Hong Kong Security Watch Report (Q2 2017)
HKCERT is pleased to bring to you the "Hong Kong Security Watch Report" for the second quarter of 2017.
Nowadays, a lot of “invisible” compromised computers are controlled by attackers with the owner being unaware. The data on these computers may be mined and exposed every day and the computers may be utilized in different kinds of abuse and criminal activities.
The Hong Kong Security Watch Report aims to provide the public a better "visibility" of the situation of the compromised computers in Hong Kong so that they can make better decision in protecting their information security.
The report provides data about the activities of compromised computers in Hong Kong which suffer from, or participate in various forms of cyber attacks, including web defacement, phishing, malware hosting, botnet command and control centres (C&C) and bots. Computers in Hong Kong is defined as those whose network geolocation is Hong Kong, or the top level domain of their host name is “.hk” or “.香港”.
Highlight of Report
This report is for Quarter 2 of 2017.
In 2017 Q2, there were 9,042 unique security events related to Hong Kong used for analysis in this report. The information is collected with IFAS1 from 19 sources of information2. They are not from the incident reports received by HKCERT.
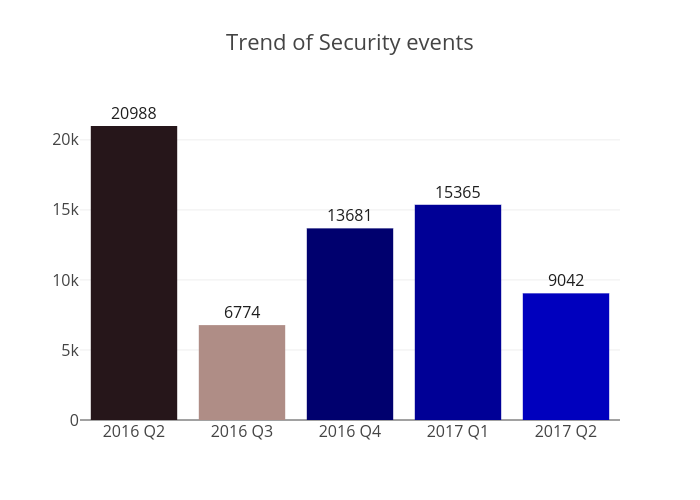
Figure 1 –Trend of security events
The total number of security events in 2017 Q2 dropped by 41% or 6323 events. The decrease was due to a rather big drop in the counts of server related security events and botnet infection.
Server related security events
Server related security events include malware hosting, phishing and defacement. Their trends and distributions are summarized below:
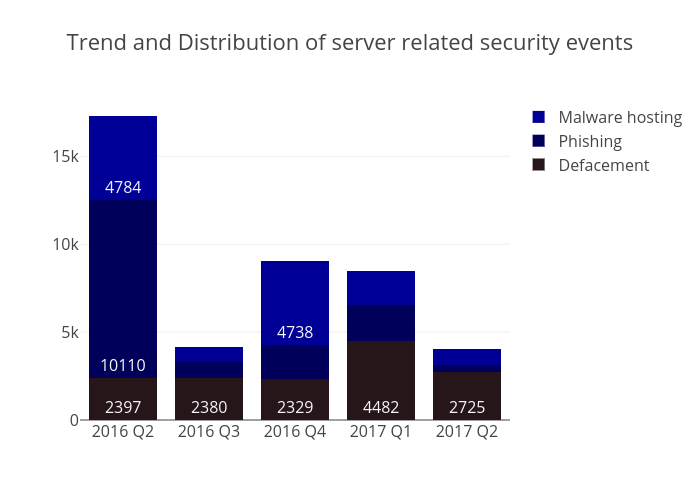 Figure 2 –Trend and distribution of server related security events
Figure 2 –Trend and distribution of server related security events
The number of server related security events substantially decreased from 8,451 to 4,015 (decreased by 52%) in this quarter. The number of defacement events decreased by 39% while the number of and malware hosting events decreased by 55%. The phishing events even recorded an all-time low of 428, which was 79% lower than the previous quarter.
Given the considerable reduction in the defacement events, the relatively low URL/IP ratio, however, reflected a fact that there were actually quite many servers compromised in the reporting period (refer to P.11 Figure 6). The same applied to the phishing events (refer to P.13 Figure 8).
| HKCERT urges system and application administrators to protect the servers. |
|
Botnet related security events
Botnet related security events can be classified into two categories:
- Botnet Command and Control Centres (C&C) security events – involving small number of powerful computers, mostly servers, which give commands to bots
- Bots security events – involving large number of computers, mostly home computers, which receive commands from C&C.
