IPv6 Security Guideline for Home User
Current Internet Protocol version 6 (IPv6) situation in Hong Kong
Everyone should be familiar with the term “IP address”. It is much like a delivery address on the Internet. IPv6 is the new generation Internet Protocol. As IPv4 address allocation have already exhausted, the era of IPv6 is coming. IPv6 provides trillions of times more addresses then IPv41 and it is expected both versions of Internet Protocol will coexist on the Internet for some years.
The websites of the Hong Kong Government fully support IPv4 and IPv6 connections. Some organizations in Hong Kong start to launch IPv6 service. Major Internet Service Providers (ISP) are providing IPv6 service to their commercial customer. 2 As of Q1 of 2013, there is no ISP providing IPv6 service to residential customer. Residential user can only use workaround method like IPv6 Tunnel over IPv4 or IPv6 Proxy to connect to IPv6 network.3
Common misunderstanding of IPv6
IPv6 is faster than IPv4
Using IPv6 will not speed up your connection, connection speed is determined by the bandwidth provided by your ISP and users should not be aware of any difference between IPv4 and IPv6.
IPv6 is more secure than IPv4
Although IPv6 was designed with security in mind and built in security features, some features are not enabled by default. To fully utilize the security feature on both protocols, you require a qualified network engineer to design and implement the network.
General Home Network architecture
Let us look at the difference between IPv4 and IPv6 network connection in a typical home environment via IPv6 Tunnel.
Figure 1 shows general IPv4 network connection using broadband router. The PC connects to the Internet via broadband router and broadband router will filter out all traffics initiated from the Internet.
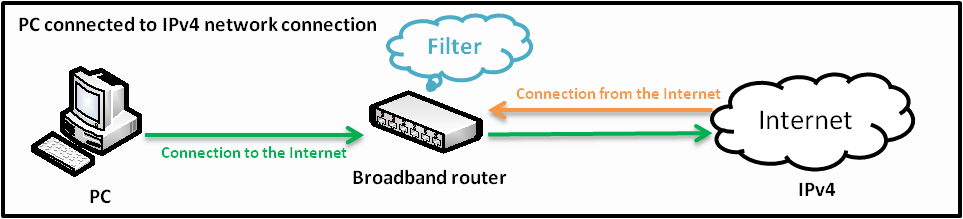
Figure 1
Figure 2 shows IPv6 connection via Tunnel Broker. 3 When the PC connects to IPv6 Internet network via Tunnel Broker, all IPv6 devices on the Internet can bypass the IPv4 NAT firewall of the broadband router and directly connect to the PC.
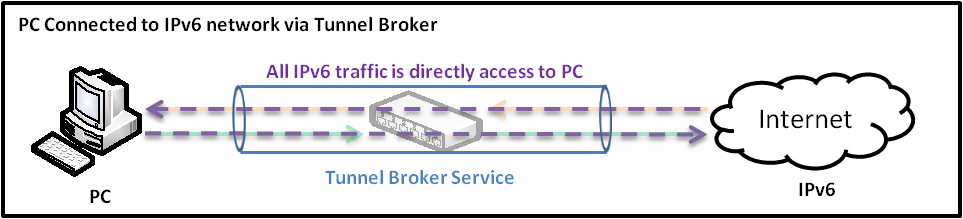
Figure 2
Security Risks on different situation
- Connect to IPv6 network
- As tunnel broker is the only way for home user to connect to the IPv6 network, all data connection will go through the tunnel broker and the data may be captured during transit.
- If your PC connect to IPv6 network using broadband router as shown on Figure 2. All IPv6 devices on the Internet can bypass IPv4 filtering for the broadband router and directly access to your PC.
Solution
- If you need to transfer sensitive and personal data, use encryption technologies, for example: use SSL enabled websites and email communication.
- Use personal firewall which fully supports IPv6. 4 After installation and configuration of personal firewall, use online inspection website to verify if the personal firewall is configured properly. 5
- Not connect to IPv6 network.
