
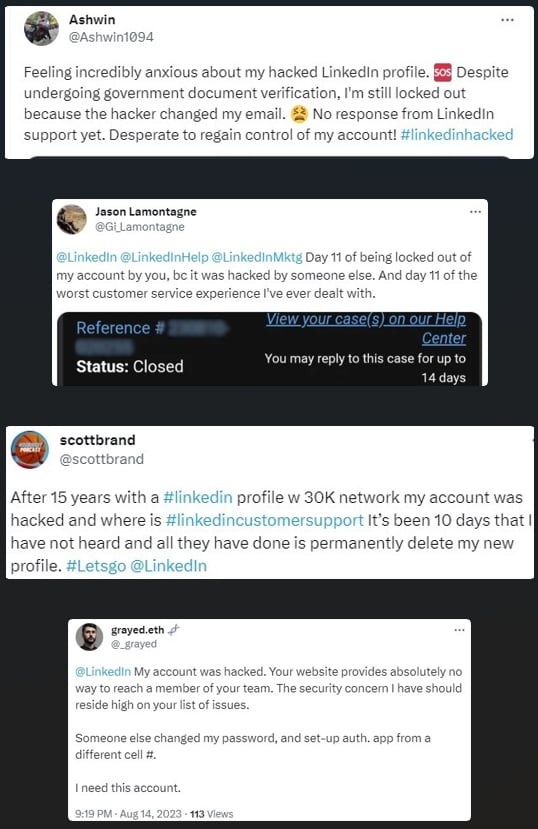
LinkedIn is being targeted in a wave of account hacks resulting in many accounts being locked out for security reasons or ultimately hijacked by attackers.
As reported today by Cyberint, many LinkedIn users have been complaining about the account takeovers or lockouts and an inability to resolve the problems through LinkedIn support.
"Some have even been pressured into paying a ransom to regain control or faced with the permanent deletion of their accounts," reports Cyberint's researcher Coral Tayar.
"While LinkedIn has not yet issued an official announcement, it appears that their support response time has lengthened, with reports of a high volume of support requests."
Source: BleepingComputer
From complaints seen by BleepingComputer on Reddit, Twitter, and the Microsoft forums, LinkedIn support has not been helpful in recovering the breached accounts, with users just getting frustrated by the lack of response.
"My account was hacked 6 days ago. Email was changed in the middle of the night and I had no ability to confirm the change or prevent it," wrote an affected user in Reddit thread about the hacks.
"No response from them anywhere. It's pathetic. I tried reporting my hacked account, going through identity verification, and even DMing them on @linkedinhelp on twitter. No responses anywhere. What a joke of a company.."
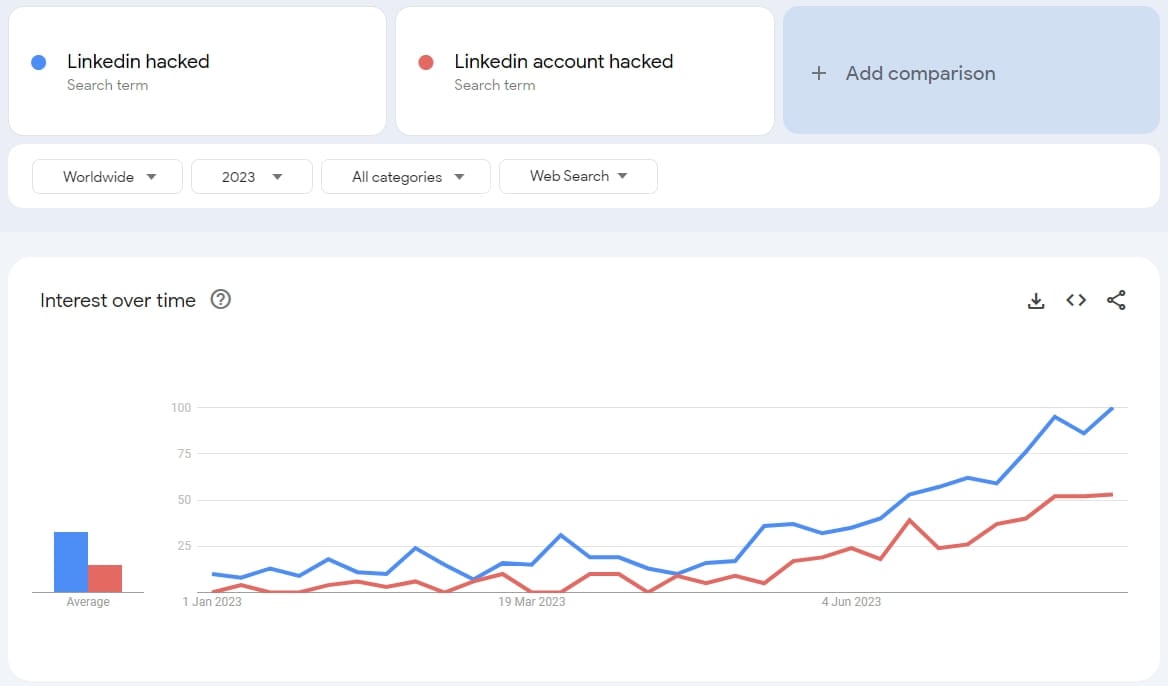
Cyberint says there are also signs of a breakout reflected in Google Trends, where search terms about LinkedIn account hack or recovery record an increase of 5,000% over the past few months.
Source: BleepingComputer
The attackers appear to be using leaked credentials or brute-forcing to attempt to take control of a large number of LinkedIn accounts.
