CryptXXX Ransomware Encrypts Victim Data
Last Update Date:
7 Jun 2016
Release Date:
3 Jun 2016
10983
Views
RISK: Extremely High Risk
TYPE: Attacks - Malware

A ransomware known as CryptXXX has been spreading quickly through compromised websites. HKCERT has received several CryptXXX infection reports from victims since mid-May 2016.
How CryptXXX was spread
- Compromised website: Most victims were infected by visiting compromised websites. Those websites mainly targeted users with outdated or unpatched browser (e.g. IE) or plugins (e.g. Flash Player).
- Banner ads: We also observed that some banner ads loaded in normal website may also be able to cause user device infected.
Impact
- CryptXXX encrypts files on victims’ computers and adds a .crypt, .crypz or .cryp1 file extension to them.
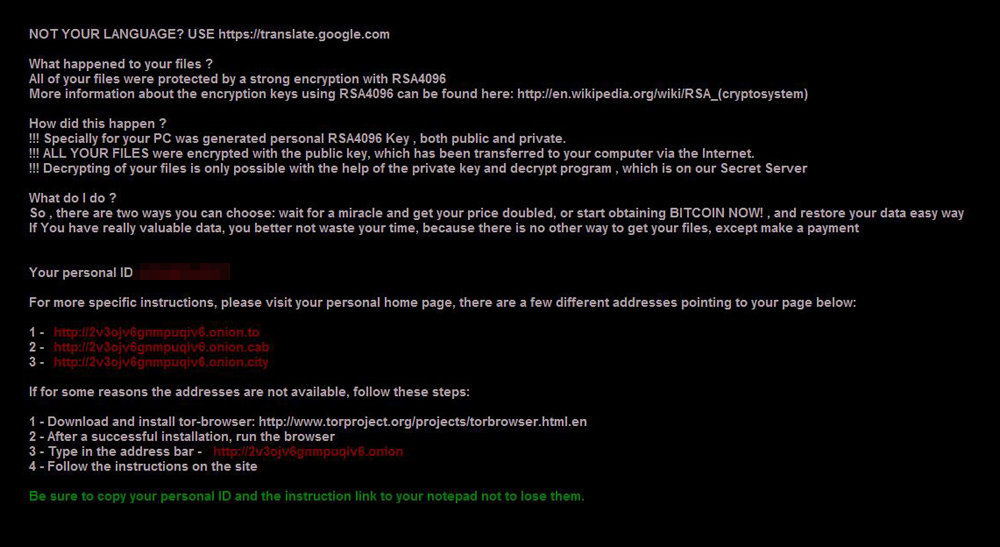
- The desktop background will be changed to ransom request image, like the following (courtesy of Trend Micro):
- Files on network drives and cloud service (e.g. Dropbox, Google Drive, One Drive) are also affected.
- Data will be unrecoverable due to encryption by ransomware.
System / Technologies affected
- Windows platform
Solutions
To handle infected devices:
- Once infected, isolate the infected computer from the network and external storage immediately. Do not open any file before clearing the malware.
- We do not recommend paying the ransom.
To decrypt files:
Some anti-virus vendors have provided decryptor for decrypting files. Depending on the version/variant of CryptXXX, it is NOT guaranteed that these decryptors could recover all of the encrypted files.
- Note before using decryptor:
- Before running any software, please visit the vendor website for more details.
- Please isolate the infected device so that it would not affect other shared folders or file servers during decryption.
- Please refer to 'Claimed decryptor for files encrypted by CryptXXX ' in the following article for the information of the decryptor:
/my_url/blog/15050402#decryption
To protect yourself from ransomeware:
- The risk of infection through visiting website can be minimized by applying updated security patch on OS and software including plugins. You may also consider to uninstall software not needed any more.
- Stop using any end of support softwares (e.g. Windows XP) since there is no security patch released for them.
- Always keep your security software up to date.
- Regularly backup the files stored on your computer, and keep an offline copy of the backup.
- Delete any suspicious-looking emails you receive, especially if they contain links or attachments.
- Be extremely wary of any Microsoft Office email attachment that advises you to enable macros to view its content. Do not enable it if in doubt.
Vulnerability Identifier
- No CVE information is available
Related Link
- /my_url/blog/15050402
- https://blog.malwarebytes.org/cybercrime/2016/05/new-wave-of-malvertising-leverages-latest-flash-exploit/
- http://blog.trendmicro.com/trendlabs-security-intelligence/will-cryptxxx-replace-teslacrypt-ransomware-shakedown/
- http://blog.checkpoint.com/2016/05/27/cryptxxx-simple-evasive-effective/
- https://www.proofpoint.com/us/threat-insight/post/cryptxxx2-ransomware-authors-strike-back-against-free-decryption-tool
Share with