- By default, some systems will automatically connect to IPv6 network such as auto configure and Teredo tunneling feature. User may not be aware they are connected to IPv6 network. As mentioned above, your PC may be exposed on IPv6 network
- Check and disable IPv6 default setting.6 By default IPv6 auto configuration is enabled on Window and Mac OS and disabled on some Linux distribution. You can follow the instruction in the Appendix to enable or disable IPv6.7
- Use personal firewall and configure it to deny all IPv6 connection.
Solution
Appendix:
- Reference Link
IPv6 Summit, Inc
http://www.usipv6.com/what_is_ipv6.php
Consumer Guide from IPv6Now
http://www.ipv6now.hk/imgShow/IPv6_Consumer_Guide_En.pdf
- Hong Kong IPv6-enabled Website Directory
http://www.ipv6now.hk/en/Resources.php
http://www.ipv6forum.com/ipv6_enabled/approval_list.php?type=loc&content=HK
- Other browsing method
- IPv6 proxy website
- Reference of IPv6 tunnel broker
You may use the IPv6 Proxy website http://www.ipv6proxy.net to visit IPv6 website, if you are unable to connect to IPv6 network but willing to experience it. To avoid information disclosure, do not enter sensitive personal data because it is using proxy server to browse website.
Hurricane Electric Tunnel Broker
http://www.he.netFreenet6 Tunnel Broker
http://www.gogo6.com/Teredo Tunnel
http://yorickdowne.wordpress.com/2008/01/26/ipv6-at-home-part-1-overview-teredo/
Teredo for Mac OS X
http://www.deepdarc.com/miredo-osx/
Miredo: Teredo IPv6 tunneling for Linux and BSD
Other IPv6 tunnel brokers
- Selection criteria on Personal firewall
- Able to control and define firewall policy for specific IPv4 and IPv6 connection.
- Able to record all activity of IPv4 and IPv6, including source and destination IP address, time and port number.
- Online inspection website
Tim’s Online IPv6 TCP/UDP Port Scanner (IPv6 Firewall Tester)
http://ipv6.chappell-family.com/ipv6tcptest/
After the online inspection, you can check the firewall log and make sure the connection from online inspection website was blocked and recorded on log file.
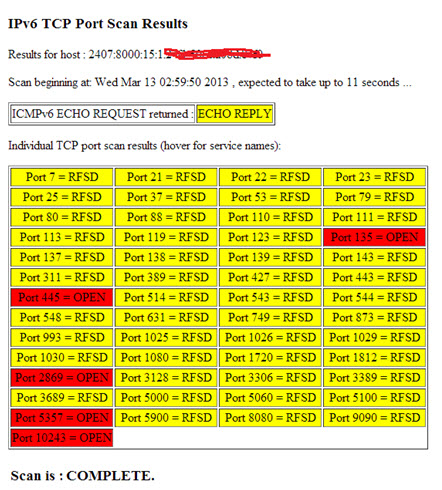
Test result below showed that TCP port 135, 445, 2869, 5357 and 10243 were listening, which means that your personal firewall is unable to block incoming connections.
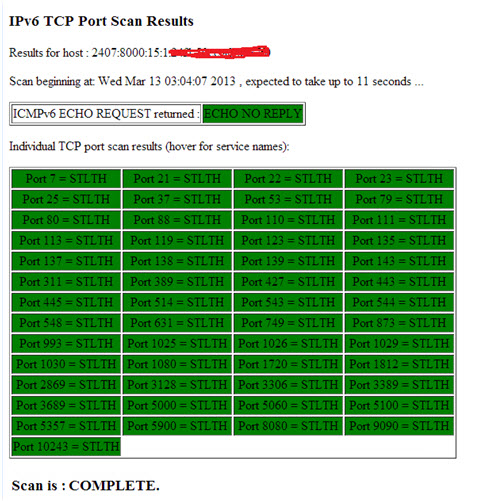
Test result below showed that the all connection was blocked, which means that your personal firewall functioning properly and is able to block incoming connections.
