The FBI announced today the disruption of the Qakbot botnet in an international law enforcement operation that not only seized infrastructure but also uninstalled the malware from infected devices.
During this past weekend’s law enforcement operation, Operation Duck Hunt, the FBI redirected the botnet’s network communications to servers under its control, allowing agents to identify approximately 700,000 infected devices (200,000 located in the U.S.).
After they took control of the botnet, the FBI devised a method to uninstall the malware from the victims’ computers, effectively dismantling the botnet’s infrastructure, from the victims’ PCs to the malware operators’ own computers.
What is Qakbot?
Before we learn how the FBI uninstalled Qakbot from computers, it is essential to understand how the malware was distributed, what malicious behavior it performed, and who utilized it.
Qakbot, aka Qbot and Pinkslipbot, started as a banking trojan in 2008, used to steal banking credentials, website cookies, and credit cards to conduct financial fraud.
However, over time, the malware evolved into a malware delivery service utilized by other threat actors to gain initial access to networks for conducting ransomware attacks, data theft, and other malicious cyber activities.
Qakbot is distributed through phishing campaigns that utilize a variety of lures, including reply-chain email attacks, which is when threat actors use a stolen email thread and then reply to it with their own message and an attached malicious document.
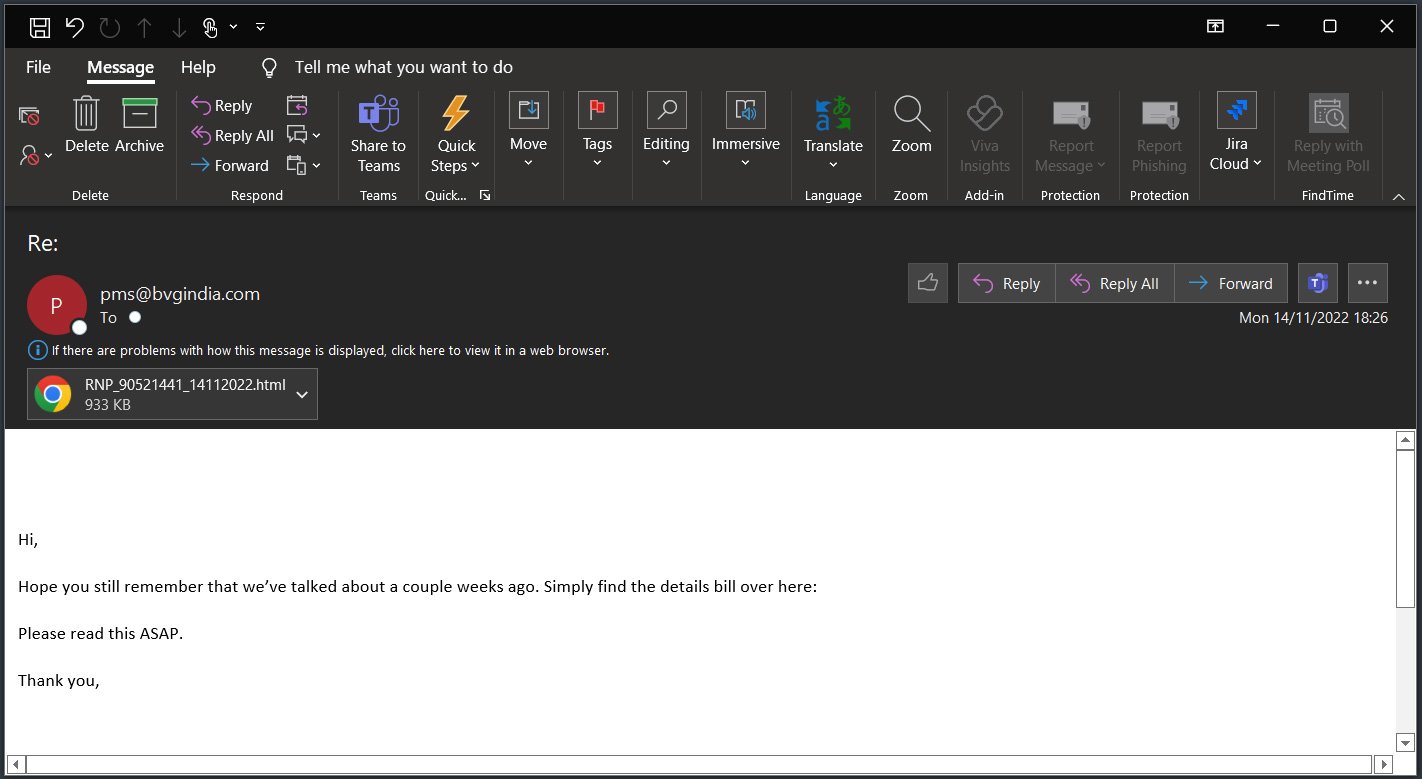
Source: BleepingComputer
These emails typically include malicious documents as attachments or links to download malicious files that install the Qakbot malware on a user’s device.
