
CISA warned today that attackers are actively exploiting a maximum-severity GitLab vulnerability that allows them to take over accounts via password resets.
GitLab hosts sensitive data, including proprietary code and API keys, and account hijacking can have a significant impact. Successful exploitation can also lead to supply chain attacks that can compromise repositories by inserting malicious code in CI/CD (Continuous Integration/Continuous Deployment) environments.
Tracked as CVE-2023-7028, the security flaw is due to an improper access control weakness that can allow remote unauthenticated threat actors to send password reset emails to email accounts under their control to change the password and hijack targeted accounts without user interaction.
Although attackers can't exploit this vulnerability to hijack accounts where two-factor authentication (2FA) is enabled, it's critical to patch systems where accounts are not protected with this additional security measure.
The CVE-2023-7028 bug impacts GitLab Community and Enterprise editions, and GitLab fixed it in 16.7.2, 16.5.6, and 16.6.4 and backported patches to versions 16.1.6, 16.2.9, and 16.3.7.
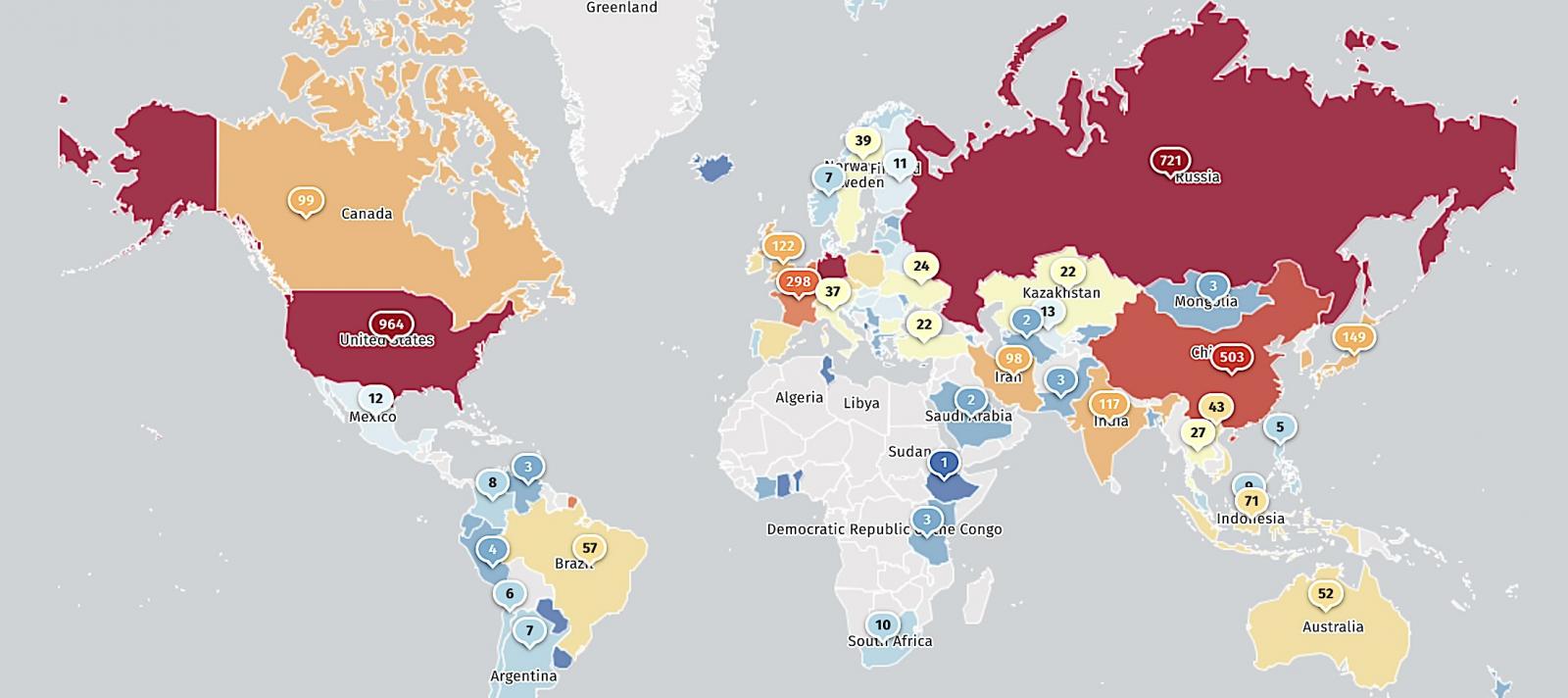
While threat monitoring service Shadowserver found 5,379 vulnerable GitLab instances exposed online in January (the week security patches were released), less than half (2,394) are still reachable at the moment.
CISA added CVE-2023-7028 to its Known Exploited Vulnerabilities Catalog on Wednesday, confirming it's now actively exploited in attacks and ordering U.S. federal agencies to secure their systems within three weeks by May 22.
The U.S. cybersecurity agency hasn't shared any information regarding ongoing attacks exploiting this maximum severity GitLab security bug, but it did confirm it has no evidence that it's being used in ransomware attacks.
"These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise," CISA said today.
Although the agency's KEV catalog primarily targets federal agencies, private organizations using the GitLab DevOps platform should also prioritize patching this vulnerability to prevent attacks.
Those who haven't already patched may have been compromised already, so they should follow GitLab's incident response guide and check for signs of compromise as soon as possible.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now