- How to check whether you are connected to IPv6 network?
- Use of Command Prompt
- Use of online inspection website
If you are Windows user, enter “ping -6 ipv6.google.com” in command prompt.
If it returns “Reply from 2404::6800::4005:803::1011: time=xxx ms”, then you are connected to IPv6 network.
If it returns “Ping request could not find host ipv6.google.com. Please check the name and try again”, then you are not connected to IPv6 network.
If you are Mac or Linux user, enter “ping6 ipv6.google.com” in the terminal.
You can visit http://test-ipv6.com/ to check your IPv6 connectivity.
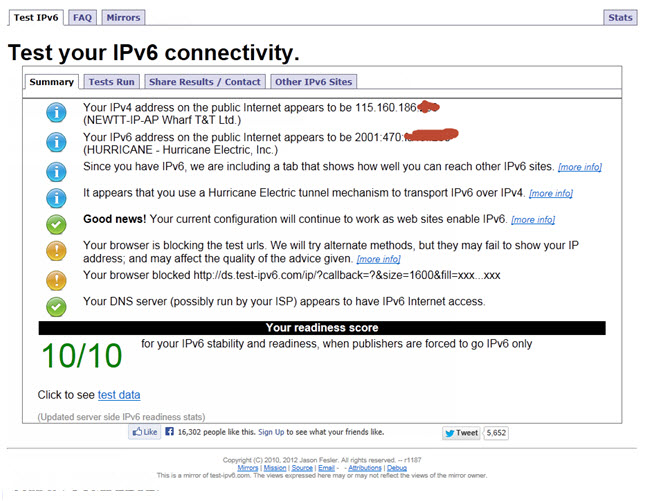
Above figure “10/10” indicates you have connected to IPv6 network.
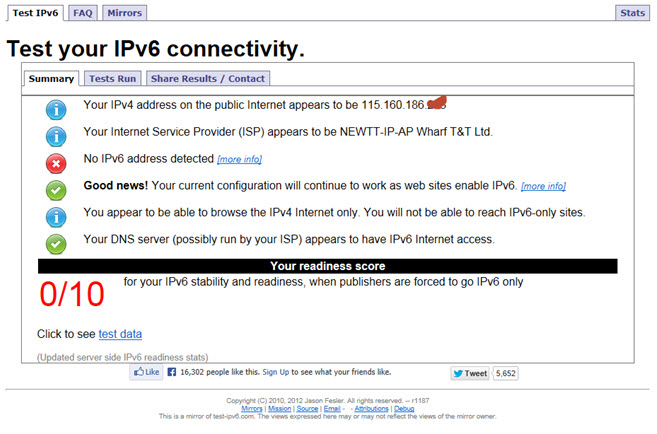
Above figure “0/10” indicates you are not able to connect to IPv6 network.
- How to disable IPv6 system default settings
- Windows User
- Mac User
- Linux User
How to disable IP version 6 or its specific components in Windows.
http://support.microsoft.com/kb/929852/en-us
Configuring IPv6 in Mac OS X v10.6.7 or later.
http://support.apple.com/kb/HT4667?viewlocale=en_US&locale=en_US
How do I disable or enable the IPv6 protocol in Red Hat Enterprise Linux? (Red Hat Linux)
https://access.redhat.com/site/solutions/8709
How do I disable IPv6? (Centos 5.x)
http://wiki.centos.org/FAQ/CentOS5#head-47912ebdae3b5ac10ff76053ef057c366b421dc4
How do I disable IPv6? (Centos 6.x)
http://wiki.centos.org/FAQ/CentOS6#head-d47139912868bcb9d754441ecb6a8a10d41781df
WebBrowsingSlowIPv6IPv4 (ubuntu)
Share with
