
Over 15 free VPN apps on Google Play were found using a malicious software development kit that turned Android devices into unwitting residential proxies, likely used for cybercrime and shopping bots.
Residential proxies are devices that route internet traffic through devices located in homes for other remote users, making the traffic appear legitimate and less likely to be blocked.
While they have legitimate uses for market research, ad verification, and SEO, many cybercriminals use them to conceal malicious activities, including ad fraud, spamming, phishing, credential stuffing, and password spraying.
Users may voluntarily register on proxy services to get monetary or other rewards in return, but some of these proxy services employ unethical and shady means to install their proxying tools on people's devices secretly.
When secretly installed, victims will have their internet bandwidth hijacked without their knowledge and risk legal trouble due to appearing as the source of malicious activity.
Proxying Android VPN apps
A report published today by HUMAN's Satori threat intelligence team lists 28 applications on Google Play that secretly turned Android devices into proxy servers. Of these 28 applications, 17 were passed off as free VPN software.
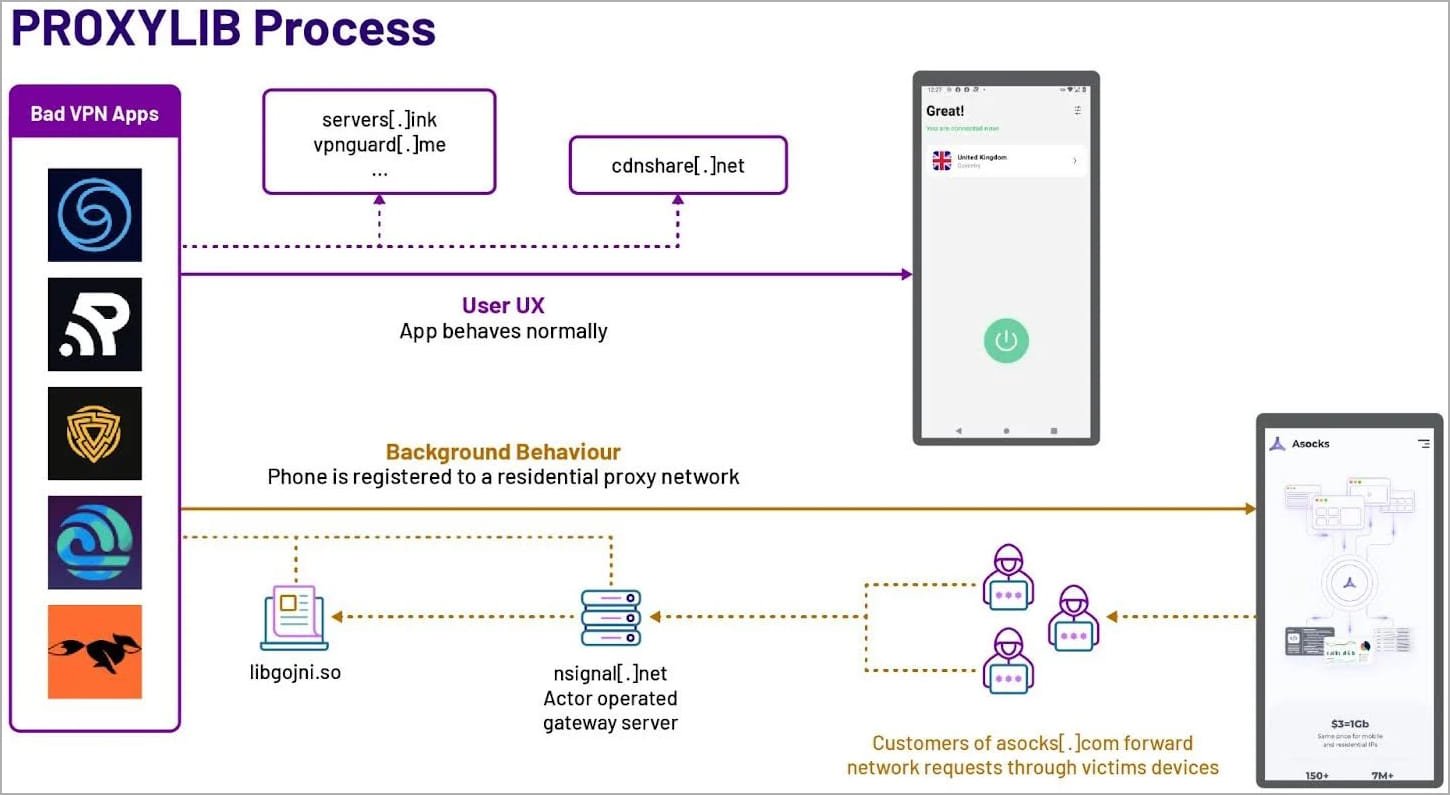
Satori analysts report that the offending apps were all using a software development kit (SDK) by LumiApps that contained "Proxylib," a Golang library to perform the proxying.
