
A new version of a banking trojan known as Mekotio is being deployed in the wild, with malware analysts reporting that it's using a new, stealthier infection flow.
The last notable activity of Mekotio dates back to the summer of 2020 when the trojan's operators deployed it in a campaign targeting Latin American countries.
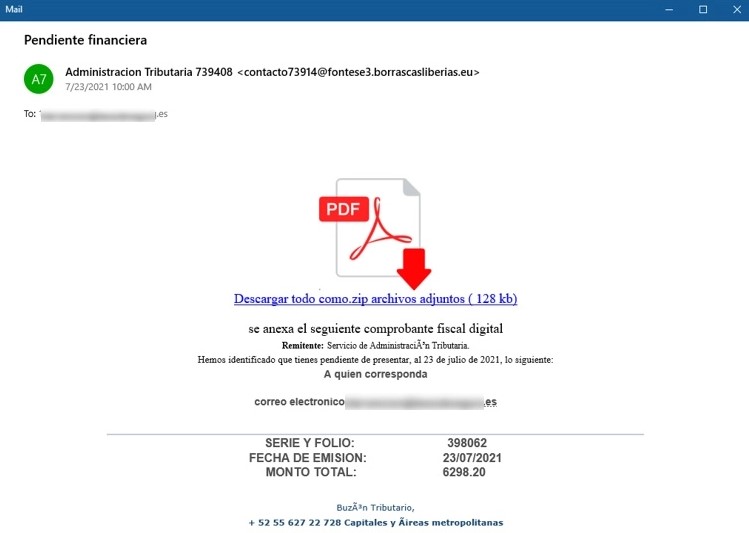
The targeting scope appears to be the same in recent attacks, with Spanish being the language of choice for the phishing emails that start the infection chain.
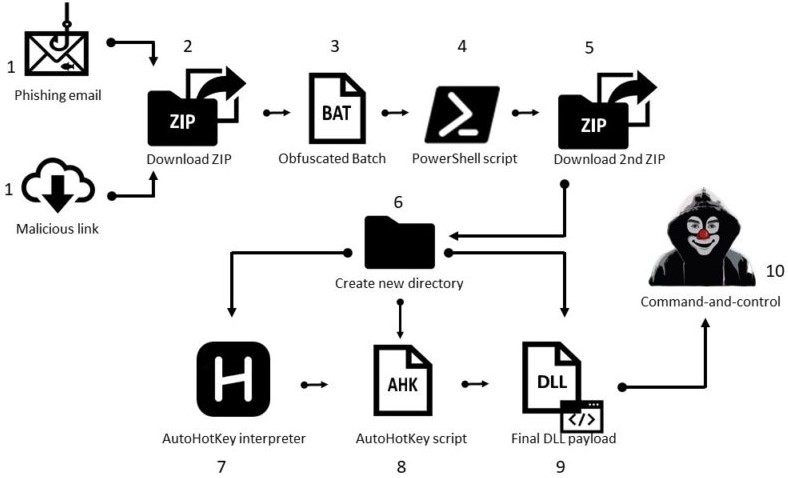
A new attack flow
The infection begins with a phishing email bundling a ZIP attachment containing an obfuscated batch script that fetches and executes a PowerShell script.
Once the PowerShell script gets launched, it will download a second ZIP archive after some basic location and anti-analysis checks.
If the checks confirm the victim is in Latin America and the malware isn't running on a virtual machine, the second ZIP, which contains the Mekotio payload in DLL form, is extracted.
Source: CheckPoint
Multi-step attack flows like the one above may appear unnecessarily complicated, but they're needed to evade detection and successfully deploy the final payload.
One of the advantages of modular attacks is the added ability to make subtle changes that render previous detection methods useless.
This is precisely the case in Mekotio's development, as the trojan's code has largely remained unchanged, with its authors mostly tweaking things instead of adding new capabilities.
Source: CheckPoint
Same old code in new wrapping
The three novel elements that make the latest Mekotio version harder to detect are the following:
- A stealthier batch file with at least two layers of obfuscation
- New file-less PowerShell script that runs directly in memory
- Use of Themida v3 for packing the final DLL payload
CheckPoint reports seeing approximately 100 attacks in the past three months deploying cipher substitution techniques, which albeit simple, help Mekotio go undetected by most AV products.
The second layer of obfuscation is slicing the PowerShell commands into parts saved in different environment variables and then concatenating the values during execution.

Source: CheckPoint
The trojan's primary goal remains to steal people's e-banking credentials and online account passwords.
Some past Mekotio variants could also hijack cryptocurrency payments and direct them to actor-controlled wallets, but recent versions have removed this functionality.
CheckPoint says the new campaign was launched right after the Spanish Civil Guard arrested 16 people in Mexico, linked with local Mekotio distribution.
However, the core Mekotio crew appears to be based in Brazil, and it's assumed that they are Mekotio's creators who are now selling it to other cybercriminals.
ESET characterized this particular trojan as "chaotic" last year due to the concurrent development that resulted in the simultaneous circulation of different variants.
That activity has now waned, and the most recent campaign uses the variant analyzed by CheckPoint.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now