These documents change between phishing campaigns and range from Word or Excel documents with malicious macros, OneNote files with embedded files, to ISO attachments with executables and Windows shortcuts. Some of them are also designed to exploit zero-day vulnerabilities in Windows.
Regardless of how the malware is distributed, once Qakbot is installed on a computer, it will be injected into the memory of a legitimate Windows processes, such as wermgr.exe or AtBroker.exe, to attempt to evade detection by security software.
For example, the image below depicts the Qbot malware injected into the memory of the legitimate wermgr.exe process.
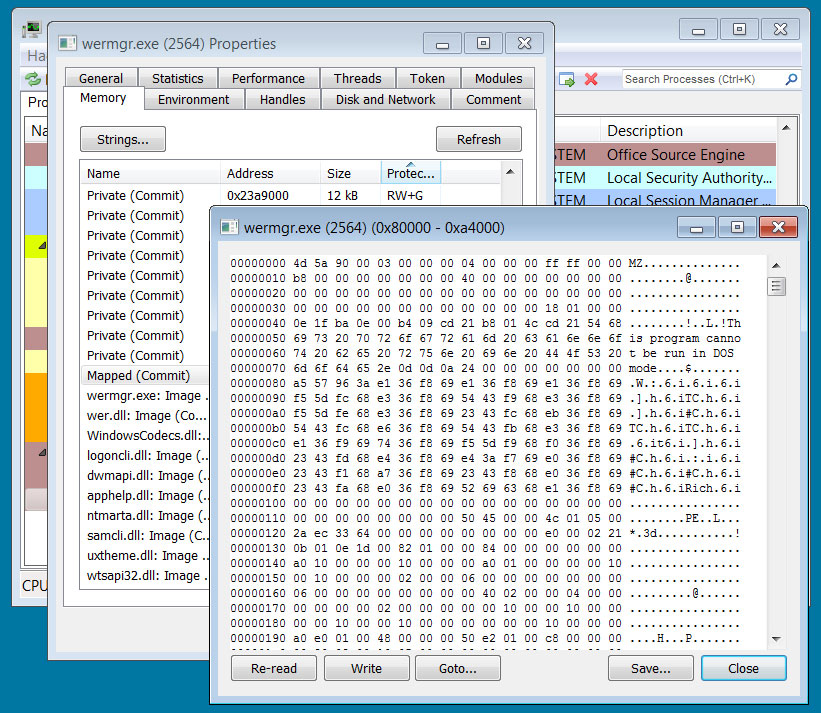
Source: BleepingComputer
Once the malware is launched on a device, it will scan for information to steal, including a victim's emails, for use in future phishing email campaigns.
However, the Qakbot operators also partnered with other threat actors to facilitate cybercrime, such as providing ransomware gangs with initial access to corporate networks.
In the past, Qakbot has partnered with multiple ransomware operations, including Conti, ProLock, Egregor, REvil, RansomExx, MegaCortex, and, most recently, Black Basta and BlackCat/ALPHV.
The FBI says that between October 2021 and April 2023, the Qakbot operators earned approximately $58 million from ransomware payments.
How the FBI uninstalled Qakbot
As part of today's announcement, the FBI states that they were able to dismantle the botnet by seizing the attacker's server infrastructure and creating a special removal tool that uninstalled the Qakbot malware from infected devices.
According to an application for seizure warrant released by the Department of Justice, the FBI was able to gain access to the Qakbot admin computers, which helped law enforcement map out the server infrastructure used in the botnet's operation.
