Ransomware Evolved: Double Extortion and Fake Decryptor
Ransomware is among the most detrimental and wide-spread cyber security threats. Hackers are using it to encrypt files on the user's device and demand ransom payments for file decryption.
HKCERT has been continually monitoring ransomware trends, providing security advice to users. In the end of last year, it published a security blog titled “New Trends of Ransomware”, analysing seven relatively common ransomware families and ransomware trend at that time.
Six months have passed with continued innovation in the attack tactic of ransomware threat actors being observed. In this blog post, two major trends in ransomware attack tactics, namely double extortion and fake decryptor, will be analysed.
1. Double Extortion
Performing regular backup and keeping it offline have been effective methods to safeguard critical data against ransomware threats. If a system is unfortunately locked by ransomware, users can recover their data from offline backup to resume operation.
Given the effectiveness of these measures, ransomware gangs have started to use a new tactic, double extortion, to increase the chance of getting paid.
Prior to encrypting the victim’s databases, the attackers would extract a large quantity of sensitive information, and request their victim to pay ransom. If the victim ignores ransom demands, some of the attackers will threaten to post the stolen information on the Internet to put additional pressure on their victims to pay the ransom. In other cases, instead of leaking data, some ransomware gangs might auction it for highest illegal return.
In the past 6 months, a rise of ransomware attacks targeting high-profile companies which hold a large number of sensitive data has been observed. In Hong Kong, a large retail company[1] has encountered double extortion ransomware. Below are the two most active ransomware gangs using this tactic.
1.1. Maze Ransomware
The first reported case of double extortion tactic was used by Maze ransomware gang in November 2019. Then they threatened a large American security staffing company [2] to upload 5GB of its sensitive data on their dedicated data-leaking site if ransom is not paid. Maze ransomware gang actively attacks and collaborate with other ransomware gangs, namely the Lockbit gang and the Ragnar Locker gang, by publishing data stolen from other ransomware gangs.
The Maze ransomware gang would first target managed service providers (MSPs) before extending their claws to clients of MSPs. Maze ransomware attacks involve leveraging phishing emails as well as brutal force attacks on remote desktop service. Once gaining initial access to target systems, attacks would follow by using remote shells, Windows Remote Management, to weaken the security control by modifying Group Policy in Active Directory, exfiltrate sensitive data, and deploy the ransomware.
1.2. REvil (Sodinokibi) Ransomware
REvil (also known as Sodinokibi) was analysed in one of the previous blogs. In early June, the operators behind REvil began auctioning data that claimed to be stolen from an agricultural company, and threatened more victims would face the same fate. The move not only marks an escalation in tactics aimed at coercing victims to pay up, but may also signal that ransomware gangs are searching for new ways to profit from their crimes. Victims might suffer attack from another attack operators who bid leaked data in the auctions. For instance, attackers can conduct target phishing attacks on victims by using the leaked information.
2. Fake Decryptor
Searching for available decryptor might be the first attempt to recover data by victims whose device is encrypted by ransomware. Meanwhile, it should be aware of traps during searching. Recently, a fake decryptor called STOP Djvu Ransomware has been distributed to lure victims with the promise of free decryption. However, the fake decryptor actually infects the system with another ransomware that makes the situation even worse while no data can be recovered.
2.1. Zorab Ransomware
Zorab is a ransomware pretending the STOP Djvu decryptor. When a victim enters their information in the phony decryptor (as Fig.1) and clicks on “Start Scan”, the program will extract a Zorab executable to encrypt the data and add the extension ".ZRB" to files in the computer. The ransomware will create ransom notes named '--DECRYPT--ZORAB.txt' in each folder where files are encrypted. This note contains instructions on how to contact the ransomware operators for payment instructions.
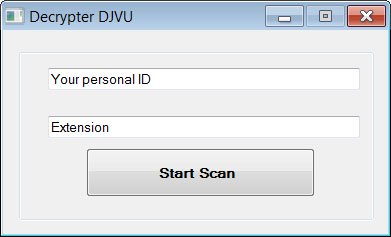
Fig.1 Fake STOP Djvu decryptor
The good news is that Emsisoft has released a decryptor for Zorab. The victims whose device is locked by Zorab could download it in below link:
https://www.emsisoft.com/ransomware-decryption-tools/zorab
3. Security Advice
From the latest trend of ransomware, it can be seen that protecting the digital assets from being compromised is the most important method to against ransomware. For the sake of reducing the risk of ransomware infection, enterprises and general users should take precautionary security measures. Especially for enterprises, there is a high risk of leakage of sensitive data when infected with ransomware. As such, enterprises must stay vigilant and pay extra attention to ransomware attacks.
For enterprises, we advise them to:
- Minimise the number of users who have domain administrative rights to confine the scope and impacts in case of an attack, and use general account in daily operation.
- Implement endpoint security protection platforms which can inspect emails for malicious payloads, prevent malicious encryption programs, and uncover endpoint vulnerabilities to deflect ransomware attacks.
- Build data privacy policy, and encrypt sensitive data and set corresponding password policies and keep encrypt keys in isolation.
- Conduct a data security plan which should focus on collecting only the required data information, keeping it safe and destroying any information that is no longer needed.
- Regularly conduct cybersecurity drills and trainings to improve employees' security awareness, such as educating employee beware of phishing emails and fake decryptors .
- Build incident responds policy about how to handle ransomware incident and data leakage.
For normal users, we advise them to:
- Be aware of suspicious emails. Do not open attachments inattentively, especially compressed files (zip), executable files (exe) or documents that contain the VBS script.
- Install security programmes and keep related security signatures up-to-date.
- Update system and software, such as Microsoft Windows, Office, Adobe reader, Flash player, etc., with the latest security patch to plug the security loopholes and avoid being utilised by malwares.
In addition to preventing infection by ransomware, enterprises and users should also make backups. We advise them to:
- Backup important files in a timely and regular manner. Keep an offline copy of the backups in a safe place to avoid being affected by malwares.
- Make sure that the cloud service provider has “version history” function when using cloud backup service. It can help recover the previous version of a file, even though the affected file has been synchronised to the cloud.
Meanwhile, if your device is infected by ransomware, we recommend taking the following measures:
- First, offline the infected computer to avoid malwares from further affecting files in the Intranet.
- Copy the encrypted files to an empty storage device.
- Use a clean computer to download legitimate decryption tool to decrypt files. Do not download suspicious decryptor from untrusted source.
- If the system or data has been backed up before being infected by malwares, users can restore the system and data from the backups.
- Refer to the “Ransomware Decryption Guideline” compiled by HKCERT for decryption.
- Contact HKCERT for enquiry or assistance.
*You can identify ransomware and download decryption tools from the website below. HKCERT makes no guarantee of the tools for successful recovery of the files. *
https://www.nomoreransom.org/en/index.html
4. Reference
- https://cyware.com/blog/live-updates-maze-ransomware-attacks-5bce
- https://research.checkpoint.com/2020/ransomware-evolved-double-extortion/
- https://www.bankinfosecurity.com/10-ransomware-strains-being-used-in-advanced-attacks-a-14199
- https://www.bankinfosecurity.com/7-ransomware-trends-gangs-join-forces-decryptors-improve-a-14401
- https://www.bleepingcomputer.com/news/security/maze-ransomware-adds-ragnar-locker-to-its-extortion-cartel/
- https://www.bleepingcomputer.com/news/security/fake-ransomware-decryptor-double-encrypts-desperate-victims-files/
- https://www.bankinfosecurity.com/unwanted-escalation-ransomware-attackers-leak-stolen-data-a-13438
Share with
