Hong Kong Security Watch Report (Q1 2017)
HKCERT is pleased to bring to you the "Hong Kong Security Watch Report" for the first quarter of 2017.
Nowadays, a lot of “invisible” compromised computers are controlled by attackers with the owner being unaware. The data on these computers may be mined and exposed every day and the computers may be utilized in different kinds of abuse and criminal activities.
The Hong Kong Security Watch Report aims to provide the public a better "visibility" of the situation of the compromised computers in Hong Kong so that they can make better decision in protecting their information security.
The report provides data about the activities of compromised computers in Hong Kong which suffer from, or participate in various forms of cyber attacks, including web defacement, phishing, malware hosting, botnet command and control centres (C&C) and bots. Computers in Hong Kong is defined as those whose network geolocation is Hong Kong, or the top level domain of their host name is “.hk” or “.香港”.
Highlight of Report
This report is for Quarter 1 of 2017.
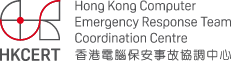
In 2017 Q1, there were 15,365 unique security events related to Hong Kong used for analysis in this report. The information is collected with IFAS1 from 19 sources of information2. They are not from the incident reports received by HKCERT.
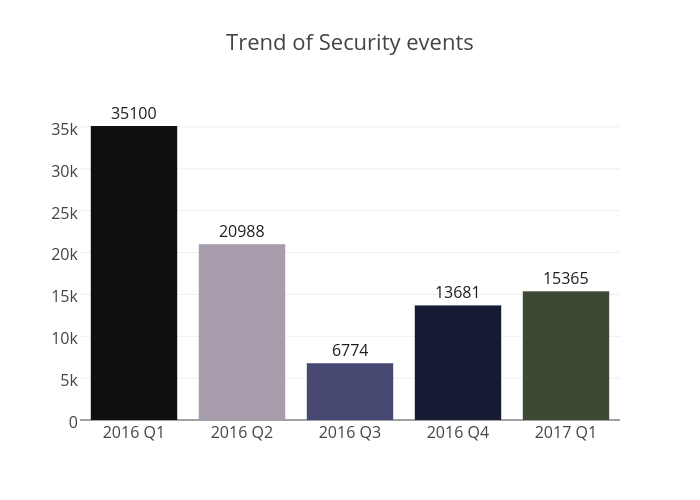
Figure 1 –Trend of security events
The total number of security events in 2017 Q1 increased by 12% or 1,684 events. The increase was mainly due to botnet events.
Server related security events
Server related security events include malware hosting, phishing and defacement. Their trends and distributions are summarized below:
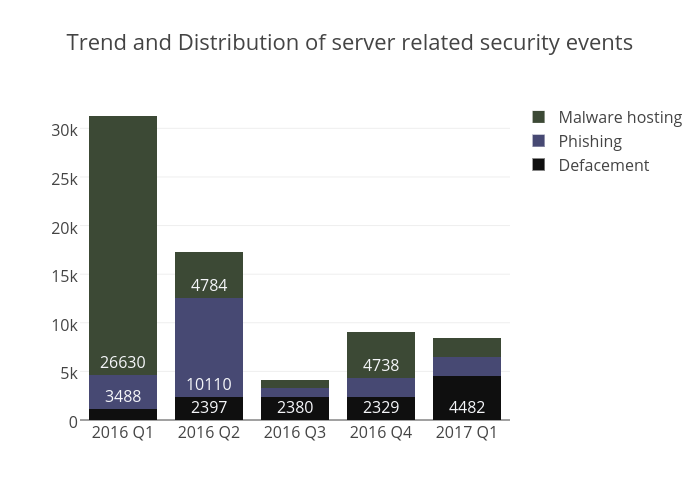 Figure 2 –Trend and distribution of server related security events
Figure 2 –Trend and distribution of server related security events
The number of server related security events decreased by 6% in Q1 2017. Phishing events and malware hosting events decreased by 5% and 59% respectively. However, the number of defacement events almost doubled.
2761 or 62% of all defacement events were from a single IP address. Most, if not all, affected domains would redirect users to an online gambling site.
According to the data from Zone-H, the server were compromised multiple times, by over 10 attack vectors, and over 20 attackers. It reflected that the server was maintained badly. Most of the attack vectors were very common, such as “known vulnerability”, “SQL Injection” and “brute force attack”.
“Known vulnerability” means the vulnerabilities that were already patched. This kind of vulnerability can be easily fixed by applying security patches. However, it is still one of the most common server vulnerabilities. HKCERT cannot emphasize more on the importance of patching. It is one of the most effective way of preventing intrusions.