Based on their investigation, the FBI determined that the Qakbot botnet utilized Tier-1, Tier-2, and Tier-3 command and control servers, which are used to issue commands to execute, install malware updates, and download additional partner payloads to devices.
Tier-1 servers are infected devices with a "supernode" module installed that act as part of the command and control infrastructure of the botnet, with some of the victims located in the USA. Tier-2 servers are also command and control servers, but the Qakbot operators operate them, usually from rented servers outside the USA.
The FBI says that both the Tier-1 and Tier-2 servers are used to relay encrypted communication with the Tier-3 servers.
These Tier-3 servers act as the central command and control servers for issuing new commands to execute, new malicious software modules to download, and malware to install from the botnet's partners, such as ransomware gangs.
Every 1 to 4 minutes, the Qakbot malware on infected devices would communicate with a built-in list of Tier-1 servers to establish encrypted communication with a Tier-3 server and receive commands to execute or new payloads to install
However, after the FBI infiltrated the Qakbot's infrastructure and administrator's devices, they accessed the encryption keys used to communicate with these servers.
Using these keys, the FBI used an infected device under their control to contact each Tier-1 server and have it replace the already installed Qakbot "supernode" module with one created by law enforcement.
This new FBI-controlled supernode module used different encryption keys not known to the Qakbot operators, effectively locking them out of their own command and control infrastructure as they no longer had any way to communicate with the Tier-1 servers.
The FBI then created a custom Windows DLL (or Qakbot module) [VirusTotal] that acted as a removal tool and was pushed to infected devices from the now-hijacked Tier-1 servers.
Based on an analysis of the FBI module by SecureWorks, this custom DLL file issued the QPCMD_BOT_SHUTDOWN command to the Qakbot malware running on infected devices, which causes the malware process to stop running.
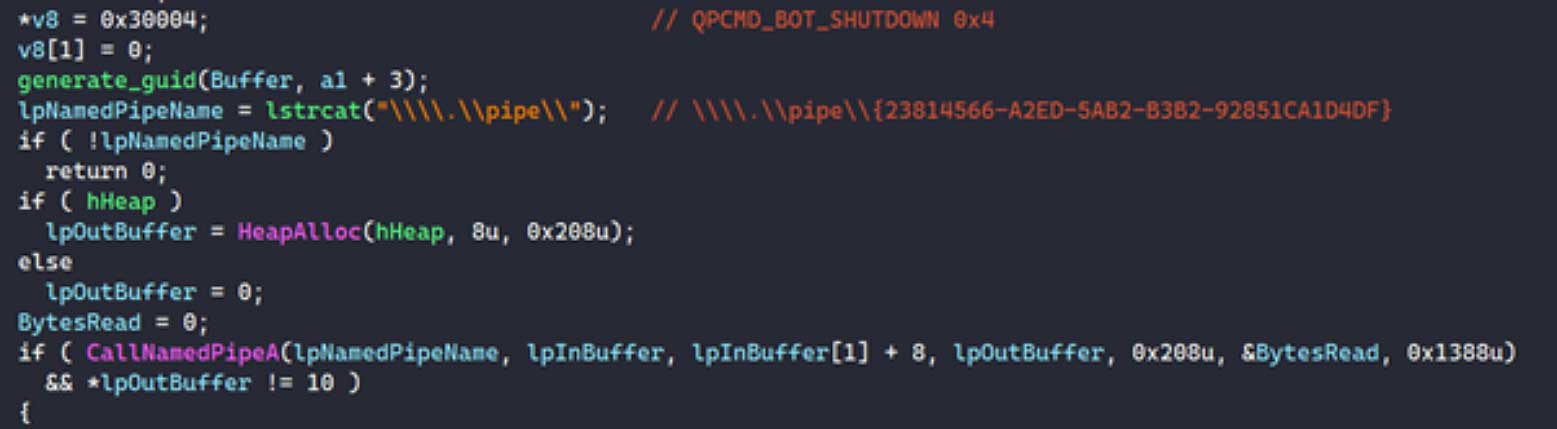
Source: SecureWorks
SecureWorks says they first saw this custom module pushed down to infected devices on August 25th at 7:27 PM ET.