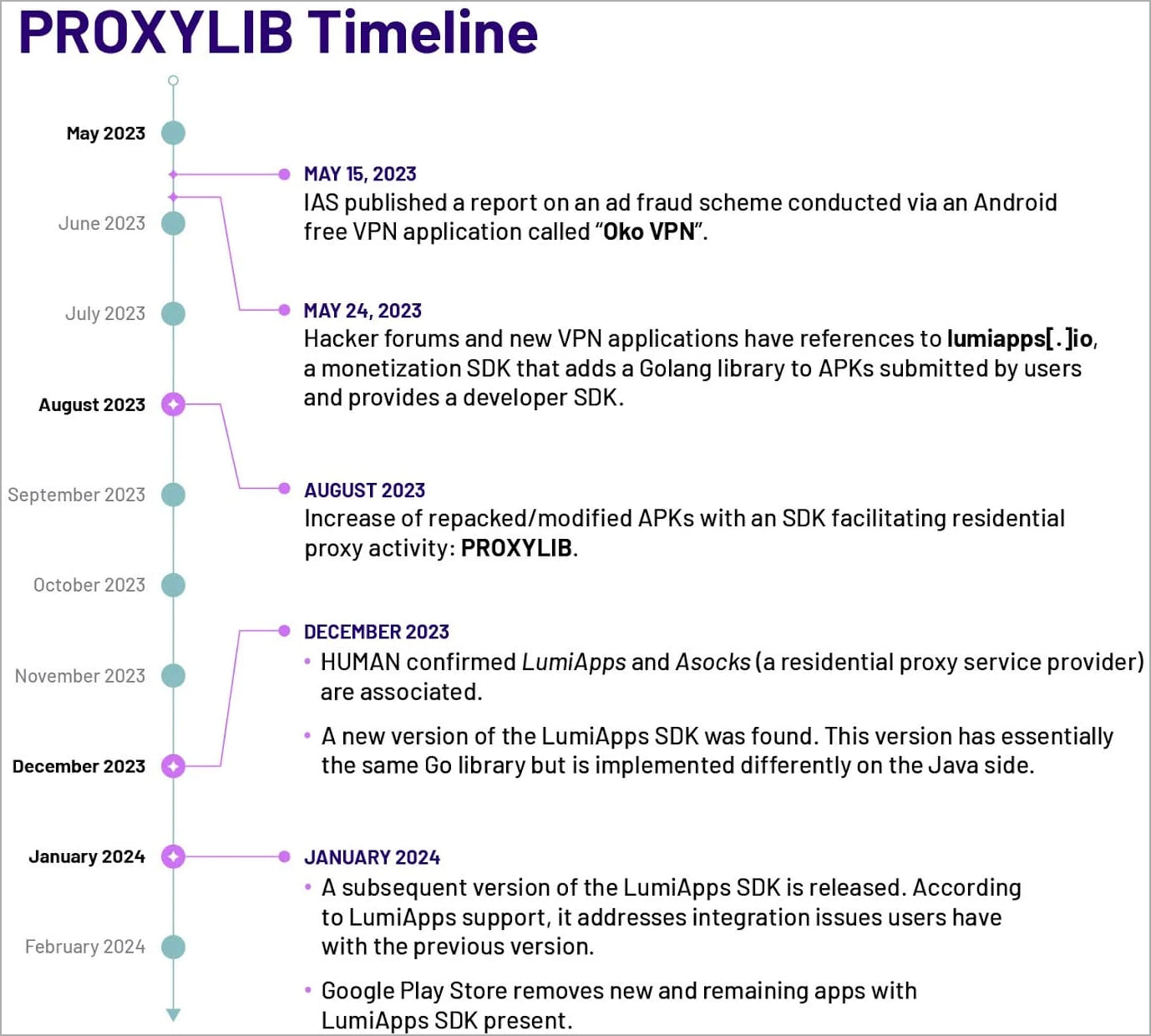
HUMAN discovered the first PROXYLIB carrier app in May 2023, a free Android VPN app named "Oko VPN." The researchers later found the same library used by the LumiApps Android app monetization service.
