Near Field Communication Security Guidelines
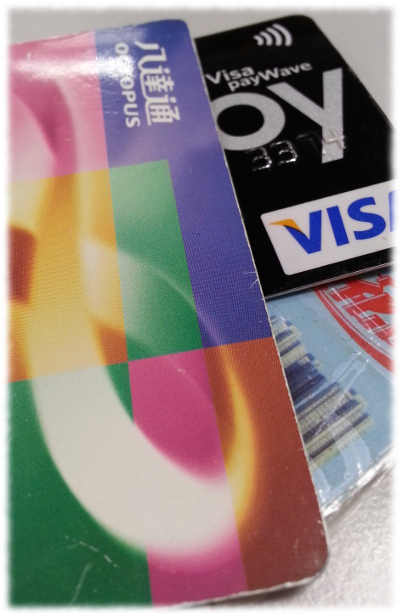
 | Near Field Communication (NFC), the name often appears in smartphone. Many electronic devices such as speakers and Bluetooth headsets also support NFC communication. In fact, NFC technology has been used since 1997 in Hong Kong in a popular payment service – the Octopus. |
Most popular Android phones have a built-in NFC transceiver which has accelerated the development of NFC applications in the recent years. As early as 2011, the use of electronic wallet on the phone to make payment via NFC has been very popular in the US. In recent years, Hong Kong has started to develop NFC payment service. Some banks and telecommunication operators cooperate to launch NFC mobile payment services. Newly issued credit cards are also NFC-enabled. Therefore, NFC will be widely used in the coming future.
NFC can be widely used because it can exchange data rapidly in wireless and has low power consumption. The transmission distance of NFC is not more than 10 centimeters which can reduce the interference that cause reading error and the risk of eavesdropping. NFC chips have different versions with storage space ranging from 96 to 4,096 bytes. There are low-speed and high-speed chips, and encryption-featured chips. The encryption function is further divided into transmission encryption and storage encryption. This provides the options for developers to apply on their products.
NFC chips are used to store the provided data; the data can be urls, codes or telephone numbers. The built-in NFC function on smartphones is for sending and receiving wireless signals and convert into data. When a smartphone read different NFC chips, it can perform different functionalities via the corresponding installed applications. For example, the chips on NFC advertising posters provide some web site information to the browser of a smartphone for surfing the product’s web site. The same applies to e-coupons, except that relevant images are downloaded when the NFC chips are scanned. Also, there are personal NFC tags which can trigger applications to operate automatically after the stored commands are read. And for e-wallet, applications provided by banks or service providers are needed to read the SIM and transmit wireless signals to the receiving device via NFC, in order to complete a transaction.
NFC brings us convenience, but increased risks on safety as well. Some of them and their prevention are discussed below:
| NFC Advertising Posters |  | |
|---|---|---|
| Use | Generally provide the web site of a product or electronic coupons. They are commonly found in MTR stations and train compartments. | |
| Risk |
| |
| Recommendation |
| |
 | NFC Tags | |
|---|---|---|
| Use | Can work with NFC applications to execute automated functions, e.g. modification of phone settings or some preset actions. | |
| Risk |
| |
| Recommendation |
| |
| NFC e-wallet |  | |
|---|---|---|
| Use | Pass the information of credit cards or prepaid cards registered by applications via NFC on the phone to make mobile payments, usually of small amounts. | |
| Risk |
| |
| Recommendation |
| |
 | Prepaid cards, credit cards and point-saving cards with NFC | |
|---|---|---|
| Use | These cards have NFC chips embedded when manufactured. They are used directly for small amount payments. | |
| Risk |
| |
| Recommendation |
| |
Various NFC applications and risks are explained above, and corresponding recommendations are also provided. Indeed, there are some common preventive measures on your phone that can help you reduce the risks:
- Disable NFC when it is not required.
- Download NFC checking tools [Note1] from Google Play store. Use the tools to verify the information being read every time.
- Keep the versions of the phone system and applications up-to-date.
- Do not download and install applications from unknown sources.
- Do not modify the phone system. [Note2]
We can enjoy the safe and convenient services brought by NFC as long as we use it more carefully.
-- End --
Note1:
NFC checking software like NFC TagReader can read the content of an NFC tag before the execution.
Note2:
Do not flash a customized system into a phone and replace the official one, and do not use specially crafted software to obtain root privilege. When the phone obtain roots privilege, hacker and all apps installed in phone can bypass security restriction that makes your phone get being attacked easily. Most customized systems provide root commands and additional functions, which may have vulnerabilities, and system may not have timely update.
Share with