For accounts that are appropriately protected by strong passwords and/or two-factor authentication, the multiple takeover attempts resulted in a temporary account lock imposed by the platform as a protection measure.
Owners of these accounts are then prompted to verify ownership by providing additional information and also update their passwords before they're allowed to sign in again.
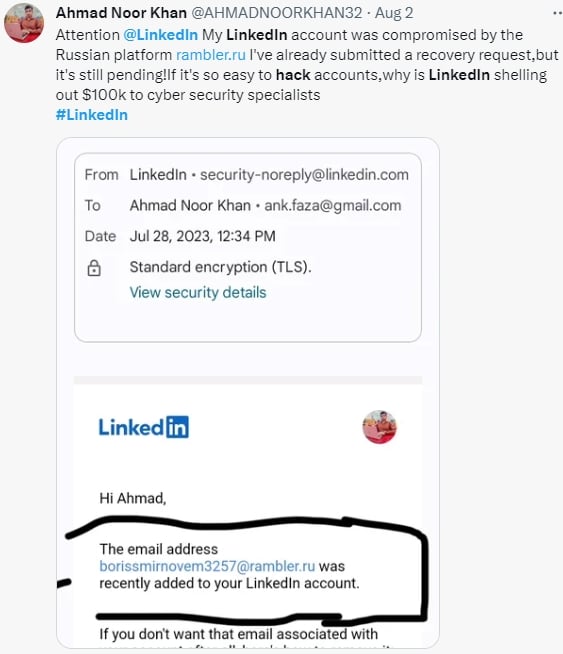
When the hackers successfully take over poorly protected LinkedIn accounts, they quickly swap the associated email address with one from the "rambler.ru" service.
After that, the hijackers change the account password, preventing the original holders from accessing their accounts. Many of the users also reported that the hackers turned on 2FA after hijacking the account, making the account recovery process even more difficult.
In some cases observed by Cyberint, the attackers demanded a small ransom to give the accounts back to the original owners or outright deleted the accounts without asking for anything.
LinkedIn accounts can be valuable for social engineering, phishing, and job offer scams that sometimes lead to multi-million dollar cyber-heists.
Especially after LinkedIn introduced features that combat fake profiles and inauthentic behavior on the platform, hijacking existing accounts has become much more pragmatic for hackers.
If you maintain a LinkedIn account, now would be a good time to review the security measures you've activated, enable 2FA, and switch to a unique and long password.
BleepingComputer has contacted LinkedIn requesting a comment on the reported situation, but we have not received a response by publication time.


Comments
GT500 - 8 months ago
How about we refer to Twitter as "eX-Twitter" from now on?
johnlsenchak - 8 months ago
Why aren't more LinkedIn users using 2FA to secure their account. It's their own fault if they lose access because they don't use the proper security measures .
I just checked , I can still access my account which has 2FA enabled
Read the "Cyberint " report above
wright_is - 8 months ago
Same here. If the account is important to these people, why haven't they protected them?
NarwhalSoup - 8 months ago
Since other commenters are blaming victims for having insecure accounts, I'll share my take:
A couple months ago, I found out my LinkedIn account was hidden and completely unsearchable on the app and search engines. When I logged in, I saw that my account was blocked for suspicious activity. I use a password manager, so I checked whether I was using some old password that might be associated with a leak. I was already using a long random password unique to LinkedIn, so it wasn't that. I had 2FA enabled as well. Weird.
The most frustrating part is that unlocking your account requires you to submit a help ticket with photos of your driver's license to verify your identity. The process takes about two weeks and you can't even check on the status after you submit the ticket because, of course, viewing status of your support tickets requires logging in but your account is locked.
It's a mess and I'm not surprised to see that it's on the rise after my experience. I understand the kneejerk reaction to blame the users but my guess is someone's brute forcing accounts in a way that can lock up any unverified account. I wouldn't be surprised if the fact that effectively DDOSing LinkedIn's support system is an added benefit to the attackers.
smylekiller - 8 months ago
I went through the same thing. Right after I published a post meant to draw attention to the credential harvesting confidence scam happening in plain sight.
smylekiller - 8 months ago
It’s actually LinkedIn Help that’s spear phishing everyone’s credentials. LinkedIn Help is a fraudulent consumer account pretending to be a Tier 1 “social support” for end-users who have simple break/fix issues, like account lockouts.
johnlsenchak - 8 months ago
Basically it's like Facebook/Meta , you get absolutely no help from a online form because it's run by a A.I. bot
Pmac66 - 8 months ago
My complaint is that I pay for and use LinkedIn Premium, therefore the bill me every month, have done so for many years, so why are they, apparently randomly, locking out paying customers? I did their ID verification anyway 3 or 4 times with absolutely no engagement from LI, no real way to speak with or communicate with LI.
djtaube - 8 months ago
Mid-to-late June, I received two emails notifying me of the following:
Your request to activate Remember me on your LinkedIn, Android in Calcutta, West Bengal, India was not successful. This is because you have 2-Factor Authentication enabled on your account for additional security. Learn more.
This was alarming as I (1) do not have an android device, (2) never have been to India or used any VPN, proxy, or other that would route through it, and (3) hand a very long and complex password that is nearly an impossibility to guess and is unique to LinkedIn.
I had no success raising this with support. Could not locate where you could see sign in activity (like Microsoft has for M365). Could not find other examples. Luckily, I had 2FA.
My suspicion with the reference to the “remember me” setting is that there is session hijacking or vuln exploit not necessarily requiring password stuffing or brute forcing.