Botnet Command and Control Servers
The trend of botnet C&C security events is summarized below:
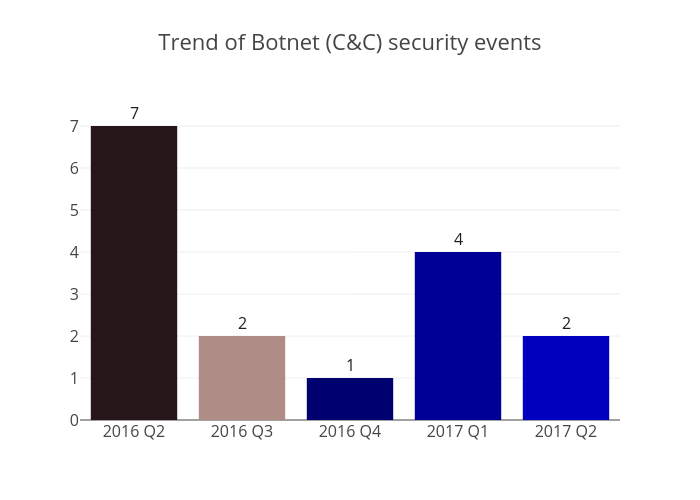 Figure 3 –Trend of Botnet (C&Cs) related security events
Figure 3 –Trend of Botnet (C&Cs) related security events
The number of botnet Command and Control Servers dropped by half to 2 in this quarter. Both were identified as IRC bot C&C servers.
The trend of botnet (bots) security events is summarized below:
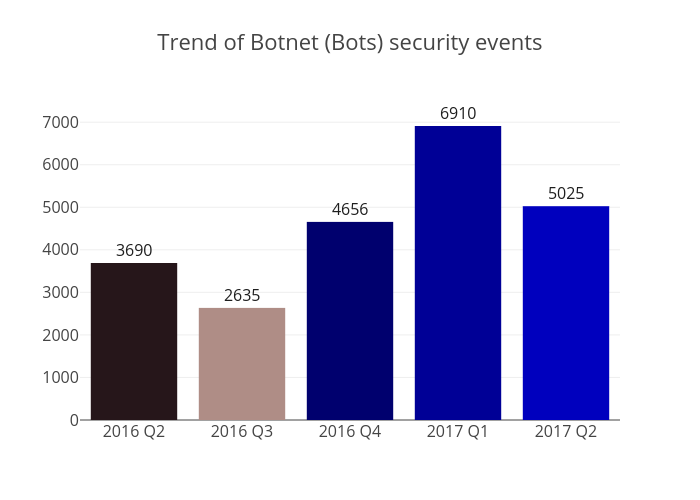 Figure 4 - Trend of Botnet (Bots) security events
Figure 4 - Trend of Botnet (Bots) security events
Number of Botnet (bots) on Hong Kong network decreased by 27% in Q2 this year.
Rank 1 was the infamous WannaCry ransomware. With a global outbreak on 12 May, it recorded a maximum connection count of 1566 unique IP addresses and a malware named Ghost Push, discovered in 2014, also made its way into HK's major botnet families in this quarter.
WannaCry
Ransomware is a type of malware which will encrypt a victim's files and demand a ransom in order to recover the files.
The 'WannaCry' variant possesses a worm's characteristic and is the first ransomware which can spread across home or office networks to infect much more devices by exploiting Microsoft Windows SMB vulnerabilities (EternalBlue and DoublePulsar). It scans for open TCP ports 139 and 445 on unpatched hosts and once detected, starts the nasty work to encrypt the files and propagate itself within the network.
Ghost Push
Ghost Push is a Android malware family discovered in 2014. Android devices get infected when a user installs a malicious app, mostly not from Google Play. Once installed, it tries to root the device and download other malicious apps. In December 2016, a mobile malware called "Gooligan" which targeted Google services was exactly a variant of Ghost Push.
| HKCERT urges users to protect computers so as not to become part of the botnets. |
|
HKCERT has been following up the security events received and proactively engaged local ISPs for the botnet clean up since June 2013. Currently, botnet cleanup operations against major botnet family - WannaCry, Avalanche, XCode Ghost, Pushdo, Citadel, Mumblehard, Ramnit, ZeroAccess and GameOver Zeus are still in action.
HKCERT urges general users to join the cleanup acts. Ensure your computers are not being infected and controlled by malicious software.
Protect yourself and keep the cyberspace clean.
| Users can use the HKCERT guideline to detect and clean up botnets |
|
Download Report
< Please click to download Hong Kong Security Watch Report >
1 IFAS Information Feed Analysis System is a HKCERT developed system that collects global security intelligence relating to Hong Kong for analysis.
Share with


