline to detect and clean up botnets |
|
Download Report
< Please click to download Hong Kong Security Watch Report >
1Information Feed Analysis System (IFAS) is a HKCERT developed system that collects global security intelligence relating to Hong Kong for analysis.
2 Refer to Appendix 1 for the Sources of Information
3 The numbers were adjusted to exclude the unconfirmed defacement events
Share with