"In late May 2023, Satori researchers observed activity on hacker forums and new VPN applications referencing a monetization SDK, lumiapps[.]io," explains the Satori report.
"Upon further investigation, the team determined that this SDK has exactly the same functionality and uses the same server infrastructure as the malicious applications analyzed as part of the investigation into the earlier version of PROXYLIB. "
A subsequent investigation revealed a set of 28 apps that utilized the ProxyLib library to convert Android devices into proxies, which are listed below:
- Lite VPN
- Anims Keyboard
- Blaze Stride
- Byte Blade VPN
- Android 12 Launcher (by CaptainDroid)
- Android 13 Launcher (by CaptainDroid)
- Android 14 Launcher (by CaptainDroid)
- CaptainDroid Feeds
- Free Old Classic Movies (by CaptainDroid)
- Phone Comparison (by CaptainDroid)
- Fast Fly VPN
- Fast Fox VPN
- Fast Line VPN
- Funny Char Ging Animation
- Limo Edges
- Oko VPN
- Phone App Launcher
- Quick Flow VPN
- Sample VPN
- Secure Thunder
- Shine Secure
- Speed Surf
- Swift Shield VPN
- Turbo Track VPN
- Turbo Tunnel VPN
- Yellow Flash VPN
- VPN Ultra
- Run VPN
LumiApps is an Android app monetization platform that states its SDK will use a device's IP address to load webpages in the background and send the retrieved data to companies.
"Lumiapps helps companies gather information that is publicly available on the internet. It uses the user's IP address to load several web pages in the background from well-known websites," reads the LumiApps website.
"This is done in a way that never interrupts the user and fully complies with GDPR/CCPA. The web pages are then sent to companies, who use them to improve their databases, offering better products, services, and pricing."
Source: BleepingComputer
However, it is unclear if the free app developers knew that the SDK was converting their users' devices into proxy servers that could be used for unwanted activities.
HUMAN believes the malicious apps are linked to the Russian residential proxy service provider 'Asocks' after observing connections made to the proxy provider's website. The Asocks service is commonly promoted to cybercriminals on hacking forums.
Source: HUMAN
In January 2024, LumiApps released the second major version of its SDK along with Proxylib v2. According to the firm, this addressed "integration issues," and it now supports Java, Kotlin, and Unity projects.
Following HUMAN's report, Google removed any new and remaining apps using the LumiApps SDK from the Play Store in February 2024 and updated Google Play Protect to detect the LumiApp libraries used in the apps.
Source: HUMAN
Meanwhile, many apps listed above are now available again on the Google Play store, presumably after their developers removed the offending SDK. They were sometimes published from different developer accounts, potentially indicating previous account bans.
Source: BleepingComputer
BleepingComputer has reached out to Google for a comment on the status of the currently available apps using the same names and whether they are now safe, but we have yet to hear back.
If you have used one of the listed apps, updating to the newest version that does not use the particular SDK will stop the proxying activity. However, out of an abundance of caution, it may be safer to remove them altogether.
If the app was removed from Google Play and no safe version exists, you are recommended to uninstall it. Play Protect should also warn users in that case.
Finally, it is likely safer to use paid VPN apps instead of free services as many products in the latter category are more eager to implement indirect monetization systems, including data collection/selling, advertising, and enrollment in proxy services.
Update 3/27 - A Google spokesperson sent BleepingComputer the following comment:
Google Play Protect automatically protects users by disabling these identified apps. Once the apps are disabled, they cannot run on the device or do any harm on the device.
Google Play Protect will also provide a warning and ask users if they would like to fully uninstall.
The spokesperson also confirmed that all 28 of the malicious apps reported by HUMAN have now been removed from Google Play.
Hence, all the apps with the same or similar names as those mentioned in the list above are completely safe to use.
.jpg)

Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now