相關新聞
Ransomware Attacks Exploit VMware ESXi Vulnerabilities in Alarming Pattern
Ransomware attacks targeting VMware ESXi infrastructure following an established pattern regardless of the file-encrypting malware deployed. [...]
The Hacker News
2024年05月24日 197 觀看次數

GHOSTENGINE Exploits Vulnerable Drivers to Disable EDRs in Cryptojacking Attack
Cybersecurity researchers have discovered a new cryptojacking campaign that employs vulnerable drivers to disable known security solutions (EDRs) and thwart detection in what's called a Bring Your Own Vulnerable Driver (BYOVD) attack.
The Hacker News
2024年05月23日 280 觀看次數

Critical Bug Allows DoS, RCE, Data Leaks in All Major Cloud Platforms
An on-by-default endpoint in ubiquitous logging service Fluent Bit contains an oversight that hackers can toy with to rattle most any cloud environment.
Dark Reading
2024年05月21日 263 觀看次數

QNAP QTS zero-day in Share feature gets public RCE exploit
An extensive security audit of QNAP QTS, the operating system for the company's NAS products, has uncovered fifteen vulnerabilities of varying severity, with eleven remaining unfixed. [...]
Bleepingcomputer
2024年05月20日 158 觀看次數

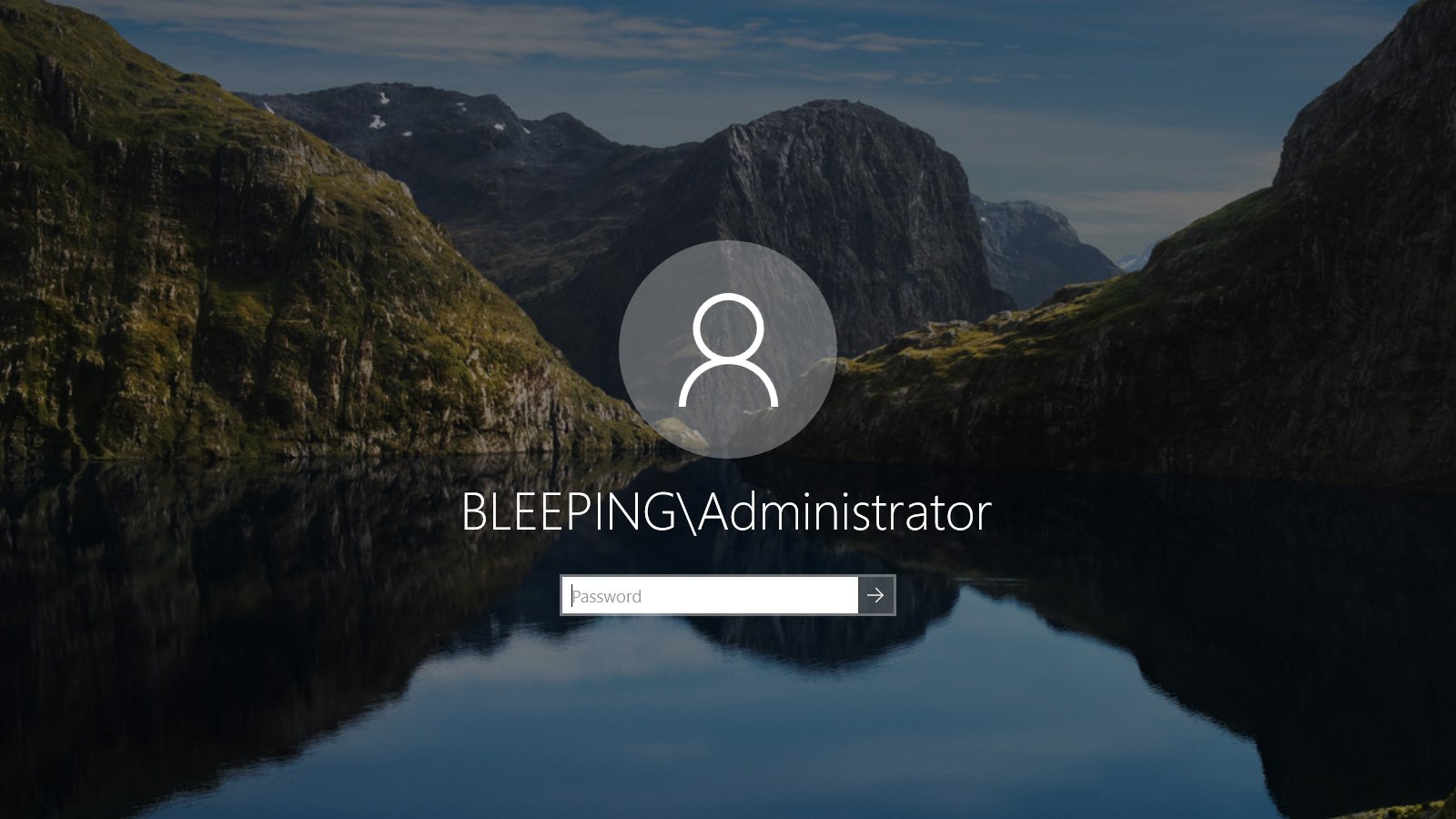
Ransomware gang targets Windows admins via PuTTy, WinSCP malvertising
A ransomware operation targets Windows system administrators by taking out Google ads to promote fake download sites for Putty and WinSCP. [...]
Bleepingcomputer
2024年05月19日 204 觀看次數
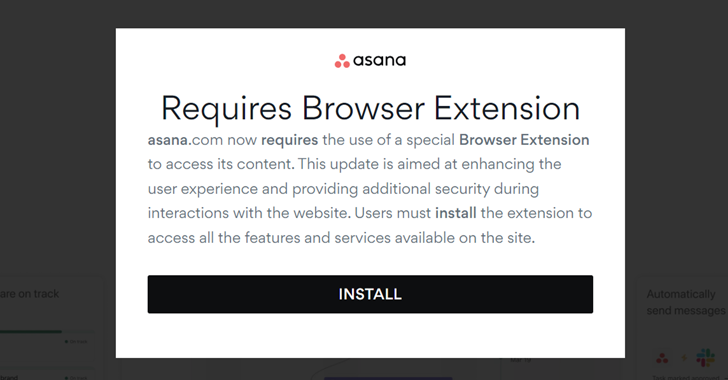
FIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
The financially motivated threat actor known as FIN7 has been observed leveraging malicious Google ads spoofing legitimate brands as a means to deliver MSIX installers that culminate in the deployment of NetSupport RAT. [...]
The Hacker News
2024年05月11日 192 觀看次數
Citrix warns admins to manually mitigate PuTTY SSH client bug
Citrix notified customers this week to manually mitigate a PuTTY SSH client vulnerability that could allow attackers to steal a XenCenter admin's private SSH key. [...]
Bleepingcomputer
2024年05月10日 155 觀看次數

New attack leaks VPN traffic using rogue DHCP servers
A new attack dubbed "TunnelVision" can route traffic outside a VPN's encryption tunnel, allowing attackers to snoop on unencrypted traffic while maintaining the appearance of a secure VPN connection. [...]
Bleepingcomputer
2024年05月08日 276 觀看次數

Billions of Android Devices Open to 'Dirty Stream' Attack
Microsoft has uncovered a common vulnerability pattern in several apps allowing code execution; at least four of the apps have more than 500 million installations each; and one, Xiaomi's File Manager, has at least 1 billion installations.
Dark Reading
2024年05月03日 246 觀看次數

CISA says GitLab account takeover bug is actively exploited in attacks
CISA warned today that attackers are actively exploiting a maximum-severity GitLab vulnerability that allows them to take over accounts via password resets. [...]
Bleepingcomputer
2024年05月02日 204 觀看次數