“SQL Injection” is another common vulnerability. Attackers attempt to compromise the database by injecting SQL commands to various website inputs. To protect servers from SQL injections, administrators need to ensure all user inputs were filtered or properly handled before applying to the databases.
“Brute force attack” means guessing passwords or keys through a exhaustive search. Though the defacement report didn’t show what is the attack target, we found from a vulnerable system report that the server’s remote desktop (RDP) interface was open to the internet. It is possible that the attacker tried to login to the server through brute forcing the user accounts. To prevent brute force attack, strong passwords should be used in all user accounts, especially those with administrative rights. Moreover, administrators should not expose RDP and other services to the internet, unless necessary.
| HKCERT urges system and application administrators to protect the servers. |
|
Botnet related security events
Botnet related security events can be classified into two categories:
- Botnet Command and Control Centres (C&C) security events – involving small number of powerful computers, mostly servers, which give commands to bots
- Bots security events – involving large number of computers, mostly home computers, which receive commands from C&C.
Botnet Command and Control Servers
The trend of botnet C&C security events is summarized below:
 Figure 3 –Trend of Botnet (C&Cs) related security events
Figure 3 –Trend of Botnet (C&Cs) related security events
The number of botnet Command and Control Servers increased this quarter. There where 4 C&C servers reported in this quarter, which was identified as IRC bot C&C server.
The trend of botnet (bots) security events is summarized below:
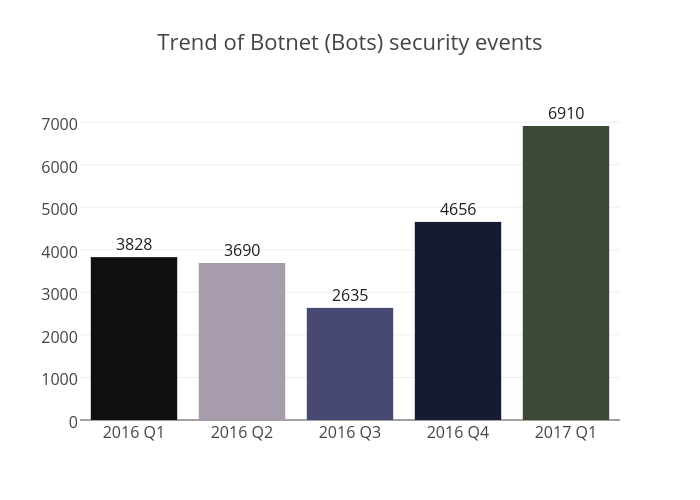 Figure 4 - Trend of Botnet (Bots) security events
Figure 4 - Trend of Botnet (Bots) security events
Number of Botnet (bots) on Hong Kong network significantly increased by 48% in this quarter. The number of Conficker events increased the most by 118.5%, and the Murofet botnet appeared in Hong Kong network for the first time.
The number of Conficker event got a sudden increase in early March. It kept at a high level for about two weeks and then started to decrease. As of the time of writing, the number of events has resumed to the level of previous quarters. We can not yet found the reason of the sudden increase. We will keep monitoring the number of Conficker closely.
Murofet is a variant of Zeus first found in mid 2010. It is a downloader that, once infected, would install other malwares from a pseudo-random generated domain name. Similar to Conflicker, it uses domain generation algorithms (DGA) technique to avoid being shutdown.
DGA are algorithms that generate a large number of domain names every day. The malware would try to resolve those domain names in order to contact the C&C server. However, only a few of them can be resolved to the real IP address of the C&C server. To cut the communication of the malware to the C&C servers, law enforcement would need to preregister a large numbers of domain names every day, which is highly inefficient. Effectively, it is not possible to take down the C&C server by taking over its domain names.
Murofet spreads by exploit kits and infected files.
| HKCERT urges users to protect computers so as not to become part of the botnets. |
|
HKCERT has been following up the security events received and proactively engaged local ISPs for the botnet clean up since June 2013. Currently, botnet cleanup operations against major botnet family - Avalanche, XCode Ghost, Pushdo, Citadel, Mumblehard, Ramnit, ZeroAccess and GameOver Zeus are still in action.
HKCERT urges general users to join the cleanup acts. Ensure your computers are not being infected and controlled by malicious software.
Protect yourself and keep the cyberspace clean.
| Users can use the HKCERT guideline to detect and clean up botnets |
|
Download Report
< Please click to download Hong Kong Security Watch Report >
1 IFAS Information Feed Analysis System is a HKCERT developed system that collects global security intelligence relating to Hong Kong for analysis.
Share with