"At 00:27 BST on August 25, CTU researchers detected the Qakbot botnet distributing shellcode to infected devices," explains SecureWorks.
"The shellcode unpacks a custom DLL (dynamic link library) executable that contains code that can cleanly terminate the running Qakbot process on the host."
The FBI says that this Qakbot removal tool was authorized by a judge with a very limited scope of only removing the malware from infected devices.
Furthermore, as the malware is injected into the memory of another process, the removal tool does not need to read or write anything to the hard drive to shut down the process.
"Qakbot establishes persistence on a host when it detects a user initiating a system shutdown. Using the named pipe to terminate the Qakbot process bypasses persistence," continues SecureWorks.
"As a result, Qakbot will not run if the host is restarted."
However, as pointed out in the comments below, QakBot may also create a scheduled task to launch the malware on startup, potentially loading the malware into memory again.
This would cause a repeated cycle of QakBot launches and uninstalls as it downloads the FBI's module, as SecureWorks explained to BleepingComputer below.
"The tool deployed by the FBI does not make any attempt to directly remove the Qakbot files from disk or to remove any existing persistence mechanism(s), instead relying on Qakbot's native functionality to remove itself when instructed to shutdown. After more rigorous testing Secureworks has been unable to recreate a scenario where Qakbot loads the FBI's tool and the infection remains active or returns after reboot, regardless of the type of persistence employed. We performed this testing in a variety of environments with version of Qakbot distributed from 2020 through the recent takedown action. The FBI's continued control of Qakbot's infrastructure is important to ensuring remaining Qakbot infections are captured and terminated. Despite the tool's effectiveness at terminating Qakbot, impacted systems may contain artifacts of prior infection such as the presence of the Qakbot installation directory within %APPDATA%, inoperational registry persistence keys, and files used during initial infection (such as downloaded email attachments)." - SecureWorks.
At this time, the FBI is unsure of the total number of devices that have been cleaned in this manner, but as the process started over the weekend, they expect that further devices will be cleaned as they connect back to the hijacked Qakbot infrastructure.
The FBI also shared a database containing credentials stolen by the Qakbot malware with Have I Been Pwned and the Dutch National Police.
As no notifications will be displayed on infected devices when the malware is removed, you can use these services to see if your credentials were stolen, indicating that you may have at one point been infected with the Qakbot malware.
This is not the first time the FBI used a court-approved seizure warrant to remove malware from infected devices.
The FBI previously received court approval to remove the Russian Snake data theft malware and the Emotet malware from infected devices, as well as web shells on Microsoft Exchange servers deployed in ProxyLogon attacks.
While this is definitely a win for law enforcement, it may not be the end of the Qakbot operation as no arrests were made.
Therefore, we will likely see the Qakbot operators begin to rebuild their infrastructure over the next few months through phishing campaigns or by purchasing installations through other botnets.
Update 8/30/23: Added information about persistence
Update 9/3/23: Added updated Secureworks statement about FBI tool.


Comments
roedldoedl - 7 months ago
"the malware only operates from memory"
Does that mean that the malware relies on victims not rebooting?
Lawrence Abrams - 7 months ago
I updated the article to make it a bit clearer.
There are two persistence methods, a Run key created when the malware detects the computer shutting down, and a scheduled task.
The FBI module bypasses the Run key creation. However, it's unclear about the scheduled task. I have contacted SecureWorks with questions on that.
peterracine - 7 months ago
No I believe that qakbot does contain a persistence mechanism as described in this article below by splunk . It either uses the registry run key or creates a scheduled task to restart if the infected computer reboots.
https://www.splunk.com/en_us/blog/security/from-macros-to-no-macros-continuous-malware-improvements-by-qakbot.html
h_b_s - 7 months ago
That's another feather for law enforcement... But the unfortunate fact remains, without competent IT support, those 700,000 devices, of which 200k are in the US, will just be reinfected by another gang because the FBI can't go in and update the infrastructure nor force the organizations to at least properly isolate the ones that can't be updated either from EOL or antiquated regulatory regimes.
Until it becomes possible for LEO to also issue directives to ISPs to block problem organizations so they finally wake up to the fact they have a problem and that problem won't be tolerated by others any longer, organizations with repeated malware infections from incompetent management or negligence, from the wider Internet this is an unsolvable problem.