Risk Level Description
Security Bulletins are classified into different risk levels. It is based on the initial assessment of the potential impact of the security vulnerabilities and the actual status of exploit attacks in the real world. In general, security vulnerabilities may cause different levels of impact on the target systems. Some examples are listed below, but the list is not intended to be exhaustive.
- Low impact such as spoofing and cross site scripting.
- Medium impact such as elevation of privilege, security restriction bypass, information disclosure and data manipulation.
- High impact such as denial of service and execution of arbitrary code on the targeted system.
Below is the risk level classification table:
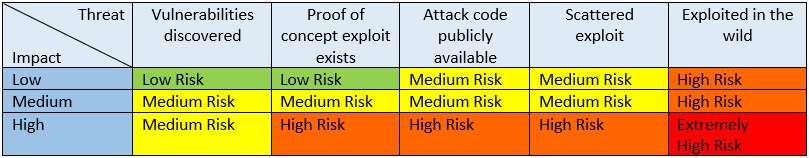
Low Risk
Typically used by security vulnerabilities which may cause low impact on the target systems. At the time of disclosure, the security vulnerabilities satisfy either one of the following situations:
- Vulnerabilities have just been discovered; or
- Proof of concept (PoC) exploit exists.
Remark:
To retain the public focus more on medium or higher risk level, HKCERT does not publish security bulletin of this level unless the security bulletin notably have the need to draw public's attention.
Medium Risk
Security vulnerabilities are classified as medium risk if it satisfies either one of the following conditions.
- Typically used by security vulnerabilities which may cause low impact on the target systems. At the time of disclosure, the security vulnerabilities satisfy either one of the following situations:
- Attack code is publicly available; or
- The vulnerabilities are being used in scattered exploit.
- Typically used by security vulnerabilities which may cause medium impact on the target systems. At the time of disclosure, the security vulnerabilities satisfy either one of the following situations:
- Vulnerabilities have just been discovered; or
- PoC exploit exists; or
- Attack code is publicly available; or
- The vulnerabilities are being used in scattered exploit.
- Typically used by security vulnerabilities which may cause high impact on the target systems. At the time of disclosure, the vulnerabilities have just been discovered.
High Risk
Security vulnerabilities are classified as high risk if it satisfies either one of the following conditions.
- Typically used by security vulnerabilities which may cause low or medium impact on the target systems. At the time of disclosure, the vulnerabilities are actively exploited in the wild.
- Typically used by security vulnerabilities which may cause high impact on the target systems. At the time of disclosure, the security vulnerabilities satisfy either one of the following situations:
- PoC exploit exists; or
- Attack code is publicly available; or
- The vulnerabilities are being used in scattered exploit.
Extremely High Risk
Typically used for security vulnerabilities which may cause high impact on the target systems. At the time of disclosure, the vulnerabilities are actively exploited in the wild.
Other considerations:
In addition to the general conditions stated above, Hong Kong Computer Emergency Response Team Coordination Centre (HKCERT) may make adjustment to the risk level based on other factors, which may not be described in the above description. The other factors include, but not limited to, social impact, the special condition required on exploiting the vulnerabilities (e.g. user interaction, user authentication and permission, etc.), availability of patch, impact on critical infrastructure, and taking full control on targeted system.
Disclaimer:
Hong Kong Computer Emergency Response Team Coordination Centre (HKCERT) and Hong Kong Productivity Council ( HKPC ) reserves the right to amend the risk level description from time to time without prior notice. HKCERT and HKPC reserve the right to make adjustment to the assessment rating, which may not be described in the above risk level description.
While we have made every attempt to ensure that the information contained in this website has been obtained from reliable sources, HKCERT is not responsible for any errors or omissions, or for the results obtained from the use of this information. All information in this website is provided "as is", with no guarantee of completeness, accuracy, timeliness or of the results obtained from the use of this information, and without warranty of any kind, express or implied, including, but not limited to warranties of performance, merchantability and fitness for a particular purpose.
The information contained in this website is intended to provide general information and for reference only. Reliance or use of this information shall be at the reader’s own risk. Nothing herein shall to any extent substitute for the independent investigations and the sound technical and business judgment of the reader. In no event will HKCERT, HKPC or its partners, employees or agents, be liable to you or anyone else for any decision made or action taken in reliance on the information in this website, or for any consequential, special or similar damages, even if advised of the possibility of such damages.
For the old severity level, please press here.
Reviewed date: 2019-08-06