An aggressive campaign of Locky ransomware
An aggressive campaign of a new ransomware Locky is observed. Locky became active since February 2016. It encrypts files found on victims’ computers or network shares and adds a ".locky" file extension to them. Because strong encryption algorithms (RSA and AES) were used, infected files became practically unrecoverable. Locky display a ransom note in local language, demanding a ransom of 0.5 to 1 bitcoin (1 bitcoin = approximately HKD 3,200) in exchange of the decryption keys (See Figure 1).
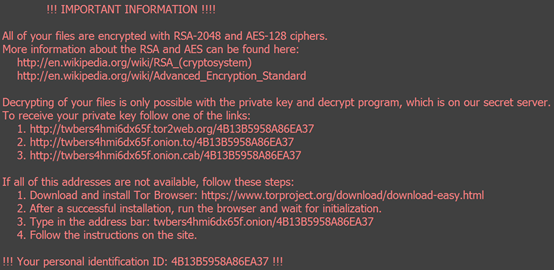
Figure 1. Locky displays the ransom note in localized language as wallpaper
Locky ransomware in the wild
Cyber criminals are aggressively pushing Locky through global spam campaign and massive compromised websites. Locky is spreading very fast on the Internet. As of March 18, HKCERT received 18 reports of Locky ransomware, with 11 received in the past two days. The victims included SMEs and non-government organizations. From the outreach to education sector we believe there should be many more unreported cases.
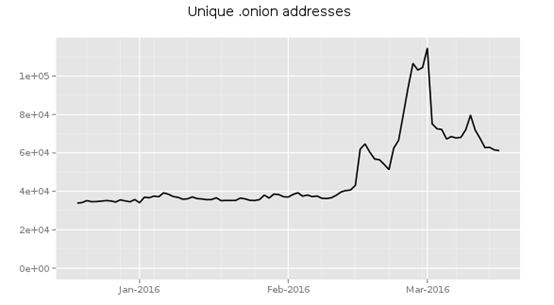
Locky’s bitcoins ransom collection website is the same as that of some other ransomwares. It is hidden inside the Tor network. A possible evidence of rapid growth of the malware is reflected in the sharp rise in unique .onion address used for Tor’s hidden services (Known as .onion sites) for illegal purposes (see Figure 2).
Global spam campaign
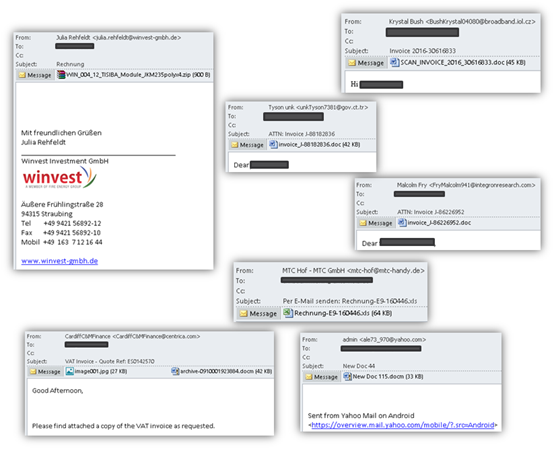
One main path of infection is through spam email campaign. Many of the scam messages disguise as invoices or payment voucher (see Figure 3). The senders were from the victims’ email domain or unknown senders.
Distributed via Massive Compromised Website
Features making Locky dangerous
Mitigating Risks of Locky Malware
- Delete any suspicious-looking emails you receive, especially if they contain links or attachments.
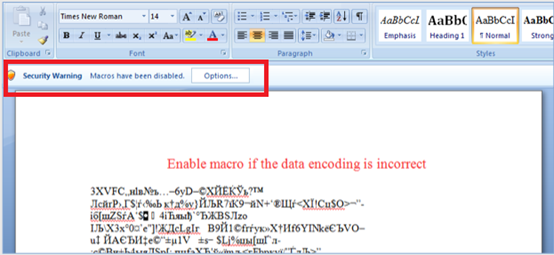
- Be extremely wary of any Microsoft Office email attachment that advises you to enable macros to view its content. Do not enable it if in doubt.
- Regularly backup the files stored on your computer, and keep an offline copy of the backup.
- Always keep your security software up to date.
- Keep your operating system and other software updated.
- Once infected, isolate the infected computer from the network and external storage immediately. Do not open any file before clearing the malware.
- We do not recommend paying the ransome.
Reference
Share with
